Introduction
A reverse proxy acts as an essential intermediary in the modern architectural stack, positioned between external clients and backend web servers to manage incoming traffic flow. By intercepting requests at the network edge, these tools provide a centralized point for critical operations such as load balancing, SSL termination, and request routing. This configuration ensures that internal server identities and IP addresses remain shielded from the public internet, creating a robust layer of abstraction. For technical leaders, deploying a reverse proxy is not merely about traffic direction; it is about establishing a high-performance gateway that can inspect, filter, and optimize every packet before it touches sensitive application logic.
The strategic importance of these tools has intensified as organizations transition toward distributed microservices and containerized environments. Modern reverse proxies handle the heavy lifting of encrypting and decrypting data, which offloads significant computational strain from the application servers and improves overall system responsiveness. Furthermore, they serve as the first line of defense against volumetric threats like DDoS attacks by providing a chokepoint where rate limiting and web application firewalls can be strictly enforced. When selecting a platform, architects must evaluate the tool’s ability to handle high concurrency, its support for modern protocols like HTTP/3, and its integration with service discovery mechanisms that reflect the dynamic nature of cloud-native infrastructure.
Best for: Enterprise-scale web applications, Kubernetes-driven microservices, high-traffic e-commerce platforms, and organizations requiring centralized security and compliance management at the edge.
Not ideal for: Simple, single-server static websites with minimal traffic, or internal applications where the overhead of an additional network hop outweighs the benefits of security and load balancing.
Key Trends in Reverse Proxy Tools
The industry is currently witnessing a massive shift toward “observability-first” architectures, where proxies are expected to provide deep-packet inspection and real-time telemetry without introducing latency. We are seeing a move away from static configuration files in favor of dynamic, API-driven control planes that allow for instantaneous routing changes across global fleets. Automation of security certificates has also become a baseline expectation, with many tools now integrating natively with automated certificate authorities to ensure that encryption is always active and up to date without manual intervention.
Another significant trend is the rise of identity-aware proxying, which integrates the reverse proxy directly with corporate identity providers to enforce zero-trust security policies at the entry point. Protocol evolution is also a major driver, with the rapid adoption of QUIC and HTTP/3 requiring proxies to manage complex UDP-based traffic streams. Furthermore, the convergence of reverse proxies and service meshes is blurring traditional boundaries, as edge proxies now frequently share the same data plane technology as the sidecars running alongside individual microservices.
How We Selected These Tools
Our selection process focused on tools that demonstrate exceptional stability and performance under massive production loads. We prioritized solutions that offer a balance between mature, battle-tested codebases and modern, cloud-native features like automatic service discovery. Market adoption played a significant role, as a larger ecosystem ensures better third-party module support and a more reliable pool of documentation for troubleshooting complex edge cases.
We also scrutinized the security posture of each tool, looking for features like FIPS 140-2 compliance, robust ACL systems, and native Web Application Firewall (WAF) capabilities. Performance benchmarks, specifically regarding throughput and resource utilization (CPU/Memory), were analyzed to ensure these tools can serve as efficient gatekeepers. Finally, we considered the developer experience, valuing tools that provide clear configuration syntax, powerful CLI interfaces, and seamless integration with CI/CD pipelines for automated deployment and scaling.
