
If you prepare and file taxes electronically, federal law has specific things to say about how your technology is set up.
Not general cybersecurity advice. Specific, documented, enforceable requirements under IRS Publication 4557 and the Federal Trade Commission’s Safeguards Rule. And if your IT infrastructure does not meet them, the consequences go well beyond a cautionary letter.
Tax and accounting firms are legally classified as financial institutions under the Gramm-Leach-Bliley Act. That classification means the FTC holds your firm to the same data protection standards as banks and credit unions.
It also means the IRS expects documented, auditable evidence of your security controls, not just good intentions. For enrolled agents and professional tax preparers, non-compliance is a PTIN issue. Lose your Preparer Tax Identification Number, and you cannot legally file taxes for clients.
If you are an enrolled agent, independent tax preparer, or small CPA firm owner, these are the five IT systems the IRS and FTC now expect you to have in 2026.
Key Takeaways
- A Written Information Security Plan (WISP) is a federal legal requirement for all tax preparers who file electronically. It is not a best practice or a recommendation. It is a legal mandate.
- IRS Publication 4557 requires multi-factor authentication (MFA), AES-256 encrypted data storage, and a documented incident response plan for every firm that handles electronic returns.
- The FTC Safeguards Rule classifies accounting and tax firms as financial institutions and requires a formal, written data protection program that is reviewed and updated annually.
- Automated encrypted backups, managed endpoint protection, and accounting-specialist IT support are each individually required to meet the combined obligations of IRS and FTC mandates in 2026.
What are the 5 IT Essentials Accounting Firms Must Have to Stay IRS-Compliant?
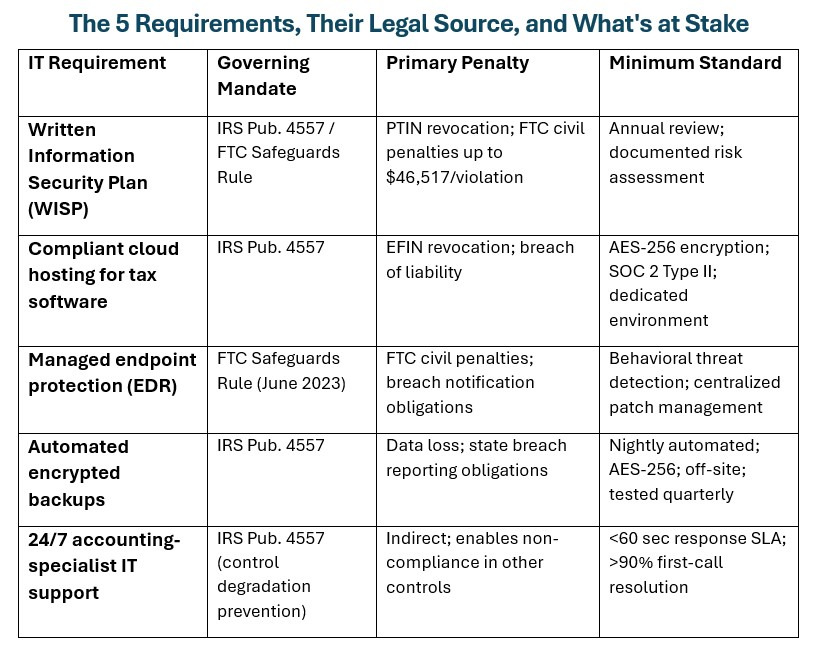
The five requirements below are drawn directly from IRS Publication 4557, IRS Publication 5708, and the FTC Safeguards Rule.
They are not a prioritized wish list or a vendor’s interpretation of best practices. They are the controls the IRS and FTC have documented as mandatory for firms that handle electronic returns and hold sensitive taxpayer data. Each one addresses a specific regulatory obligation, and together they form the complete IT compliance baseline every enrolled agent and CPA firm operating in 2026 is expected to meet.
The IRS refers to its core technical requirements as the “Security Six”: antivirus, firewalls, MFA, drive encryption, tested backups, and secure remote access. The five essentials below are the operational systems a firm must have to actually implement and sustain those controls in a production environment.
1. A Written Information Security Plan (WISP)
A Written Information Security Plan is a formal, documented policy that describes how your firm identifies, manages, and protects the sensitive taxpayer data it holds. It is the foundational compliance document that every other IT control feeds into.
Without it, even a firm with solid technical defenses has no documented evidence that those defenses exist, which is what regulators actually audit.
The IRS Security Summit, a coalition of the IRS, state tax agencies, and the broader tax industry, has made the WISP a centerpiece of its annual data security guidance for years. IRS Publication 4557 names it as a required safeguard for all professional preparers who file electronically. IRS Publication 5708 goes further and provides a step-by-step WISP template that firms can use as a baseline.
These are not ambiguous recommendations. They are the IRS’s direct guidance to tax professionals on what their security documentation must contain.
The document itself must cover, at minimum: a formal risk assessment, administrative safeguards governing staff access and training, technical controls including MFA and encryption, physical access restrictions, a written incident response procedure, and a schedule for annual review.
What Happens If You Don’t Have a WISP?
