Introduction
Decentralized Identity (DID) platforms represent a paradigm shift in how digital identity is managed, moving away from centralized authorities like social media giants or government databases toward a user-centric model. At its core, a DID platform leverages blockchain or distributed ledger technology to allow individuals to own, manage, and share their identity credentials without relying on an intermediary. These platforms utilize cryptographic keys and “verifiable credentials” to prove attributes—such as age, professional certifications, or citizenship—without revealing the underlying sensitive data. In a professional landscape increasingly plagued by data breaches and privacy concerns, DID technology offers a way to build trust through mathematics rather than institutional reputation.
The relevance of decentralized identity has grown alongside the rise of the sovereign web and zero-trust security architectures. Organizations across finance, healthcare, and supply chain management are adopting these platforms to streamline onboarding processes, reduce the risk of identity theft, and comply with stringent data residency regulations. By returning control of the digital “persona” to the individual, DID platforms eliminate the “honeypots” of centralized data that hackers frequently target. When evaluating these platforms, buyers must look at the underlying protocol’s interoperability, the ease of integration into existing enterprise systems, and the robustness of the developer tools provided for building decentralized applications.
Best for: Security-conscious enterprises, government agencies, fintech developers, and organizations looking to implement zero-trust authentication or compliant data-sharing ecosystems.
Not ideal for: Organizations with very low security requirements or those that prefer the simplicity of traditional “Sign in with Google” models and are not concerned with data ownership or intermediary risks.
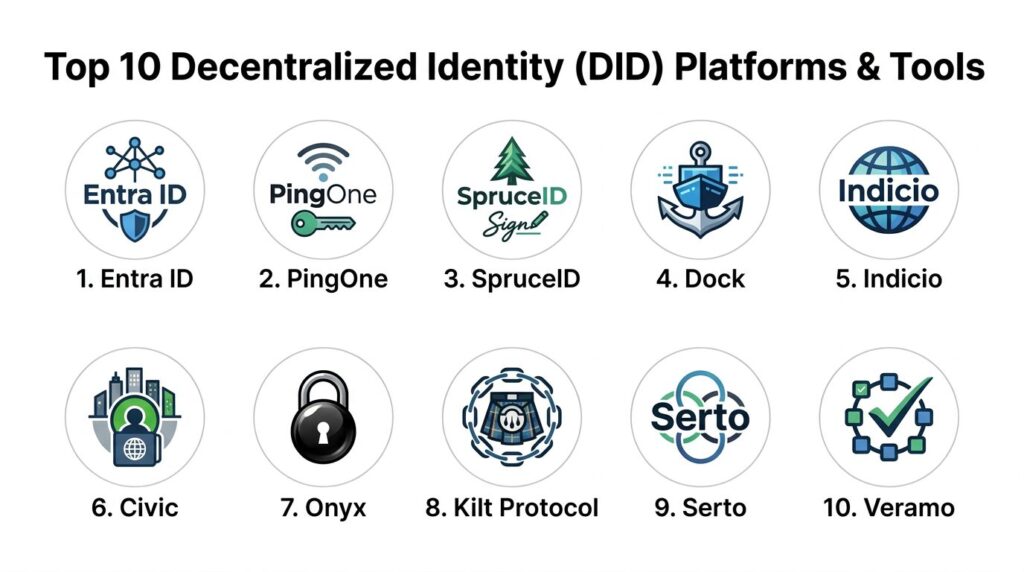
Key Trends in Decentralized Identity Platforms
The primary trend in this space is the push for cross-chain interoperability, ensuring that a digital identity created on one network can be verified and used across various other blockchains and legacy systems. We are also seeing the emergence of “Biometric Decentralized Identity,” where hardware-based biometrics are used to secure cryptographic keys, providing a more user-friendly layer to complex security protocols. Zero-knowledge proofs (ZKPs) have become a standard feature, allowing users to verify specific information—like being over a certain age—without disclosing their actual birthdate.