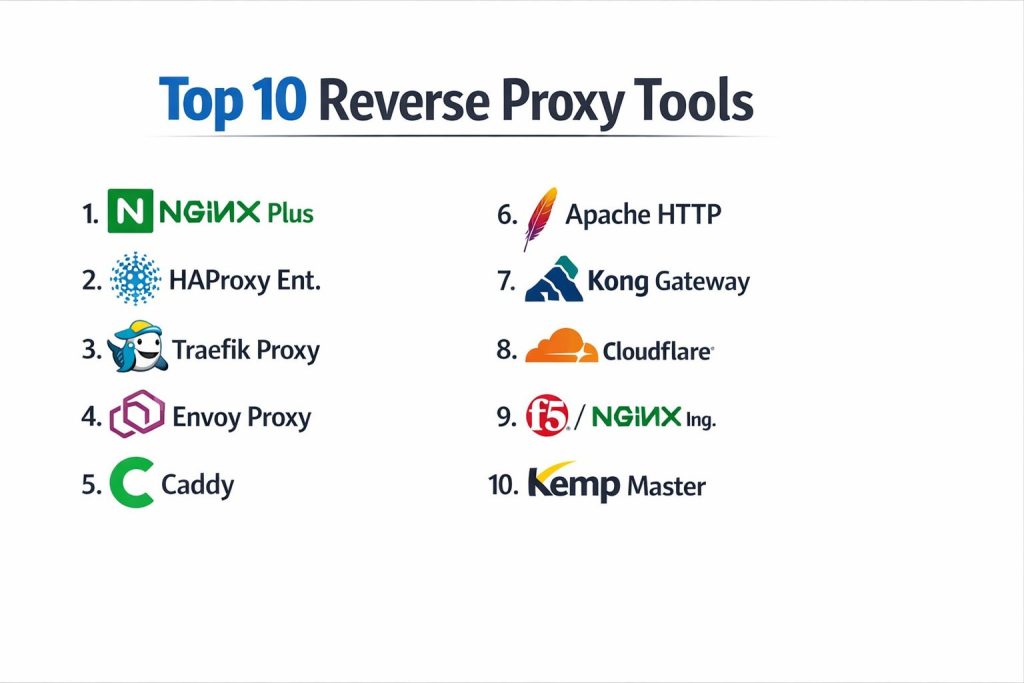
1. NGINX Plus
NGINX Plus is the high-performance, enterprise-grade version of the world’s most popular web server and reverse proxy. It extends the open-source core with advanced features designed for mission-critical environments, such as active health checks, session persistence, and a sophisticated REST API for dynamic configuration. It is engineered to handle tens of thousands of concurrent connections with a very low memory footprint, making it the standard choice for high-traffic digital properties.
Key Features
The platform provides advanced Layer 7 load balancing with support for multiple algorithms like Least Connections and IP Hash. It includes a native Web Application Firewall (WAF) to protect against common web vulnerabilities. Its live activity monitoring dashboard offers real-time visibility into server health and traffic patterns. The tool also supports high-speed content caching and compression to reduce origin server load. Additionally, it offers enterprise-grade SSL/TLS offloading and centralizes certificate management for large-scale deployments.
Pros
It offers unparalleled performance and stability for high-concurrency workloads. The commercial support and advanced feature set make it ideal for enterprises that cannot afford downtime.
Cons
The licensing cost is significant compared to open-source alternatives. Some advanced modules require a deep understanding of its specific configuration syntax to master.
Platforms and Deployment
Windows, Linux, and specialized container images. It is commonly deployed as a standalone gateway or as an Ingress Controller in Kubernetes.
Security and Compliance
It is FIPS 140-2 compliant and supports SOC 2 and HIPAA requirements. It includes integrated DDoS protection and fine-grained access control lists.
Integrations and Ecosystem
Integrates deeply with all major cloud providers and CI/CD tools. It has a massive ecosystem of third-party modules and certified integrations for security and monitoring.
Support and Community
Users benefit from 24/7 global professional support, an extensive technical knowledge base, and a vast community of experienced engineers.
2. HAProxy Enterprise
HAProxy Enterprise is widely regarded as the gold standard for pure load balancing and high-availability proxying. It is built for environments where performance and reliability are the absolute priorities, often serving as the front door for some of the world’s largest websites. The Enterprise version adds a suite of management tools, advanced security features, and dedicated support to the ultra-fast open-source engine.
Key Features
The tool features an industry-leading multi-threaded architecture that maximizes CPU efficiency on modern hardware. It includes advanced health checks that can probe backends at the application level to ensure traffic only reaches healthy servers. Its Global Server Load Balancing (GSLB) allows for traffic distribution across multiple geographical regions. The platform also provides sophisticated rate limiting and bot management to protect backend services. It includes a dedicated portal for managing large clusters of proxy instances from a single interface.
Pros
It delivers the highest throughput and lowest latency of any software-based proxy. Its configuration logic is extremely logical and powerful for complex routing requirements.
Cons
It lacks the built-in web serving capabilities found in NGINX, focusing purely on proxying. The learning curve for its advanced ACL (Access Control List) system can be steep.
Platforms and Deployment
Primarily Linux-based. It is frequently deployed on bare metal for maximum performance or as a high-speed containerized gateway.
Security and Compliance
Complies with GDPR and PCI DSS standards. It features a robust security engine capable of identifying and blocking malicious patterns at the edge.