When you renew your PTIN each year, the renewal attestation asks you to confirm a WISP is in place.
A missing or inadequate WISP is not a gray area in that process. The IRS can revoke PTIN status for demonstrated non-compliance with its data security requirements, ending your ability to file professionally. The FTC can impose civil penalties of up to $46,517 per violation under the Gramm-Leach-Bliley Act for failure to maintain a written information security program, and each affected client record can constitute a separate violation.
And in the event of a breach, the absence of a documented WISP creates direct exposure with cyber insurance carriers who increasingly require proof of written security controls before honoring claims.
According to IBM’s Cost of a Data Breach Report 2024, the average cost of a data breach reached $4.88 million globally.
Firms that need a fully customized, audit-ready WISP aligned to their specific software stack and staff size can now take the help of specialized WISP service for tax and accounting firms that delivers a compliant, IRS-aligned plan in as little as five business days.
2. Secure, IRS-Compliant Cloud Hosting for Tax Software
IRS Publication 4557 requires that all client data be stored with AES-256 encryption, accessible only to authorized personnel, and protected both at rest and in transit at all times.
Your tax software is the primary container for that data. Drake Tax, Lacerte, ProSeries, UltraTax CS, and QuickBooks Desktop collectively hold Social Security numbers, Employer Identification Numbers, prior-year return data, and complete financial records for every client you serve. Where and how that software runs is a compliance question before it is an operational one.
Compliance-grade hosting for tax and accounting software means several specific things:
- AES-256 encryption at rest and in transit.
- Multi-factor authentication enforced on every login without exception.
- SOC 2 Type II certified infrastructure that has been independently audited.
- A dedicated server environment where your firm’s data is fully isolated from other tenants.
That last requirement deserves more attention than it typically receives. In a shared cloud hosting environment, one tenant’s misconfiguration or vulnerability can create risk for neighboring accounts. During tax season, when servers handle the highest volume of sensitive returns in the tightest timeframe, shared infrastructure is a compliance and security liability that Publication 4557 requires you to address.
There is a meaningful operational benefit alongside the regulatory one. When tax software runs on certified, dedicated cloud infrastructure, your team can access Drake, ProSeries, Lacerte, or QuickBooks from any device and any operating system without configuring a VPN or maintaining aging local hardware.
A dedicated server environment where your firm’s data is fully isolated from other tenants also delivers the most tangible operational benefit: reliability during the period it matters most. Shared cloud hosting environments experience performance degradation under peak tax-season load precisely because server resources are spread across hundreds of firms simultaneously.
Dedicated infrastructure removes that variable entirely. Providers like Verito, which has maintained a 100% uptime record since 2016 serving tax and accounting firms exclusively, demonstrate what that commitment looks like in practice.
For enrolled agents and preparers relying on Drake, ProSeries, or Lacerte to meet filing deadlines, access continuity is not a convenience feature. In compliance terms, downtime is a risk. In operational terms, it is lost revenue. A dedicated hosting environment addresses both.
3. Managed Endpoint Protection
Endpoint protection covers every device that connects to your firm’s data or network: workstations, laptops, tablets, and mobile phones used for work.
The FTC Safeguards Rule, whose updated provisions took full effect in June 2023, explicitly requires covered firms to encrypt data in transit, enforce MFA, maintain a documented patch management program, and monitor system activity for unauthorized access. These four requirements cannot be reliably met by traditional antivirus software, regardless of how recently it was updated.
The practical distinction between legacy antivirus and next-generation Endpoint Detection and Response (EDR) matters here. Traditional antivirus identifies threats by comparing files against a database of known malware signatures. EDR uses behavioral analysis to detect threats that have never been cataloged before, including the lateral movement patterns that consistently precede ransomware deployment.
According to Verizon’s 2024 Data Breach Investigations Report, 68% of breaches involved a human element such as phishing or credential theft. EDR is specifically designed to catch those entry points before they become incidents that trigger your notification obligations under state data breach laws.
Accounting and tax firms are high-value targets because of what they hold: Social Security numbers, bank account data, EINs, and years of financial history for individuals and businesses, all in a single system, typically behind lighter defenses than dedicated financial institutions.
The IRS Security Summit has documented a sustained pattern of credential phishing campaigns targeting tax professionals specifically. The technical safeguards that address those threats are not optional enrichments. In 2026, they are the regulatory floor.
Providers of managed IT services built for accounting firms typically bundle EDR, MFA enforcement, patch management, and FTC Safeguards Rule compliance documentation into a single monthly service, removing the burden of sourcing and managing each control independently.
4. Automated, Encrypted Backups
IRS Publication 4557 explicitly requires that firms maintain the ability to restore critical client data following a system failure, ransomware attack, or natural disaster.
A backup process that depends on a staff member manually exporting files to a USB drive or external hard disk does not satisfy that requirement. The IRS expects an automated, encrypted, and periodically tested backup solution.
A compliant backup strategy has four components:
- Automated nightly execution so no backup depends on human action
- AES-256 encryption at rest so the backup itself cannot be read if intercepted
- Geographically separate or cloud-based off-site storage so a single physical event cannot destroy both primary and backup data simultaneously
- A documented test restore process that confirms the backup actually works before it is needed.