Another major shift is the integration of DIDs into the Internet of Things (IoT), where devices are given their own unique decentralized identities to ensure secure and autonomous machine-to-machine communication. Regulatory alignment is also maturing, with platforms now building “compliance-by-design” features that map decentralized protocols to legal frameworks like the European eIDAS regulation. Furthermore, the focus on “Social Recovery” mechanisms is increasing, allowing users to regain access to their identity through a network of trusted contacts, solving the long-standing issue of lost private keys in decentralized systems.
How We Selected These Tools
The selection of these platforms was based on a rigorous evaluation of their technical maturity and their contributions to the global DID ecosystem. We prioritized platforms that adhere to the World Wide Web Consortium (W3C) standards for decentralized identifiers, ensuring long-term viability and compatibility. Market mindshare was a significant factor, as platforms with larger developer communities offer more extensive libraries and peer-reviewed security audits. We also examined the “governance models” of the underlying networks to ensure they are truly decentralized and not controlled by a single corporate entity.
Performance was evaluated based on the speed of credential issuance and the latency of verification processes in production environments. We sought out platforms that offer diverse SDKs and documentation, making it easier for traditional IT teams to bridge the gap between legacy systems and blockchain-based identity. Security was assessed by looking at the cryptographic methods used for key management and the platform’s history of resilience against common attack vectors. Finally, we considered the practical utility of each tool across different industry verticals, from healthcare to decentralized finance (DeFi).
1. Microsoft Entra Verified ID
Microsoft Entra Verified ID is an enterprise-grade service built on open standards that allows organizations to issue and verify digital identity credentials. It leverages the ION network, a decentralized Layer 2 protocol that runs on top of the Bitcoin blockchain, providing massive scale and security. It is designed to work seamlessly within the broader Microsoft ecosystem while maintaining the core principles of self-sovereign identity.
Key Features
The platform provides a streamlined portal for organizations to define and issue verifiable credentials for employees or partners. It includes a user-friendly wallet interface integrated into the Microsoft Authenticator app for managing credentials. The system supports open-source protocols like Sidetree for high-throughput decentralized identifier operations. It features automated verification workflows that can be integrated into existing web applications via standard APIs. Additionally, it offers robust reporting and auditing tools to monitor the lifecycle of issued credentials across the organization.
Pros
It bridges the gap between traditional enterprise IT and decentralized identity, making it accessible for companies already using Microsoft services. The underlying ION network provides one of the most secure and decentralized foundations available.
Cons
While built on open standards, users might find themselves gravitating toward the Microsoft ecosystem for the best experience. The technical setup for custom credential types requires a solid understanding of DID protocols.
Platforms and Deployment
Cloud-based service managed through the Azure portal with mobile support via Microsoft Authenticator.
Security and Compliance
Utilizes Bitcoin-level security for the root of trust and is compliant with major global standards like GDPR and SOC 2.
Integrations and Ecosystem
Deeply integrated with Azure Active Directory and the broader Entra suite, with support for any system that can communicate via REST APIs.
Support and Community
Offers professional enterprise support through Microsoft, backed by extensive technical documentation and a large global partner network.
2. Ping Identity (PingOne DaVinci)
Ping Identity has moved aggressively into the decentralized space with its orchestration engine, which allows for the integration of DIDs into complex identity journeys. They focus on providing a “bridge” for enterprises to adopt decentralized models without replacing their entire existing infrastructure.
Key Features
The platform uses a drag-and-drop orchestration tool to build identity workflows that include decentralized verification steps. It supports the issuance of verifiable credentials that users can store in a digital wallet of their choice. The system includes a “Digital Wallet SDK” for businesses that want to build their own branded identity applications. It features advanced fraud detection signals that work alongside decentralized proofs. The architecture is designed to support multiple different DID methods and blockchain backends simultaneously.
Pros
It is excellent for large organizations that need to mix traditional and decentralized identity models in a single user journey. The orchestration engine drastically reduces the amount of custom code needed to implement DIDs.
Cons
The platform is a premium enterprise solution with a pricing structure to match. It may be overly complex for small startups looking for a simple, pure-play DID solution.