Integrations and Ecosystem
Supports a wide range of integrations through its Lua scripting engine. It integrates natively with Prometheus for monitoring and various service discovery tools like Consul.
Support and Community
Provides authoritative enterprise support with fast response times and a highly active community focused on high-performance networking.
3. Traefik Proxy
Traefik is a modern reverse proxy designed specifically for microservices and containerized environments. It differentiates itself through “auto-discovery,” where it automatically scans your infrastructure (like Docker or Kubernetes) and configures the necessary routing rules without manual intervention. This makes it a favorite for agile teams who deploy services frequently and need a proxy that can keep up with a constantly changing environment.
Key Features
The core feature is its ability to automatically discover backend services through various providers like Kubernetes, Swarm, and Mesos. It provides a clean, web-based dashboard for visualizing the state of all routes and services. The tool handles SSL/TLS certificates automatically through native ACME integration (Let’s Encrypt). It supports sophisticated middleware for tasks like authentication, rate limiting, and header manipulation. Its dynamic configuration capabilities allow it to update its routing table in real-time without restarting.
Pros
It drastically reduces the operational overhead of managing routes in a dynamic container environment. The built-in support for automatic HTTPS is a major time-saver for developers.
Cons
The “magic” of auto-discovery can sometimes make troubleshooting difficult when configurations don’t behave as expected. It may not be as performant as HAProxy in extremely high-concurrency scenarios.
Platforms and Deployment
Windows, macOS, and Linux. It is native to Docker and Kubernetes ecosystems and is often deployed as a sidecar or ingress.
Security and Compliance
Supports modern security standards and integrates with enterprise identity providers. It is widely used in SOC 2 and HIPAA compliant cloud architectures.
Integrations and Ecosystem
Natively integrates with almost all container orchestrators and service discovery tools. It has a growing library of plugins available through its community marketplace.
Support and Community
Offers enterprise support tiers and has a very modern, rapidly growing community with excellent documentation for cloud-native use cases.
4. Envoy Proxy
Envoy is a cloud-native high-performance edge and service proxy, originally developed at Lyft. It is designed for large-scale microservice architectures where observability and resilience are critical. Envoy is often used as the “data plane” for service meshes like Istio, but it is equally powerful as a standalone edge reverse proxy for managing external traffic.
Key Features
It supports advanced Layer 7 routing and load balancing for HTTP/2 and gRPC traffic. The proxy features a completely dynamic “discovery API” that allows all aspects of its configuration to be updated over the network. It provides industry-leading observability with detailed statistics and distributed tracing integration. Its filter chain architecture allows for deep customization of how requests are processed. It also includes sophisticated resilience features like retries, circuit breaking, and global rate limiting.
Pros
It offers incredible flexibility and is designed from the ground up for massive, distributed environments. The focus on observability makes it much easier to debug complex network issues.
Cons
The configuration is very verbose and can be difficult for humans to write and maintain manually without a control plane. It has a high memory footprint compared to HAProxy or NGINX.
Platforms and Deployment
Linux and macOS. It is almost exclusively deployed in containerized environments and Kubernetes clusters.
Security and Compliance
Built with high-security standards in mind, supporting mTLS and integration with enterprise secret management. It is widely used in regulated financial and healthcare sectors.
Integrations and Ecosystem
It is the backbone of the CNCF cloud-native ecosystem. It integrates perfectly with service meshes, monitoring tools like Jaeger, and modern API management platforms.
Support and Community
Backed by the Cloud Native Computing Foundation (CNCF), it has a massive contributor base and is supported by almost every major cloud provider.
5. Caddy
Caddy is a powerful, enterprise-ready web server and reverse proxy that is famous for its simplicity and “HTTPS by default” philosophy. It is written in Go, which makes it a memory-safe alternative to older C-based proxies. Caddy is ideal for users who want a modern, high-performance proxy that just works out of the box with minimal configuration.
Key Features
The standout feature is its automatic HTTPS, where it handles the entire lifecycle of certificate issuance and renewal automatically. It features a very simple, human-readable configuration syntax called the “Caddyfile.” The tool supports HTTP/3 (QUIC) natively, providing faster performance for modern browsers. It can be configured dynamically through a powerful JSON API. It also includes a robust plugin system that allows users to add features like DNS-based challenge solvers and specialized authentication modules.