That last component is the one most small firms skip entirely, and it is the one that determines whether a backup is a recovery plan or an assumption.
The tax season timing dimension is not abstract. A ransomware attack in February or early March, at the peak of filing volume, leaves a sole practitioner with no technical recovery path if backups are untested or unencrypted. The firm faces data loss, mandatory client notification under applicable state breach reporting statutes, and potential IRS reporting obligations.
Firms that run automated nightly backups and test their restore process quarterly can recover from most incidents within hours. Firms that discover their backup has not been running at the moment they need it cannot.
5. 24/7 IT Support from Specialists Who Know Tax Software
A support technician who has never opened Drake Tax cannot resolve a Drake Tax failure at 9 PM on April 14.
This is not a criticism of general IT support providers. It is a structural limitation. Tax and accounting software has specific, recurring failure modes around multi-user licensing configurations, update timing conflicts, remote desktop session behavior, and integration issues with practice management platforms like TaxDome and OfficeTools.
Resolving those problems requires hands-on familiarity with how the software actually behaves in production, not just general Windows Server knowledge.
The compliance dimension of IT support quality is often overlooked. When firms cannot get fast, first-call resolution, staff create workarounds. Shared login credentials. MFA turned-off on one workstation “just temporarily.” A client return processed on an unpatched personal laptop because the office server was down and a deadline was approaching.
These are not policy failures. They are predictable responses to inadequate support. IRS Publication 4557 requires firms to prevent exactly these kinds of control degradations, which means the quality and responsiveness of your IT support provider directly affects your compliance posture, not just your productivity.
Firms assessing specialist IT providers should ask explicitly for documented response time SLAs and first-call resolution rates, and should confirm that the provider’s technicians can name and demonstrate familiarity with the specific software the firm runs.
When evaluating services such as managed IT for accounting firms, look for response times under 60 seconds and first-call resolution rates above 90%. Those benchmarks exist, they are achievable, and they are the specific service levels that prevent tax-season workarounds before they become compliance gaps.
The Baseline is Higher Than Most Firms Realize
These five requirements represent the regulatory floor for 2026, not an advanced security posture reserved for large CPA firms.
The FTC Safeguards Rule update that took effect in June 2023 brought independent tax preparers and small accounting firms into a compliance regime that previously applied primarily to larger financial institutions. That shift has not been fully absorbed across the profession, and enforcement activity is increasing.
The practical benefit of addressing all five requirements under a single framework is that compliance documentation becomes unified. When the same provider manages your cloud environment, endpoints, backups, and support, there is no gap where one vendor assumes another has covered a requirement.
Your WISP documents controls that are actually in place, tested, and generating evidence logs. That is what IRS auditors and FTC reviewers verify when they assess whether a firm’s data security program is real or theoretical.
For enrolled agents and small CPA firms operating in 2026, the compliance floor is clear: a documented WISP, compliant cloud hosting, managed endpoint protection, tested automated backups, and specialist IT support are each individually required under IRS Publication 4557 and the FTC Safeguards Rule, not collectively optional.
The FTC Safeguards Rule update that took full effect in June 2023 extended these obligations to independent preparers with no revenue or headcount threshold. Firms that can demonstrate all five controls through documented, auditable evidence are compliant. Firms that cannot, are exposed.
Frequently Asked Questions
1. Is a WISP required for all accounting firms and enrolled agents?
Yes. Under IRS Publication 4557 and the FTC Safeguards Rule, every professional tax preparer who files electronically is legally required to have a Written Information Security Plan. PTIN renewal attestation asks preparers to confirm a WISP is in place. Firms without a current WISP face PTIN revocation risk and potential civil penalties under the Gramm-Leach-Bliley Act.
2. What does IRS Publication 4557 require from a technology standpoint?
IRS Publication 4557 requires multi-factor authentication on all accounts that access taxpayer data, AES-256 encryption for data stored and transmitted, a documented incident response plan, and a written WISP that captures these controls. It also requires ongoing monitoring for unauthorized system access and a formal annual review of all security practices. These are not suggestions. They are the IRS’s baseline data security requirements for professional tax preparers.
3. Does the FTC Safeguards Rule apply to independent tax preparers and small CPA firms?
Yes. The FTC classifies tax preparers and CPA firms as financial institutions under the Gramm-Leach-Bliley Act. This means they are subject to the Safeguards Rule, which requires a written information security program, a designated security coordinator, a formal risk assessment, and annual program reviews. The 2023 rule update introduced stricter documentation, encryption, and monitoring requirements that apply to firms of all sizes.
4. What should I look for when choosing IT support for my accounting firm?
Prioritize providers with verifiable, hands-on experience supporting Drake Tax, Lacerte, ProSeries, UltraTax CS, and QuickBooks Desktop. Ask specifically for their documented response time SLA and first-call resolution rate. Confirm they generate compliance documentation that satisfies IRS Publication 4557 and FTC Safeguards Rule requirements. Avoid general-purpose managed service providers that cannot demonstrate specific accounting and tax software expertise. Those gaps in knowledge become your compliance gaps during filing season.