Platforms and Deployment
Cloud-native platform (SaaS) with mobile SDKs for iOS and Android.
Security and Compliance
Holds numerous certifications including ISO 27001 and SOC 2 Type II, with a heavy focus on FIPS-compliant cryptography.
Integrations and Ecosystem
Extensive marketplace of integrations covering almost all major HR, CRM, and security platforms.
Support and Community
Provides dedicated enterprise support, a professional services arm, and an active community forum for identity professionals.
3. SpruceID
SpruceID is a leader in the “Sign-In with Ethereum” (SIWE) movement and provides a suite of open-source tools for decentralized identity. They focus on providing the “plumbing” for the decentralized web, allowing users to control their data across platforms ranging from Web3 applications to traditional enterprise software.
Key Features
The platform features a toolkit for implementing secure, wallet-based authentication that replaces traditional passwords. It includes a specialized storage solution that allows users to store their personal data in encrypted “vaults” they control. The software supports the creation of verifiable credentials for professional and social attributes. It provides a library for managing decentralized identifiers across various blockchain networks. The system is designed to be highly modular, allowing developers to pick only the components they need for their specific application.
Pros
It is a favorite among developers due to its open-source nature and clean, well-documented SDKs. It offers a very high degree of data sovereignty by giving users direct control over their storage.
Cons
Requires a higher level of technical expertise to implement compared to more “packaged” enterprise solutions. Documentation is robust but aimed primarily at developers rather than business administrators.
Platforms and Deployment
Self-hosted or integrated via open-source libraries; cloud-agnostic and cross-platform.
Security and Compliance
Relies on battle-tested cryptographic libraries and community-driven security audits; certifications vary by deployment.
Integrations and Ecosystem
Strongest in the Ethereum and Web3 ecosystem but provides tools for integration with legacy OIDC and SAML systems.
Support and Community
Active Discord community and GitHub presence, with professional support available for enterprise partners.
4. Dock
Dock is a dedicated blockchain and platform designed specifically for the issuance and management of decentralized identities and verifiable credentials. It focuses on providing a high-performance, low-cost infrastructure for high-volume credential issuers like universities and certification bodies.
Key Features
The platform features its own purpose-built blockchain for recording DID operations with high throughput. It provides a specialized “Ceremonies” feature for secure, decentralized key generation. The system includes a web-based dashboard for managing credentials without writing code. It offers a mobile wallet app and a mobile SDK for custom wallet development. The platform also supports “Revocation Registries” that allow issuers to instantly invalidate a credential if it is no longer true.
Pros
The dedicated blockchain ensures that identity operations are not slowed down by unrelated network traffic. It offers a very cost-effective model for organizations that need to issue thousands of credentials.
Cons
Using a niche blockchain means it may have less broad network security than Bitcoin or Ethereum-based solutions. Some enterprise users may be hesitant to adopt a new, specialized chain.
Platforms and Deployment
Cloud-based API and dashboard, with an underlying decentralized blockchain network.
Security and Compliance
Utilizes W3C-compliant standards and features decentralized governance for the network; GDPR compliance features are built into the protocol.
Integrations and Ecosystem
Provides a robust API and SDKs for JavaScript and other major languages, with a focus on interoperability with other DID networks.
Support and Community
Offers a developer-focused help center, active social channels, and professional support for high-volume issuers.
5. Indicio
Indicio provides a comprehensive suite of tools for building and deploying decentralized identity networks, primarily focused on the Hyperledger Aries and Indy frameworks. They are known for providing “production-ready” infrastructure for organizations that want to launch their own private or public identity ecosystems.
Key Features
The platform offers a hosted environment for running identity agents and mediators. It features a professional-grade wallet application that can be white-labeled for specific organizations. The system includes a “Provenance” network for tracking the lifecycle of verifiable credentials across multiple parties. It provides extensive developer tools for building “Trusted Digital Assistants.” The architecture is designed to be fully interoperable with any other network following the Hyperledger identity standards.