Pros
It is arguably the easiest reverse proxy to set up and maintain, especially for managing hundreds of domains. The memory safety of the Go language provides an additional layer of security.
Cons
While very fast, it may not reach the extreme performance heights of HAProxy in specialized benchmarks. The plugin ecosystem is smaller than that of NGINX or Apache.
Platforms and Deployment
Windows, macOS, Linux, and BSD. It is distributed as a single static binary, making deployment exceptionally simple.
Security and Compliance
Highly secure by default, enforcing modern TLS versions and ciphers. It is increasingly adopted in corporate environments where ease of audit is a priority.
Integrations and Ecosystem
Integrates well with modern dev tools and has a clean API for automation. It is a popular choice for developers using Go-based stacks and home lab enthusiasts.
Support and Community
Provides commercial support through its parent company and has a very friendly, active forum where the developers themselves often help users.
6. Apache HTTP Server (mod_proxy)
The Apache HTTP Server remains a titan in the web serving world, and its mod_proxy module provides a highly flexible and mature reverse proxy solution. It is known for its incredible stability and a module-based architecture that has been refined over several decades, making it a safe choice for traditional enterprise stacks.
Key Features
The software offers a vast array of modules that can handle everything from complex URL rewriting to LDAP-based authentication. Its reverse proxy module supports various backend protocols, including AJP for Java-based application servers. It features a reliable load balancing system that can distribute traffic based on several built-in algorithms. The configuration allows for fine-grained control over nearly every aspect of the request-response cycle. It also supports non-blocking, event-driven processing for improved performance under load.
Pros
It is one of the most well-documented pieces of software in history, with solutions for almost any imaginable edge case. Its flexibility allows it to bridge the gap between modern web apps and legacy systems.
Cons
It generally has higher resource consumption and slower performance compared to NGINX or HAProxy. The configuration files can become very large and difficult to manage in complex setups.
Platforms and Deployment
Windows, Linux, macOS, and many Unix variants. It is typically deployed as a standard OS package on traditional servers.
Security and Compliance
Features long-standing, robust security modules and is FIPS 140-2 compatible. It is a staple in government and highly regulated enterprise environments.
Integrations and Ecosystem
It has the largest library of third-party modules in the world. It is the default choice for environments that rely heavily on older technologies like PHP or Java/Tomcat.
Support and Community
Global community support is unparalleled, and professional support is available through numerous third-party vendors and consultants.
7. Kong Gateway
Kong Gateway is a cloud-native API gateway and reverse proxy built on top of the NGINX core. It is designed to act as a central management layer for all your APIs, providing a suite of plugins for authentication, traffic control, and analytics that can be applied to any route with a simple command.
Key Features
The platform uses a modular plugin architecture that allows you to add features like OAuth2, rate limiting, and request transformation without writing code. It supports both traditional database-backed configurations and “DB-less” declarative setups for CI/CD workflows. The gateway provides high-performance traffic routing for REST, gRPC, and GraphQL. It includes a built-in developer portal for documenting and sharing APIs with internal and external teams. Its advanced analytics provide deep insights into API usage and performance.
Pros
It is the most feature-rich choice for organizations that need to manage a large number of APIs with centralized policies. It leverages the raw performance of NGINX while adding a modern management layer.
Cons
Managing the underlying database can add operational complexity in larger deployments. Some of the most valuable enterprise features are locked behind a high-priced subscription.
Platforms and Deployment
Windows, Linux, macOS, and Kubernetes. It is frequently deployed as a centralized API hub in hybrid-cloud environments.
Security and Compliance
Offers enterprise-grade security including SOC 2 Type II and PCI DSS compliance. It provides sophisticated tools for managing secrets and enforcing fine-grained access policies.
Integrations and Ecosystem
Has a massive marketplace of plugins and integrates perfectly with monitoring stacks like ELK and Prometheus. It is a primary choice for organizations moving toward “API-first” architectures.
Support and Community
Offers tiered professional support and has a very large, active community centered around its open-source version.
8. Cloudflare Zero Trust (Cloudflared)
Cloudflare Zero Trust, specifically through the cloudflared agent, provides a modern, cloud-managed reverse proxy experience. Instead of opening ports on your firewall, you run a lightweight tunnel that connects your internal services directly to the Cloudflare global network. This effectively hides your infrastructure from the public internet while providing world-class security and performance at the edge.
