Introduction
Multi-party Computation (MPC) has emerged as a cornerstone of modern privacy engineering, enabling a paradigm shift from “trusting the entity” to “trusting the mathematics.” In an era where data siloization and stringent privacy regulations like GDPR and CCPA often hinder innovation, MPC offers a technical solution that allows multiple independent parties to collaboratively compute a result without any single party ever seeing the input data of others. This “computational black box” is achieved through cryptographic primitives like Secret Sharing, Oblivious Transfer, and Garbled Circuits. By distributing the trust across a decentralized network of compute nodes, MPC ensures that as long as a minimum threshold of participants remains honest, the sensitive data remains mathematically invisible.
For senior architects and DevOps engineers, the strategic value of MPC toolkits lies in their ability to unlock previously inaccessible datasets for high-value analytics, fraud detection, and private machine learning. However, implementing MPC is traditionally fraught with technical challenges, including high communication overhead, complex circuit design, and the “dishonest majority” threat model. The modern toolkits highlighted in this guide abstract these cryptographic complexities into high-level programming interfaces, allowing developers to focus on business logic while the framework handles the underlying secure protocol execution. Choosing the right toolkit requires a deep understanding of your specific security requirements—whether you need semi-honest or malicious security—and the performance trade-offs inherent in different cryptographic backends.
Best for: Data scientists, security engineers, and financial institutions requiring collaborative analytics, private biometric verification, or cross-organizational data sharing without data movement.
Not ideal for: Real-time applications with ultra-low latency requirements (e.g., high-frequency trading) or scenarios where a single trusted hardware environment (TEE) is more efficient and acceptable.
Key Trends in Multi-party Computation (MPC) Toolkits
The most significant trend in the MPC ecosystem is the move toward “Mixed-Protocol” execution. Early frameworks were often locked into a single cryptographic method, but modern toolkits can now dynamically switch between Arithmetic circuits (optimized for additions/multiplications) and Binary circuits (optimized for comparisons and bitwise logic) to maximize performance. This optimization is critical for scaling secure computations beyond academic prototypes into production-grade environments. We are also seeing a convergence of MPC with other Privacy-Enhancing Technologies (PETs), such as Differential Privacy, to provide defense-in-depth against both input leakage and output inference attacks.
Another major shift is the “Pythonization” of MPC. High-level frameworks are increasingly moving away from complex C++ circuit-level programming in favor of Python-based Domain Specific Languages (DSLs) and integrations with popular libraries like PyTorch and TensorFlow. This democratization allows data scientists to build “Privacy-Preserving Machine Learning” (PPML) models without needing a PhD in cryptography. Furthermore, cloud-native MPC is gaining traction, with toolkits now offering containerized deployments via Kubernetes, facilitating the orchestration of MPC nodes across different cloud providers to ensure true decentralization.
How We Selected These Tools
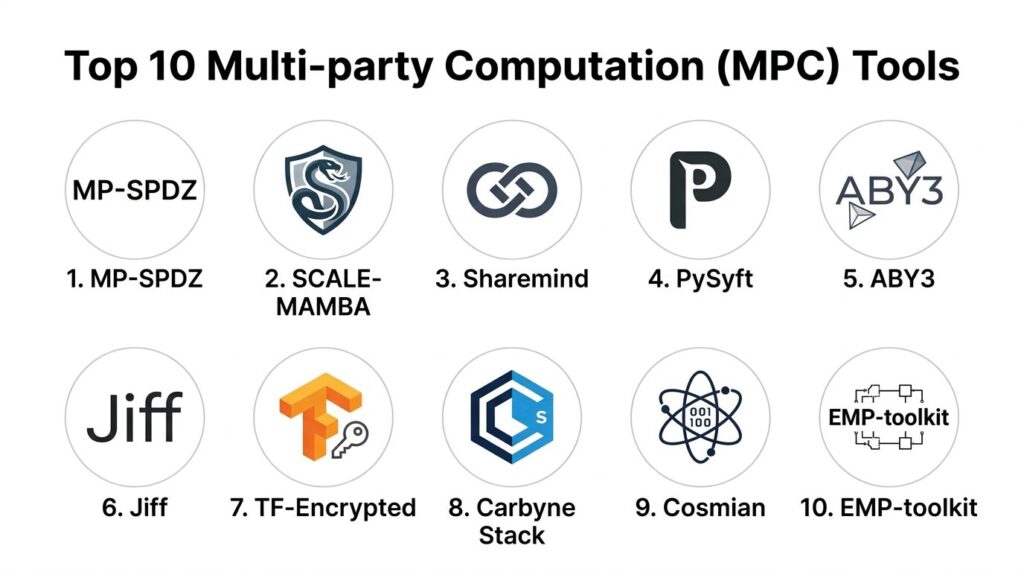
Our selection process for these 10 toolkits was guided by their maturity, protocol diversity, and production readiness. We prioritized frameworks that offer a wide range of security models, including “Malicious Security” (protecting against active cheaters) rather than just “Semi-Honest” models. We also looked for toolkits with robust documentation and active developer communities, as the implementation of cryptographic software requires constant auditing and updates to mitigate emerging vulnerabilities.