Pros
It is one of the most mature solutions for organizations that want to use Hyperledger technology without managing the complex underlying infrastructure themselves. Their focus on interoperability makes them a safe choice for multi-party consortiums.
Cons
The Hyperledger ecosystem can have a steep learning curve for teams used to more modern, lightweight Web3 stacks. The costs are geared toward enterprise and consortium use cases.
Platforms and Deployment
Hybrid cloud deployment with managed nodes and mobile components.
Security and Compliance
Built on the highly secure Hyperledger framework and offers extensive tools for meeting data privacy and regulatory requirements.
Integrations and Ecosystem
Deeply integrated into the Hyperledger and Linux Foundation identity ecosystems, with tools for bridging to other DLTs.
Support and Community
Provides top-tier professional services, training, and 24/7 support for mission-critical deployments.
6. Civic
Civic is a long-standing player in the identity space that has pivoted toward providing decentralized identity for the Solana ecosystem and beyond. They focus on “identity as a service,” helping applications verify that their users are real humans without requiring the storage of personal data.
Key Features
The platform features a “Civic Pass” which acts as a non-transferable token that proves a user has met certain verification requirements. It provides automated tools for age verification and bot detection. The system includes a secure identity wallet for users to store their verified attributes. It offers a decentralized “reputation” system that can be used in governance and DeFi. The architecture uses zero-knowledge proofs to ensure that only the “proof” of an attribute is shared, never the attribute itself.
Pros
It is exceptionally easy to integrate for developers building on the Solana blockchain. It provides a very smooth, “consumer-grade” user experience for the end-user.
Cons
Historically very focused on the Solana ecosystem, which might be a limitation for enterprises on other chains. The service model is more “managed” than some of the purely open-source alternatives.
Platforms and Deployment
SaaS-based verification services with mobile wallet applications.
Security and Compliance
Features advanced biometric verification and is designed to help dApps meet KYC and AML requirements without storing user PII.
Integrations and Ecosystem
Dominant presence in the Solana DeFi and NFT space, with expanding support for other EVM-compatible chains.
Support and Community
Offers an active developer portal, community Discord, and dedicated support for enterprise integration.
7. Onyx by J.P. Morgan
Onyx represents the entry of major institutional finance into the decentralized identity space. It provides a platform for “Verifiable Credentials” specifically tailored for the needs of the financial services industry, focusing on privacy-preserving compliance and secure asset movement.
Key Features
The platform is built on top of a private, permissioned version of the Ethereum blockchain. It provides specialized credentials for KYC (Know Your Customer) and AML (Anti-Money Laundering) status. The system includes tools for the secure exchange of documents and identities between financial institutions. It features high-throughput architecture designed to handle the scale of global banking transactions. The platform also focuses on “Institutional DeFi,” allowing verified entities to interact in private liquidity pools.
Pros
It carries the massive institutional credibility of J.P. Morgan, which is a significant factor for other banks and regulators. It is designed specifically to meet the high-security and regulatory hurdles of the finance sector.
Cons
As a permissioned network, it is not as “open” as public blockchain alternatives. Access is generally restricted to institutional partners and clients.
Platforms and Deployment
Managed private cloud infrastructure.
Security and Compliance
Meets the most stringent banking security standards in the world and is built to be regulator-friendly.
Integrations and Ecosystem
Deeply integrated with the Onyx Digital Assets platform and other J.P. Morgan blockchain initiatives.
Support and Community
Dedicated institutional support and relationship management, with access to J.P. Morgan’s extensive technical resources.
8. Kilt Protocol
Kilt Protocol is a decentralized identity blockchain built on the Polkadot network. It provides a simple, modular way for developers to create identities for people, machines, and services, emphasizing a “business-first” approach to identity on the web.
Key Features
The platform features a unique “Claim-Attest” model where users claim attributes and trusted entities attest to them. It includes “SocialKYC,” a service that allows users to prove ownership of social media accounts without revealing personal data. The system supports the creation of DIDs for IoT devices to ensure secure firmware updates and communication. It offers a browser extension for managing identities and interacting with decentralized apps. The protocol also features a built-in mechanism for managing and rewarding attesters within the network.