Key Features
The tool creates an outbound-only connection to Cloudflare’s network, eliminating the need for complex firewall rules. It provides a centralized dashboard for managing access policies based on user identity and device posture. The service includes world-leading DDoS protection and a globally distributed Web Application Firewall (WAF). It supports high-performance global load balancing with automatic failover. Additionally, it offers built-in observability with detailed logs of every request passing through the tunnel.
Pros
It is one of the most secure ways to expose internal applications, as it completely removes the server’s public IP from the internet. The setup is remarkably fast for teams already using Cloudflare.
Cons
It creates a dependency on Cloudflare’s infrastructure and pricing. There is less granular control over the low-level proxy settings compared to self-hosted tools like HAProxy.
Platforms and Deployment
Windows, macOS, Linux, and Docker. It is typically deployed as a lightweight agent running alongside your applications.
Security and Compliance
Includes top-tier compliance certifications like ISO 27001 and SOC 2. It is a leader in zero-trust security architectures.
Integrations and Ecosystem
Integrates natively with all major identity providers (Okta, Google, Azure AD). It works seamlessly with other Cloudflare edge services like Workers and R2 storage.
Support and Community
Enterprise users get prioritized professional support, while the free tier is backed by an enormous library of self-help documentation and community forums.
9. F5 BIG-IP / NGINX Plus Ingress
F5 is the industry leader in hardware-based application delivery, and their software solutions (including the advanced NGINX Ingress) provide a bridge between traditional data centers and modern cloud environments. These tools are designed for the most demanding enterprise scenarios where security and complex traffic manipulation are paramount.
Key Features
The platform features an advanced policy engine that can inspect and modify traffic based on complex business logic. It includes high-performance SSL/TLS hardware acceleration (in physical deployments) or highly optimized software encryption. Its security suite is among the most comprehensive in the world, covering everything from bot protection to fraud detection. The software provides a unified management plane for controlling traffic across physical, virtual, and cloud-based instances. It also features sophisticated analytics for troubleshooting application performance issues.
Pros
It offers the most comprehensive set of features for application security and delivery in the industry. It is the preferred choice for large-scale financial and government institutions.
Cons
The complexity of the platform requires specialized training to manage effectively. The cost of entry is typically much higher than other software-only solutions.
Platforms and Deployment
Available as hardware appliances, virtual editions (VMware, KVM), and cloud-native container versions.
Security and Compliance
Meets the highest global security standards, including Common Criteria and FIPS 140-2 Level 2. It is designed for maximum compliance in highly regulated sectors.
Integrations and Ecosystem
Integrates with all enterprise IT management suites and cloud platforms. It has a massive network of certified partners and specialized consultants.
Support and Community
Provides world-class, 24/7 technical support and has an established community of networking professionals through its DevCentral platform.
10. Kemp LoadMaster
Kemp LoadMaster is a versatile and user-friendly reverse proxy and load balancer that offers an excellent balance of features and value. It is particularly popular in mid-market organizations and environments that rely heavily on Microsoft applications like Exchange or SharePoint, where it provides pre-configured templates for rapid deployment.
Key Features
The software includes specialized templates that automate the configuration of a reverse proxy for common enterprise applications. it features a built-in Web Application Firewall (WAF) to protect against modern cyber threats. The tool supports high-performance SSL/TLS offloading to free up backend server resources. It provides a simple, intuitive web interface for managing all aspects of the proxy and load balancing. It also includes an “Edge Security Pack” that provides advanced authentication features like single sign-on (SSO).
Pros
It is incredibly easy to deploy and manage, especially for Windows-centric environments. It offers enterprise-grade features at a more accessible price point than F5 or NGINX Plus.
Cons
The interface can feel a bit dated compared to modern cloud-native tools like Traefik. It has a smaller community and fewer third-party plugins than NGINX or Apache.
Platforms and Deployment
Available as hardware, virtual appliances (Hyper-V, VMware), and on major cloud platforms like AWS and Azure.
Security and Compliance
Supports FIPS 140-2 and is frequently used in environments requiring HIPAA and GDPR compliance. It provides robust protection for web-facing applications.
Integrations and Ecosystem
Excellent integration with Microsoft ecosystems and major virtualization platforms. It provides a RESTful API for integration into broader automation workflows.