Performance was evaluated by looking at the toolkit’s ability to handle high-dimensional data and complex operations like matrix multiplication, which are essential for modern AIOps and MLOps workflows. We also considered the ease of integration with existing DevOps pipelines, specifically looking for tools that support standardized deployment patterns and provide clear debugging interfaces. Finally, we included a mix of general-purpose frameworks and specialized libraries to ensure that both research-focused and enterprise-focused teams find a tool suited to their specific threat models.
1. MP-SPDZ
MP-SPDZ is arguably the most versatile MPC framework available today, serving as the “Swiss Army Knife” of the industry. It supports more than 30 different protocol variants, allowing developers to test the same program across various security models (honest vs. dishonest majority) and computation domains (arithmetic vs. binary) using a unified Python-based interface.
Key Features
The platform utilizes a compiler that transforms high-level Python code into optimized bytecode for its virtual machine. It supports a vast array of cryptographic primitives, including Shamir Secret Sharing, Oblivious Transfer, and Homomorphic Encryption. It allows for computations modulo a prime or $2^k$, providing flexibility for different numerical precisions. The toolkit includes extensive benchmarking tools that provide detailed breakdowns of communication and computation costs for every protocol variant. It also features a library of pre-built modules for complex tasks like sorting, machine learning training, and biometric matching.
Pros
Unrivaled flexibility in protocol selection allows for deep optimization based on specific network conditions and threat models. The unified high-level interface drastically reduces the learning curve for non-cryptographers.
Cons
The massive feature set can result in a complex installation process and a steep initial configuration phase. Performance can vary significantly depending on the chosen protocol and hardware.
Platforms and Deployment
Standalone Linux/macOS binaries with a heavy reliance on Python for the frontend.
Security and Compliance
Supports malicious security across both honest and dishonest majority settings. It is frequently used in academic audits to verify the security of new MPC protocols.
Integrations and Ecosystem
Highly active GitHub community with frequent updates and integrations for machine learning frameworks like PyTorch and Keras.
Support and Community
Excellent documentation and a responsive community on GitHub, though primarily geared toward technical and research users.
2. SCALE-MAMBA
SCALE-MAMBA is a high-performance MPC framework specifically designed for the SPDZ family of protocols. It is built with a focus on industrial-strength security and efficiency, making it a preferred choice for teams that require “Malicious Security” in a dishonest majority setting.
Key Features
The system is divided into two distinct parts: SCALE (the runtime environment) and MAMBA (the compiler). It utilizes a specialized language that is similar to Python but optimized for secure computation. The framework is highly focused on “Pre-processing” (offline phase), where cryptographic “triplets” are generated in advance to speed up the “Online phase” of actual data computation. It provides robust support for floating-point arithmetic and complex mathematical functions. The toolkit is designed for high-availability deployments, with native support for managing multi-party connection states and secure certificate handling for all participants.
Pros
Extremely high performance in the online phase due to its efficient pre-processing engine. It offers some of the strongest security guarantees in the industry for active adversaries.