Pros
The “SocialKYC” feature is one of the most practical applications of DID for general web users. Being part of Polkadot allows for native interoperability with a wide range of other specialized blockchains.
Cons
The Polkadot ecosystem can be technically daunting for those unfamiliar with “parachains.” The token-based governance may introduce economic complexities for some users.
Platforms and Deployment
Decentralized blockchain network with browser-based tools and SDKs.
Security and Compliance
Leverages the shared security model of the Polkadot Relay Chain and uses W3C-compliant DID standards.
Integrations and Ecosystem
Strongest within the Polkadot and Kusama ecosystems, with increasing bridges to Ethereum and other networks.
Support and Community
Highly active developer community, extensive documentation, and a dedicated foundation supporting the protocol.
9. Serto
Serto (formerly part of ConsenSys Mesh) provides a set of user-friendly tools designed to make decentralized identity accessible to everyday businesses. They focus on lowering the barrier to entry for issuing and managing verifiable credentials without needing deep blockchain expertise.
Key Features
The platform features a “Search” tool for finding and verifying decentralized identifiers across different networks. It provides a simple API for issuing verifiable credentials from existing business databases. The system includes a “Schema” manager to help organizations define what their digital certificates should look like. It offers a managed service for those who don’t want to run their own identity nodes. The interface is designed to look and feel like a modern SaaS product, hiding the complexity of the underlying ledger.
Pros
It is one of the most accessible tools for a traditional business to start experimenting with DIDs. The focus on “schemas” ensures that data remains structured and usable across different systems.
Cons
Might lack some of the deeper technical customization required by very advanced Web3 projects. As a managed service, it introduces a degree of reliance on the Serto platform.
Platforms and Deployment
Cloud-based SaaS platform.
Security and Compliance
Standard SaaS security certifications with a focus on implementing W3C and DIF (Decentralized Identity Foundation) privacy standards.
Integrations and Ecosystem
Strongest in the Ethereum ecosystem but designed to be ledger-agnostic where possible.
Support and Community
Offers clear documentation, a responsive help desk, and professional consulting for custom implementations.
10. Veramo
Veramo is a highly flexible, plugin-based framework for decentralized identity. It is not a network itself but rather a powerful software engine that can be used to build identity-enabled applications across any environment, from mobile phones to backend servers.
Key Features
The framework features a “modular-first” architecture where every piece of functionality—from storage to DID methods—is a plugin. It supports multiple ledgers out of the box, including Ethereum, Bitcoin, and others. The system includes a powerful agent-to-agent communication layer for secure data exchange. It provides a CLI (Command Line Interface) for rapid testing and development. The architecture is designed to be extremely lightweight, making it suitable for resource-constrained environments like mobile apps or IoT devices.
Pros
It offers the absolute maximum amount of flexibility for developers; you are never locked into a single blockchain or storage provider. The plugin system allows the framework to evolve quickly as new DID standards emerge.
Cons
Because it is a framework and not a “finished” product, it requires significant development work to create a complete end-user solution. Not suitable for business users looking for an “out-of-the-box” dashboard.
Platforms and Deployment
Open-source software framework for Node.js, React Native, and web browsers.
Security and Compliance
Depends on the specific plugins and deployment strategy chosen by the developer; uses highly vetted cryptographic libraries.
Integrations and Ecosystem
One of the most interoperable tools in the space, with a large library of community-contributed plugins for various networks.
Support and Community
Thriving developer community on GitHub and Discord, with a focus on collaborative open-source improvement.