Support and Community
Kemp is known for its highly rated technical support and provides a wealth of documentation and deployment guides for various use cases.
Comparison Table
| Tool Name | Best For | Platform(s) Supported | Deployment | Standout Feature | Public Rating |
| 1. NGINX Plus | Enterprise Web Apps | Linux, Win, Cont. | Hybrid | Content Caching | 4.8/5 |
| 2. HAProxy Ent. | High-Load Systems | Linux | Local/Cont. | Peak Throughput | 4.9/5 |
| 3. Traefik Proxy | Docker/Kubernetes | Win, Mac, Linux | Container | Auto-Discovery | 4.7/5 |
| 4. Envoy Proxy | Service Mesh/Apps | Linux, Mac | Container | Observability | 4.6/5 |
| 5. Caddy | Solo/Startups | Win, Mac, Linux | Single Bin | Auto HTTPS | 4.8/5 |
| 6. Apache HTTP | Legacy/Traditional | Win, Mac, Linux | Local | Module Ecosystem | 4.4/5 |
| 7. Kong Gateway | API Management | Win, Mac, Linux | Hybrid | Plugin Marketplace | 4.7/5 |
| 8. Cloudflare | Zero Trust Edge | Win, Mac, Linux | Cloud Agent | Firewall Tunnels | 4.9/5 |
| 9. F5 / NGINX Ing. | Mission-Critical | HW, VM, Cloud | Distributed | Policy Engine | 4.5/5 |
| 10. Kemp Master | Mid-Market/MS Apps | VM, Cloud, HW | Hybrid | App Templates | 4.3/5 |
Evaluation & Scoring of Reverse Proxy Tools
The scoring below is a comparative model intended to help shortlisting. Each criterion is scored from 1–10, then a weighted total from 0–10 is calculated using the weights listed. These are analyst estimates based on typical fit and common workflow requirements, not public ratings.
Weights:
- Core features – 25%
- Ease of use – 15%
- Integrations & ecosystem – 15%
- Security & compliance – 10%
- Performance & reliability – 10%
- Support & community – 10%
- Price / value – 15%
| Tool Name | Core (25%) | Ease (15%) | Integrations (15%) | Security (10%) | Performance (10%) | Support (10%) | Value (15%) | Weighted Total |
| 1. NGINX Plus | 10 | 6 | 10 | 9 | 9 | 10 | 7 | 8.85 |
| 2. HAProxy Ent. | 10 | 5 | 9 | 9 | 10 | 10 | 8 | 8.80 |
| 3. Traefik Proxy | 9 | 10 | 10 | 8 | 8 | 8 | 9 | 9.05 |
| 4. Envoy Proxy | 10 | 3 | 10 | 9 | 9 | 9 | 8 | 8.30 |
| 5. Caddy | 8 | 10 | 7 | 9 | 8 | 8 | 10 | 8.45 |
| 6. Apache HTTP | 9 | 6 | 10 | 8 | 6 | 9 | 9 | 8.05 |
| 7. Kong Gateway | 10 | 7 | 10 | 9 | 8 | 9 | 7 | 8.60 |
| 8. Cloudflare | 10 | 9 | 10 | 10 | 9 | 10 | 8 | 9.45 |
| 9. F5 / NGINX Ing. | 10 | 4 | 9 | 10 | 9 | 10 | 5 | 8.05 |
| 10. Kemp Master | 8 | 9 | 8 | 9 | 7 | 9 | 8 | 8.15 |
How to interpret the scores:
- Use the weighted total to shortlist candidates, then validate with a pilot.
- A lower score can mean specialization, not weakness.
- Security and compliance scores reflect controllability and governance fit, because certifications are often not publicly stated.
- Actual outcomes vary with assembly size, team skills, templates, and process maturity.
Which Reverse Proxy Tool Is Right for You?
Solo / Freelancer
For individual developers, Caddy is often the superior choice because it eliminates the complexity of SSL management and offers a clean, modern interface. It allows you to focus on building your application rather than managing the intricacies of the network.
SMB
Small and medium businesses should look toward Traefik if they are running containerized workloads, or NGINX if they need a more traditional, versatile web server. These tools provide the right balance of flexibility and ease of use without requiring a dedicated network engineering team.