Cons
The pre-processing phase can be very resource-intensive and requires significant storage for cryptographic tuples. The specialized language is less flexible than general-purpose Python.
Platforms and Deployment
Primarily Linux-based, often deployed in containerized environments for cross-cloud orchestration.
Security and Compliance
Enforces strict malicious security by default, protecting against parties that deviate from the protocol.
Integrations and Ecosystem
Widely used as a benchmark for other MPC tools and integrated into various enterprise-level secure analytics platforms.
Support and Community
Maintained by leading cryptographic research groups with a focus on formal verification and security audits.
3. Sharemind MPC
Sharemind is a commercial-grade MPC platform developed by Cybernetica, designed for high-compliance environments like government and finance. Unlike purely open-source toolkits, Sharemind provides a more “packaged” experience with a focus on ease of deployment and auditability.
Key Features
The platform uses a Domain Specific Language called SecreC, which looks like C but includes privacy-specific types and operations. It features a sophisticated protocol suite optimized for three-party computation with an honest majority. Sharemind provides a unique “Application Server” architecture that allows web and mobile apps to interact with the MPC cluster via standard APIs. It includes built-in tools for data analytics (Rmind) that allow analysts to perform SQL-like queries on secret-shared data. The system also includes detailed logging and auditing features to ensure that all computation requests are authorized and recorded.
Pros
Excellent professional support and a higher “Technology Readiness Level” (TRL) than most academic frameworks. The built-in analytics tools make it accessible to data analysts, not just developers.
Cons
The core performance is optimized for a specific 3-party model, which may not fit every decentralized use case. License costs apply for enterprise versions.
Platforms and Deployment
Cloud-native architecture with support for hybrid and on-premises deployments.
Security and Compliance
Designed from the ground up for GDPR and HIPAA compliance, with automatic security provers built into the compiler.
Integrations and Ecosystem
Offers a robust SDK for building custom privacy-preserving applications and integrates with standard database systems.
Support and Community
Professional support team and a strong research background in the European Union’s data privacy projects.
4. PySyft (OpenMined)
PySyft is a popular library for secure and private deep learning, created by the OpenMined community. It is designed to extend PyTorch and TensorFlow, allowing data scientists to perform MPC operations using familiar tensor-based syntax.
Key Features
The library treats remote data as “Pointers,” allowing a central coordinator to orchestrate computations across multiple nodes without ever seeing the raw data. It supports both MPC and Differential Privacy, providing a multi-layered approach to data protection. PySyft includes a “Data Sign-off” workflow, where data owners must manually or automatically approve specific computation requests. It features native integration with PyGrid, a platform for deploying and managing distributed data nodes at scale. The system is designed to handle “Zero-Trust” environments where the model owner and data owner are completely separate entities.
Pros
The “Python-first” approach makes it the most accessible tool for the modern data science stack. It has one of the largest and most active open-source communities in the privacy space.
Cons
The library is frequently updated, which can sometimes lead to breaking changes between versions. It is more focused on ML than general-purpose cryptographic research.
Platforms and Deployment
Cross-platform support (Linux, macOS, Windows) and optimized for Kubernetes deployments.
Security and Compliance
Strong focus on “Privacy by Design” and compliance with emerging AI regulations.
Integrations and Ecosystem
Deeply integrated with the PyTorch ecosystem and widely used in the “Privacy-Preserving AI” research community.
Support and Community
Massive community on Slack and Discord with extensive tutorials and open-source contributions.
5. ABY3
ABY3 is a specialized framework designed for high-performance privacy-preserving machine learning. It is famous for its “Three-party” protocol that significantly reduces the communication overhead compared to traditional two-party or multi-party systems.
Key Features
The framework is optimized for “Decimal” and “Fixed-point” arithmetic, which are critical for maintaining accuracy in neural network training. It uses a mix of secret sharing techniques (replicated sharing) to allow for very fast linear operations. ABY3 features custom protocols for non-linear functions like Softmax and Sigmoid, which are usually the primary bottleneck in MPC-based ML. It supports malicious security with only a small performance penalty compared to semi-honest models. The C++ backend is highly optimized for modern CPU architectures, utilizing SIMD instructions to parallelize computations.