Comparison Table
| Tool Name | Best For | Platform(s) Supported | Deployment | Standout Feature | Public Rating |
| 1. Entra ID | Enterprise/Azure | Win, Mac, Cloud | SaaS/Hybrid | Bitcoin-based ION | 4.6/5 |
| 2. PingOne | Identity Orchestration | Cloud, Mobile | SaaS | Journey Orchestration | 4.5/5 |
| 3. SpruceID | Web3/Ethereum | Cross-platform | Self-hosted | Sign-In with Ethereum | 4.7/5 |
| 4. Dock | High-Volume Issuers | Cloud, API | Blockchain | Dedicated DID Chain | 4.4/5 |
| 5. Indicio | Consortiums | Hybrid, Mobile | Managed | Hyperledger Expertise | 4.6/5 |
| 6. Civic | Bot Detection/Solana | Web, Mobile | SaaS | Civic Pass Verified | 4.3/5 |
| 7. Onyx | Institutional Finance | Private Cloud | Managed | Bank-grade Compliance | N/A |
| 8. Kilt Protocol | Machine/Social ID | Blockchain | Decentralized | SocialKYC Proofs | 4.5/5 |
| 9. Serto | Simplified Adoption | Web-based | SaaS | DID Search & Schema | 4.2/5 |
| 10. Veramo | Custom Development | Node.js, Mobile | Library | Modular Plugin System | 4.8/5 |
Evaluation & Scoring of Decentralized Identity (DID) Platforms
The scoring below is a comparative model intended to help shortlisting. Each criterion is scored from 1–10, then a weighted total from 0–10 is calculated using the weights listed. These are analyst estimates based on typical fit and common workflow requirements, not public ratings.
Weights:
- Core features – 25%
- Ease of use – 15%
- Integrations & ecosystem – 15%
- Security & compliance – 10%
- Performance & reliability – 10%
- Support & community – 10%
- Price / value – 15%
| Tool Name | Core (25%) | Ease (15%) | Integrations (15%) | Security (10%) | Performance (10%) | Support (10%) | Value (15%) | Weighted Total |
| 1. Entra ID | 10 | 8 | 10 | 10 | 9 | 10 | 7 | 9.05 |
| 2. PingOne | 9 | 9 | 10 | 9 | 9 | 9 | 6 | 8.55 |
| 3. SpruceID | 10 | 5 | 9 | 9 | 9 | 8 | 9 | 8.60 |
| 4. Dock | 8 | 8 | 7 | 8 | 10 | 8 | 9 | 8.20 |
| 5. Indicio | 9 | 7 | 8 | 9 | 8 | 10 | 7 | 8.25 |
| 6. Civic | 7 | 9 | 8 | 8 | 9 | 8 | 8 | 8.00 |
| 7. Onyx | 9 | 5 | 7 | 10 | 9 | 9 | 5 | 7.60 |
| 8. Kilt Protocol | 8 | 7 | 8 | 9 | 8 | 9 | 8 | 8.10 |
| 9. Serto | 7 | 10 | 8 | 8 | 8 | 8 | 8 | 8.10 |
| 10. Veramo | 10 | 4 | 10 | 9 | 10 | 8 | 9 | 8.65 |
How to interpret the scores:
- Use the weighted total to shortlist candidates, then validate with a pilot.
- A lower score can mean specialization, not weakness.
- Security and compliance scores reflect controllability and governance fit, because certifications are often not publicly stated.
- Actual outcomes vary with assembly size, team skills, templates, and process maturity.
Which Decentralized Identity (DID) Platform Tool Is Right for You?
Solo / Freelancer
For individual developers or those working on small-scale projects, Veramo or SpruceID offer the best entry points. Their open-source nature and robust libraries allow you to experiment with decentralized identity without any upfront platform fees or corporate overhead.
SMB
Small and medium businesses that need to get to market quickly without deep blockchain knowledge should look at Serto or Civic. These platforms provide a more “productized” version of DID that can be integrated into existing web apps with minimal friction.
Mid-Market
Organizations in this tier often have more complex security requirements and may be part of larger professional networks. Dock or Kilt Protocol are strong choices here, offering specialized infrastructure for issuing credentials at a predictable cost while maintaining high performance.
Enterprise
For large corporations that are already heavily invested in cloud infrastructure, Microsoft Entra Verified ID or PingOne DaVinci are the logical choices. They provide the security, compliance, and integration depth that major enterprise IT departments demand.
