Introduction
Cloud-Native Application Protection Platforms (CNAPP) represent the architectural convergence of siloed security tools into a unified, risk-centric ecosystem. As organizations migrate from monolithic architectures to distributed, containerized microservices, traditional security perimeters have effectively dissolved. A modern CNAPP suite integrates Cloud Security Posture Management (CSPM), Cloud Workload Protection (CWPP), and Cloud Infrastructure Entitlement Management (CIEM) into a single “pane of glass.” This consolidation is not merely a matter of convenience; it is a technical necessity to understand the complex “attack paths” that emerge when misconfigurations, over-privileged identities, and software vulnerabilities intersect across multi-cloud environments.
The strategic objective of a CNAPP is to shift security both “left” into the development pipeline and “right” into the runtime environment. By correlating signals from Infrastructure as Code (IaC) templates with real-time telemetry from production clusters, these suites enable security teams to prioritize the 1% of alerts that represent a true existential risk to the business. In the current landscape, where ephemeral workloads and agentless scanning are the standards, a CNAPP acts as the central nervous system for DevSecOps, ensuring that security guardrails are enforced at the speed of cloud deployment without introducing friction to the engineering lifecycle.
Best for: Security operations centers (SOC), DevSecOps teams, and C-level executives in mid-to-large enterprises who need to consolidate multi-cloud visibility and automate compliance across AWS, Azure, GCP, and Kubernetes.
Not ideal for: Small businesses with static, single-server environments or legacy on-premises data centers that do not utilize cloud-native orchestration or containerization.
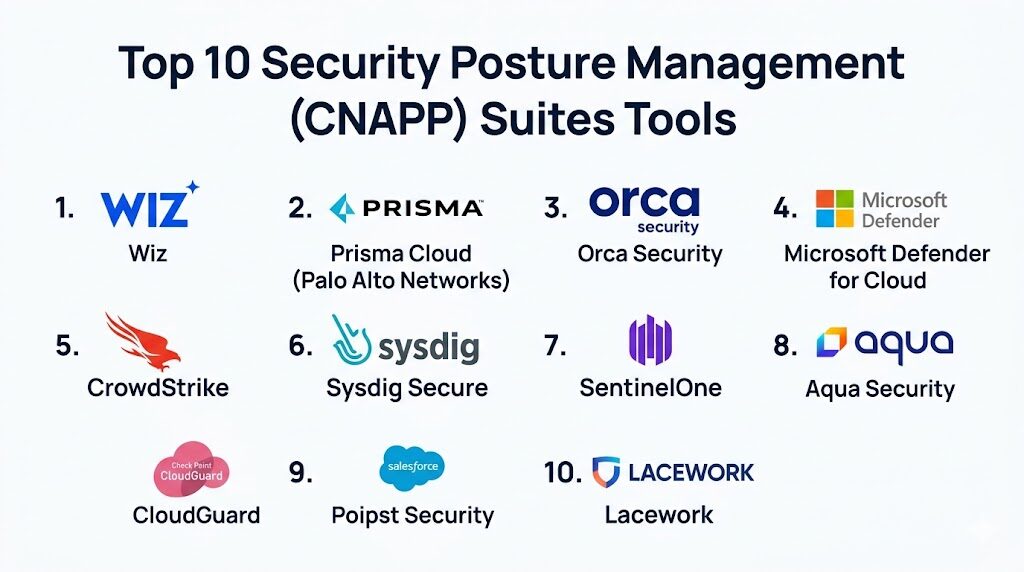
Key Trends in Security Posture Management (CNAPP) Suites
The industry is currently witnessing a massive shift toward “Security Graphs,” which utilize graph database technology to map the relationships between all cloud assets, identities, and vulnerabilities. This allows for automated “Attack Path Analysis,” where the platform can predict how an attacker might move laterally from a public-facing container to a sensitive database. Furthermore, “Agentless Scanning” has become the dominant deployment model, leveraging cloud provider APIs and disk snapshots to provide 100% visibility without the operational overhead of installing and maintaining software agents on every virtual machine or container.