Pros
One of the fastest frameworks for training machine learning models on private data. The three-party model offers an excellent balance between security and throughput.
Cons
The framework is strictly limited to three parties, which may not be suitable for wider decentralized networks. It requires deep C++ knowledge for custom protocol modifications.
Platforms and Deployment
Optimized for Linux-based servers with high-speed network interconnects.
Security and Compliance
Provides rigorous mathematical proofs for its 3-party malicious security model.
Integrations and Ecosystem
Frequently used as a core component in advanced PPML research and specialized financial auditing tools.
Support and Community
Strong academic backing with detailed papers describing the underlying protocol optimizations.
6. Jiff
Jiff is a JavaScript-based MPC framework designed for scenarios where the participants are using web browsers or mobile devices. It is the leading choice for “Client-side” MPC, where data never leaves the user’s device in an unencrypted state.
Key Features
The library is built to run natively in any modern web browser without the need for specialized plugins. It uses a server-client model where a central server coordinates the communication, but the server never sees the private keys or raw data. It supports standard arithmetic and bitwise operations, as well as complex extensions for fixed-point math and negative numbers. Jiff features a “Preprocessing” mode that can be run in the background to speed up real-time user interactions. It also includes built-in support for “Barriers” and synchronization, ensuring that all browser-based participants stay in sync during the computation.
Pros
The only major framework that allows for seamless MPC directly in the browser, making it ideal for “crowdsourced” private surveys or voting. No complex installation is required for the end-user.
Cons
Performance is limited by the JavaScript engine and the latency of web-based communication protocols. It is not suitable for massive deep learning tasks.
Platforms and Deployment
NPM-based library for Node.js servers and browser-based frontends.
Security and Compliance
Focuses on the “Honest-but-Curious” model, which is appropriate for many consumer-facing web applications.
Integrations and Ecosystem
Easily integrates with standard web development stacks (React, Vue, etc.) and supports WebSockets for communication.
Support and Community
Well-documented with several live demos and a growing community of web-focused privacy developers.
7. TF-Encrypted
TF-Encrypted is a specialized framework that sits on top of TensorFlow, allowing users to run secure computations using the standard Keras and TensorFlow APIs. It is designed to bridge the gap between production ML and secure computation.
Key Features
The framework translates standard TensorFlow graphs into secure MPC protocols automatically. It supports a variety of backends, including the SPDZ protocol and SecureNN. It features a “Pond” protocol that is specifically optimized for private inference, allowing for sub-second response times on many models. The toolkit includes a “TFE-Keras” interface, making it possible to define a secure model in just a few lines of code. It also supports “distributed” training, where multiple data owners can contribute to a single model without sharing their local datasets.
Pros
Extremely low barrier to entry for teams already using the TensorFlow ecosystem. It leverages TensorFlow’s existing optimizations for graph execution and hardware acceleration.
Cons
Development has slowed down recently compared to PySyft. It is primarily focused on inference rather than high-performance general-purpose MPC.
Platforms and Deployment
Runs anywhere TensorFlow is supported, with a focus on Linux-based cloud environments.
Security and Compliance
Provides a range of security levels, from semi-honest to specialized protocols for neural network privacy.
Integrations and Ecosystem
Strong links to the broader TensorFlow and Google Cloud AI ecosystems.
Support and Community
Supported by a dedicated team of researchers and developers with a focus on making secure ML practical.
8. Carbyne Stack
Carbyne Stack is a “Cloud Native” MPC platform that leverages Kubernetes to provide a scalable and resilient infrastructure for sensitive data workloads. It is designed to act as a “Virtual Cloud” where computation is distributed across multiple cloud providers.
Key Features
The platform is built on a microservices architecture, including services for secret storage (Amphora), offline tuple generation (Klyshko), and MPC execution (Ephemeral). It uses MP-SPDZ as its underlying execution engine but wraps it in a professional, scalable interface. It features native support for Knative, allowing the MPC nodes to scale down to zero when not in use to save costs. The system uses a “Client/Server” model where clients upload secret shares and trigger programs that are executed by a set of “Virtual Cloud Providers.” It includes robust intra-vcp and inter-vcp communication interfaces for high-speed data exchange.