Mid-Market
Mid-market companies will find significant value in Kong or HAProxy Enterprise. These tools offer the professional support and advanced management features needed as a team grows, while still being cost-effective compared to high-end hardware solutions.
Enterprise
At the enterprise level, the decision usually comes down to F5 for traditional data center security, or NGINX Plus for modern, cloud-native high-performance routing. These organizations prioritize long-term stability, deep compliance certifications, and 24/7 global support.
Budget vs Premium
Budget-conscious users should stick with the open-source versions of NGINX, HAProxy, or Caddy, which offer professional performance for free. Premium solutions like Cloudflare or NGINX Plus are worth the investment when the cost of a single hour of downtime exceeds the annual licensing fee.
Feature Depth vs Ease of Use
If you need deep technical control over every packet, HAProxy or Envoy are the tools for you. If you want a tool that “just works” with automatic discovery and HTTPS, Caddy and Traefik are much more appropriate.
Integrations & Scalability
For highly integrated environments using Kubernetes and service meshes, Envoy and Traefik are the most scalable options. They are designed to be part of a larger ecosystem and can be automated completely through APIs.
Security & Compliance Needs
Organizations with strict compliance requirements (HIPAA, PCI DSS) should prioritize managed solutions like Cloudflare or established enterprise tools like F5 and NGINX Plus, which provide the audit logs and security certifications required by regulators.
Frequently Asked Questions (FAQs)
1. What is the main difference between a load balancer and a reverse proxy?
While the terms are often used interchangeably, a reverse proxy focuses on the security and optimization of requests before they reach a server, while a load balancer focuses specifically on distributing those requests across multiple servers to ensure high availability.
2. Does using a reverse proxy slow down my website?
When configured correctly, a reverse proxy actually speeds up a website. By handling tasks like SSL termination and content caching, it removes significant load from the application servers and delivers content to users more efficiently.
3. Can I run multiple reverse proxies together?
Yes, this is a common architecture. Many organizations use a cloud-based global proxy (like Cloudflare) for DDoS protection, followed by an internal proxy (like NGINX or Traefik) to handle specific application routing and service discovery.
4. Why is SSL termination important?
SSL termination allows the reverse proxy to handle the heavy math of encryption. This simplifies certificate management by centralizing it in one place and frees up the backend servers to focus entirely on running your application logic.
5. Is NGINX still the best choice for new projects?
NGINX remains an excellent, highly versatile choice for almost any project. However, for modern containerized apps, Traefik’s auto-discovery or Caddy’s simple configuration might offer a faster and more modern workflow.
6. Do I need a public IP address for my backend server?
No. In fact, one of the primary benefits of a reverse proxy is that your backend servers can stay on a private network. Only the reverse proxy needs to be exposed to the public internet, which greatly increases your security posture.
7. Can a reverse proxy protect against SQL injection?
Yes, if it has a Web Application Firewall (WAF) module. Tools like NGINX Plus or Cloudflare can inspect incoming request payloads and block those that contain common attack patterns like SQL injection or cross-site scripting.
8. What is a “sidecar” proxy in Kubernetes?
A sidecar proxy is a small proxy instance (like Envoy) that runs alongside every individual microservice in a container. It handles all network communication for that specific service, enabling features like service-to-service encryption and advanced monitoring.
9. How do I choose between open-source and enterprise versions?
Choose the open-source version if you have the technical expertise to manage and secure the tool yourself. Move to the enterprise version if you require guaranteed uptime, specialized security features, or 24/7 support for business-critical applications.
10. What is “sticky sessions” in a reverse proxy?
Sticky sessions (or session persistence) ensure that a specific user is always routed to the same backend server during their visit. This is important for older applications that store user login or cart data on a specific server’s local memory.
Conclusion
In the complex landscape of modern network architecture, the reverse proxy has evolved from a simple traffic director into a sophisticated control plane for security, performance, and reliability. Choosing the right tool requires a deep understanding of your infrastructure’s specific demands—whether that is the extreme raw throughput of HAProxy, the seamless container integration of Traefik, or the comprehensive zero-trust protection of Cloudflare. A well-implemented proxy strategy does more than just protect your backend; it creates a flexible layer that allows your engineering teams to scale services, rotate certificates, and mitigate threats without ever disrupting the end-user experience. By prioritizing observability and interoperability at the edge, you establish a resilient foundation that can adapt to the shifting needs of both your users and the global threat landscape.