Another critical evolution is the rise of AI-SPM (AI Security Posture Management). As enterprises integrate Large Language Models (LLMs) and AI agents into their applications, CNAPP suites are expanding to protect the AI supply chain. This includes securing model weights, monitoring for “prompt injection” attacks, and ensuring that AI training data is not exposed. Additionally, we are seeing the emergence of “eBPF-native” runtime protection, which allows for deep kernel-level monitoring and threat blocking with negligible performance impact, replacing older, resource-heavy security agents.
How We Selected These Tools
The criteria for selecting these ten suites were rooted in their ability to provide a “Code-to-Cloud” security lifecycle. We prioritized platforms that demonstrated high levels of automation and the ability to reduce “alert fatigue”—a primary pain point for modern SRE and Security teams. Market leadership was evaluated not just by revenue, but by technical innovation in fields like graph-based risk modeling and identity-first security. Each platform was vetted for its multi-cloud support, ensuring consistent policy enforcement across diverse environments like AWS, OCI, and Alibaba Cloud.
Technical robustness was measured by the depth of their integration into the CI/CD pipeline and the sophistication of their runtime detection engines. We also considered the “time-to-value,” favoring platforms that can be deployed via API in minutes to provide an immediate asset inventory. Security and compliance were non-negotiable; every suite on this list supports major frameworks like SOC2, HIPAA, and NIST. Finally, we looked for forward-thinking features such as automated remediation and AI-assisted investigation capabilities that empower teams to respond to threats in real-time.
1. Wiz
Wiz is the current market leader in agentless cloud security, known for its revolutionary “Security Graph.” It provides a unified view of cloud risk by correlating vulnerabilities, misconfigurations, and identity risks without requiring any agents. Its ability to visualize complex attack paths makes it a favorite for teams managing massive, fast-moving cloud estates.
Key Features
The platform utilizes “SideScanning” technology to assess workloads by analyzing the underlying storage volumes via API. It features a comprehensive “Cloud Detection and Response” (CDR) module that monitors for active threats in real-time. The Wiz Security Graph automatically prioritizes risks based on their potential business impact and reachability. It includes built-in CIEM for analyzing permissions and a specialized AI-SPM module for securing AI pipelines. Additionally, it offers automated “Shift Left” capabilities by scanning IaC and container images within the developer workflow.
Pros
Fastest deployment in the industry with near-instant visibility into multi-cloud environments. The graph-based prioritization significantly reduces alert noise for security teams.
Cons
Premium pricing model can be prohibitive for smaller organizations. As an agentless-first platform, it may lack some of the granular “inline” blocking capabilities of agent-based tools.
Platforms and Deployment
SaaS-based platform with agentless API integration across AWS, Azure, GCP, OCI, and Alibaba Cloud.
Security and Compliance
Full support for over 100 compliance frameworks including GDPR, PCI DSS, and FedRAMP.
Integrations and Ecosystem
Extensive integrations with Jira, ServiceNow, Slack, and major CI/CD tools like GitHub Actions and GitLab.
Support and Community
Top-tier enterprise support and a large, active user community of cloud security professionals.
2. Prisma Cloud (Palo Alto Networks)
Prisma Cloud is perhaps the most comprehensive CNAPP on the market, offering both agentless and agent-based protection. It is designed for large-scale enterprises that require deep “Code-to-Cloud” security, spanning from the developer’s IDE to the production runtime environment.
Key Features
The platform offers a robust Web Application and API Protection (WAAP) module integrated directly into the CNAPP. It provides deep container security with eBPF-powered runtime protection and micro-segmentation. Prisma Cloud’s “Supply Chain Security” module tracks every component in the software development lifecycle, ensuring no malicious code is introduced. It features advanced “Identity Threat Detection” and a powerful compliance engine that automates reporting for global regulations. The platform also includes a specialized “AI Security” suite to protect LLM-based applications.
Pros
Provides the broadest feature set of any suite, covering almost every possible cloud security use case. Excellent for highly regulated industries requiring deep compliance controls.
Cons
The platform’s complexity can lead to a steep learning curve for new users. Management of multiple modules can sometimes feel fragmented compared to single-graph solutions.
Platforms and Deployment
Hybrid deployment offering both agentless API scanning and high-performance defenders (agents).