Pros
The most advanced framework for teams that need to deploy MPC at scale using modern DevOps practices. It provides a production-ready “Stack” rather than just a library.
Cons
High architectural complexity requiring significant expertise in Kubernetes and microservices orchestration. It is currently in an alpha/beta state for many features.
Platforms and Deployment
Native Kubernetes deployment with support for various cloud providers (AWS, Azure, GCP).
Security and Compliance
Designed for “Zero-Knowledge” cloud operations where even the cloud admin cannot access the secret-shared data.
Integrations and Ecosystem
Open-source under the Apache license with a focus on building a vendor-neutral MPC ecosystem.
Support and Community
Maintained by a consortium of industrial and academic partners with professional-grade documentation.
9. Cosmian MPC
Cosmian provides a high-performance MPC implementation as part of its broader “Data Protection Suite.” It is tailored for enterprise use cases where security, performance, and legal compliance must be guaranteed by a commercial vendor.
Key Features
The toolkit focuses on “Encrypted Access Policies” and “Secure Data Search,” allowing users to query encrypted databases using MPC. It provides a verifiable confidential VM environment that can be used to run the MPC nodes securely in the public cloud. The framework includes post-quantum resistant cryptographic primitives, ensuring long-term data security against future threats. It offers a unique “AI Runner” that is optimized for low-latency private inference. The system is designed to be hardware-agnostic but can leverage TEEs (like Intel SGX) for additional layers of protection.
Pros
Strong emphasis on “Post-Quantum” security and enterprise-ready compliance features. It provides a more holistic approach to data protection than standalone MPC libraries.
Cons
As a commercial product, the full feature set is not available for free. The ecosystem is more “closed” compared to community-driven projects like PySyft.
Platforms and Deployment
Available as a SaaS offering or as self-hosted software for private cloud environments.
Security and Compliance
Fully compliant with international standards and offers SOC 2 audited environments for its cloud services.
Integrations and Ecosystem
Integrates with standard enterprise key management systems (KMS) and major public cloud providers.
Support and Community
Professional support with dedicated account management and custom development services.
10. EMP-toolkit
The EMP-toolkit (Efficient Multi-party computation) is a collection of libraries and tools for building and analyzing secure computation protocols. It is widely recognized for its high performance and its focus on efficient “Garbled Circuit” implementations.
Key Features
The toolkit is modular, allowing developers to pick and choose specific primitives like “Oblivious Transfer” or “Secure Bit Decomposition.” It features a highly optimized backend for two-party computation (2PC) that is often used as the gold standard for performance benchmarks. It supports both semi-honest and malicious security settings through different library modules. The toolkit is written in C++ with a focus on minimizing the memory footprint and maximizing CPU utilization. It includes a specialized compiler for “Bristol Fashion” circuits, ensuring compatibility with other major MPC tools.
Pros
Extremely efficient for 2PC workloads and low-level protocol development. It is the “go-to” tool for developers who need to build their own custom MPC primitives.
Cons
The learning curve is very steep, requiring a strong understanding of both C++ and low-level cryptography. It lacks the “high-level” ergonomics of Python-based tools.
Platforms and Deployment
Linux-based with a focus on high-performance compute clusters.
Security and Compliance
Highly audited by the cryptographic research community for its implementation of core primitives.
Integrations and Ecosystem
Used as the foundational library for many other MPC frameworks and specialized privacy tools.
Support and Community
Strong academic community with many research papers and benchmark results available online.