Budget vs Premium
If the primary concern is the lowest possible cost for custom builds, Veramo is the winner. For those who are willing to pay a premium for a managed service that handles all the technical and regulatory heavy lifting, Onyx or Ping Identity are the standout options.
Feature Depth vs Ease of Use
Veramo represents the absolute maximum in feature depth but requires significant effort to master. On the other end, Serto provides a very easy-to-use interface but sacrifices some of the deeper technical customization found in modular frameworks.
Integrations & Scalability
If your goal is to integrate with a wide variety of legacy HR and security systems, Microsoft and Ping Identity are unmatched. For scalability within the blockchain ecosystem itself, Dock and Kilt Protocol offer dedicated chains that won’t get bogged down by unrelated transactions.
Security & Compliance Needs
Financial institutions and high-security government bodies should prioritize Onyx or Indicio. These platforms are built with institutional-grade compliance and long-term security in mind, often favoring stability and vetted protocols over the latest experimental features.
Frequently Asked Questions (FAQs)
1. What is the difference between a DID and a traditional username?
A username is owned and controlled by the platform you sign into, which can delete or lock it at any time. A DID is owned and controlled by you, stored on a decentralized ledger, and cannot be taken away or altered by any single central authority.
2. Is my personal data stored on the blockchain in a DID system?
No, professional DID platforms do not store personal data on the blockchain. Instead, the blockchain stores only the decentralized identifier and a public key; your personal data stays in your private digital wallet and is only shared directly with those you choose.
3. What happens if I lose my phone or my digital wallet?
Most modern DID platforms implement “social recovery” or “backup” mechanisms. This allows you to regain control of your identity through a network of trusted contacts or an encrypted cloud backup, rather than losing it forever like a traditional private key.
4. How do organizations verify the credentials I share?
When you share a credential, the verifier checks the blockchain for the public key of the entity that issued it (e.g., a university). They then use cryptography to prove that the credential was signed by that key and has not been tampered with since it was issued.
5. Are DID platforms compliant with GDPR?
Yes, decentralized identity is often considered the “gold standard” for GDPR compliance because it follows the principle of data minimization. Since the user controls their own data and shares only what is necessary, organizations can verify attributes without ever “possessing” the sensitive data.
6. Can a single DID be used across multiple different apps?
Yes, that is the primary goal of interoperability. A single DID can store multiple different credentials (like a driver’s license, a work ID, and a gym membership) and be used to sign into any application that supports the relevant DID standards.
7. Do I need to understand blockchain to use a DID platform?
If you are an end-user, no; it should feel as simple as using a digital wallet or a password manager. If you are a developer, you need to understand the basic concepts of public-key cryptography and decentralized identifiers, but most platforms provide SDKs that handle the ledger interactions.
8. What is a “Verifiable Credential” (VC)?
A VC is a digital version of a physical document, like a passport or a diploma. It is cryptographically secured so that the person receiving it can be 100% sure who issued it and that the information inside has not been changed.
9. Can DIDs be used for physical access control?
Yes, many enterprises are now using DIDs to grant access to physical buildings. An employee can “scan” their verified work credential at a door, and the system verifies their identity and permissions instantly through a decentralized proof.
10. How do these platforms make money if they are decentralized?
Most platforms operate on a SaaS model for the issuer (the university or employer) while remaining free for the holder. Some also charge small transaction fees on their specific blockchain for recording or revoking identity operations.
Conclusion
Decentralized Identity is no longer a theoretical concept; it is a critical infrastructure component for the future of digital trust. As we move away from the era of centralized data silos, selecting the right DID platform becomes a matter of balancing institutional security with user-centric sovereignty. Whether you are an enterprise integrating Microsoft’s Entra to secure your remote workforce or a developer utilizing Veramo to build the next generation of private-by-design applications, the transition to decentralized models is inevitable. The “best” platform is the one that respects the long-term ownership of the user while providing the practical integration tools necessary for today’s business environment. I recommend starting with a small-scale pilot to verify one specific credential type before committing to a full-scale ecosystem migration.