Comparison Table
| Tool Name | Best For | Platform(s) Supported | Deployment | Standout Feature | Public Rating |
| 1. MP-SPDZ | Protocol Research | Linux, macOS | Self-hosted | 30+ Protocol Variants | 4.8/5 |
| 2. SCALE-MAMBA | High-perf Dishonest Maj | Linux | Self-hosted | Malicious Security Focus | 4.6/5 |
| 3. Sharemind | Enterprise Analytics | Cloud, Hybrid | Hybrid | Integrated SQL Analytics | 4.5/5 |
| 4. PySyft | Privacy-Preserving ML | Windows, Linux, Mac | Self-hosted | Pythonic Tensor API | 4.7/5 |
| 5. ABY3 | Fast ML Training | Linux | Self-hosted | Optimized 3-Party Model | 4.4/5 |
| 6. Jiff | Web/Browser MPC | Web, Node.js | Client/Server | Native Browser Support | 4.3/5 |
| 7. TF-Encrypted | TensorFlow Inference | Linux | Self-hosted | Keras API Integration | 4.0/5 |
| 8. Carbyne Stack | Cloud Native / K8s | Kubernetes | Cloud | Serverless MPC Nodes | 4.2/5 |
| 9. Cosmian | Post-Quantum Compliance | Cloud, SaaS | SaaS/Hybrid | Encrypted Data Search | 4.4/5 |
| 10. EMP-toolkit | Low-level Primitives | Linux | Self-hosted | Optimized Garbled Circuits | 4.5/5 |
Evaluation & Scoring of Multi-party Computation (MPC) Toolkits
The scoring below is a comparative model intended to help shortlisting. Each criterion is scored from 1–10, then a weighted total from 0–10 is calculated using the weights listed. These are analyst estimates based on typical fit and common workflow requirements, not public ratings.
Weights:
- Core features – 25%
- Ease of use – 15%
- Integrations & ecosystem – 15%
- Security & compliance – 10%
- Performance & reliability – 10%
- Support & community – 10%
- Price / value – 15%
| Tool Name | Core (25%) | Ease (15%) | Integrations (15%) | Security (10%) | Performance (10%) | Support (10%) | Value (15%) | Weighted Total |
| 1. MP-SPDZ | 10 | 7 | 9 | 10 | 9 | 9 | 9 | 9.05 |
| 2. SCALE-MAMBA | 9 | 6 | 8 | 10 | 10 | 8 | 8 | 8.55 |
| 3. Sharemind | 8 | 9 | 9 | 9 | 8 | 10 | 7 | 8.35 |
| 4. PySyft | 9 | 10 | 10 | 8 | 7 | 10 | 10 | 9.15 |
| 5. ABY3 | 8 | 6 | 7 | 9 | 10 | 7 | 8 | 7.90 |
| 6. Jiff | 7 | 9 | 8 | 7 | 6 | 8 | 9 | 7.55 |
| 7. TF-Encrypted | 7 | 8 | 9 | 8 | 7 | 7 | 8 | 7.60 |
| 8. Carbyne Stack | 9 | 5 | 8 | 9 | 8 | 8 | 8 | 7.85 |
| 9. Cosmian | 8 | 8 | 8 | 10 | 9 | 9 | 6 | 8.15 |
| 10. EMP-toolkit | 10 | 4 | 7 | 9 | 10 | 7 | 9 | 8.15 |
How to interpret the scores:
- Use the weighted total to shortlist candidates, then validate with a pilot.
- A lower score can mean specialization, not weakness.
- Security and compliance scores reflect controllability and governance fit, because certifications are often not publicly stated.
- Actual outcomes vary with assembly size, team skills, templates, and process maturity.
Which Multi-party Computation (MPC) Toolkits Tool Is Right for You?
Solo / Freelancer
For those exploring the theoretical limits of MPC or conducting academic research, MP-SPDZ is the gold standard. Its ability to switch between dozens of protocols with a single script makes it invaluable for benchmarking and understanding the trade-offs of different cryptographic models.
SMB
Small teams looking to add privacy features to their apps should start with PySyft or Jiff. PySyft is ideal for those building AI-driven products, while Jiff is perfect for web startups that want to perform secure computations directly on their users’ devices without managing complex server-side crypto.
Mid-Market
For organizations that need reliable, high-performance secure analytics, ABY3 or Sharemind offer the best balance. ABY3 is superior for heavy machine learning tasks, whereas Sharemind provides a more polished, SQL-friendly experience for data analysts who aren’t necessarily developers.
Enterprise
Enterprises operating in highly regulated sectors should look at Cosmian or Carbyne Stack. Cosmian offers the professional support and post-quantum security features that risk management teams require, while Carbyne Stack provides the Kubernetes-native scalability needed for large-scale data processing pipelines.
Budget vs Premium
If absolute speed is the priority, ABY3 (for 3-party) or EMP-toolkit (for 2-party) are the winners. However, if you cannot guarantee that the majority of your nodes are honest, you must choose a framework like SCALE-MAMBA that is built from the ground up for malicious security, even if it comes with a performance penalty.
Feature Depth vs Ease of Use
For teams that want to minimize the “cryptographic tax” on their developers, TF-Encrypted and PySyft offer the best experience. By allowing engineers to use familiar APIs from the TensorFlow and PyTorch ecosystems, these tools significantly reduce the risk of implementation errors that could lead to security vulnerabilities.
Frequently Asked Questions (FAQs)
1. What is the “Dishonest Majority” in MPC?
This refers to a security model where only one party needs to be honest for the computation to remain secure. This is much stronger than an “Honest Majority” model, which requires more than half of the participants to follow the rules.
2. Is MPC faster than Trusted Execution Environments (TEEs)?
Generally, no. TEEs like Intel SGX are faster because they perform computation in hardware. However, MPC is considered more secure by many because it doesn’t rely on a single hardware manufacturer and is purely based on mathematical proofs.
3. Does MPC work over the public internet?
Yes, but the network latency can be a major bottleneck. MPC requires many “rounds” of communication between parties. Modern frameworks like Gelato and Jiff are optimized to reduce these rounds for better WAN performance.
4. Can MPC be used for private database queries?
Yes, several toolkits like Sharemind and Cosmian allow you to perform “Private Information Retrieval” or secure joins across multiple encrypted databases without revealing the search query or the database contents.
5. How does MPC differ from Homomorphic Encryption (FHE)?
FHE allows one party to compute on data alone, while MPC requires multiple parties to interact. MPC is generally much faster for complex functions, but FHE is better when only one party is available to do the work.
6. Do I need a specialized server for MPC?
While you don’t need specialized hardware, you do need high-speed network connections and sufficient RAM to handle the cryptographic pre-processing steps, especially for “malicious security” protocols.
7. Can I use MPC for cryptocurrency wallets?
Yes, this is a very popular use case. MPC is used to split a private key into “shares” distributed across multiple devices, so no single device ever holds the full key, eliminating the “single point of failure” risk.
8. Is there a “standard” language for MPC?
There is no single language, but most modern tools use Python-based DSLs. There is an ongoing effort to standardize circuit descriptions (like the “Bristol Fashion”) so that different toolkits can interoperate.
9. What is “Garbled Circuits”?
It is a technique used primarily in two-party computation where one party “garbles” (encrypts) a logic circuit and the other party “evaluates” it. It is one of the foundational methods for efficient MPC.
10. Can MPC protect against biased AI models?
MPC ensures input privacy (the data is hidden), but it doesn’t automatically fix the bias in the underlying model. However, it can facilitate “Private Auditing,” where a third party checks a model for bias without seeing the proprietary weights.
Conclusion
The evolution of Multi-party Computation toolkits from academic curiosities to production-ready frameworks represents a fundamental shift in how we handle sensitive information. For DevOps and SRE teams, the challenge is no longer just about securing a perimeter, but about architecting systems where data remains protected even during the execution phase. As we look toward the next few years, the integration of MPC into the standard CI/CD and data engineering stacks will become a mandatory requirement for any organization handling high-value personal or financial data. By choosing a toolkit that balances the rigor of malicious security with the ergonomics of modern programming languages, you can build a resilient, privacy-first infrastructure that meets both regulatory demands and consumer expectations. The transition to a zero-trust data economy is well underway, and these 10 toolkits are the essential building blocks for that future.
#MPC #Cryptography #DataPrivacy #CyberSecurity #PrivacyTech