Security and Compliance
Enterprise-grade security with extensive certifications and built-in “Out-of-the-box” compliance templates.
Integrations and Ecosystem
Deeply integrated into the Palo Alto Networks ecosystem (Cortex, Strata) and supports all major clouds.
Support and Community
World-class global support and professional services tailored for Fortune 500 companies.
3. Orca Security
Orca Security pioneered the “SideScanning” approach, which allows for full-stack visibility without agents. It is highly regarded for its ease of use and its “unified risk” approach, which treats the cloud environment as a single entity rather than a collection of separate tools.
Key Features
The platform’s core is its ability to scan the entire cloud estate—including OS, applications, and data—without impacting performance. It features a “Data Security Posture Management” (DSPM) module that identifies sensitive data at risk. Orca includes a “Vulnerability Management” system that prioritizes patches based on exploitability. Its “API Security” module automatically discovers and audits all cloud-based APIs. The platform also offers an AI-powered “search” function that allows users to query their cloud security state using natural language.
Pros
Extremely low operational overhead as there are no agents to manage or update. Excellent at uncovering “shadow IT” and orphaned resources that other tools might miss.
Cons
While it has added runtime capabilities, it is generally seen as stronger in “posture” than in “active threat blocking.” Pricing scales based on the number of cloud assets.
Platforms and Deployment
100% agentless SaaS platform connecting via cloud-native APIs.
Security and Compliance
Strong focus on automated compliance for frameworks like ISO 27001 and SOC2.
Integrations and Ecosystem
Strong integrations with SIEM/SOAR platforms and developer tools like Jenkins and Bitbucket.
Support and Community
Known for highly responsive customer success teams and a straightforward onboarding process.
4. Microsoft Defender for Cloud
Microsoft’s native CNAPP is a powerhouse for organizations heavily invested in the Azure ecosystem, though it has expanded significantly to support AWS and GCP. It provides a unique “Secure Score” that gives organizations a measurable way to track their security maturity over time.
Key Features
The suite includes “Defender for DevOps,” which provides visibility into the security state of GitHub and Azure DevOps repositories. It features “Entra Permissions Management” (CIEM) to manage identities across multi-cloud environments. The “Cloud Workload Protection” modules provide specialized security for SQL databases, storage, and app services. It integrates “Copilot for Security,” allowing users to use Gen-AI to summarize incidents and generate remediation scripts. It also provides a “free” foundational CSPM tier for basic posture checks.
Pros
Seamless, “native” integration for Azure users with one-click enablement. The “Secure Score” provides a very clear roadmap for improving organizational security.
Cons
Multi-cloud features (AWS/GCP) can sometimes feel less mature or more expensive than the Azure-specific features. The interface can be complex due to the breadth of the Microsoft security portfolio.
Platforms and Deployment
Native to Azure; multi-cloud support via Azure Arc and API connectors.
Security and Compliance
Leverages Microsoft’s massive global threat intelligence network for real-time protection.
Integrations and Ecosystem
Deep integration with Microsoft Sentinel (SIEM) and the broader Microsoft 365 security suite.
Support and Community
Backed by Microsoft’s extensive global support network and vast documentation library.
5. CrowdStrike Falcon Cloud Security
CrowdStrike brings its world-renowned EDR (Endpoint Detection and Response) expertise to the cloud. Its CNAPP suite is built on a single-agent architecture that provides unparalleled real-time threat detection and “Indicators of Attack” (IOAs) for cloud workloads.
Key Features
The platform combines “Agentless Snapshot Scanning” for posture with a “Single Agent” for high-fidelity runtime protection. It features a “Cloud Asset Inventory” that discovers all managed and unmanaged cloud resources. The “Identity Protection” module blocks credential-based attacks in real-time. It includes a “Managed Threat Hunting” service (OverWatch) that monitors your cloud environment for advanced adversaries. The “1-Click Remediation” allows teams to fix misconfigurations and vulnerabilities directly from the console.
Pros
Unrivaled runtime detection capabilities; if an attacker is active in your environment, CrowdStrike is likely to find them. Excellent for teams that already use Falcon for endpoint security.
Cons
Achieving full “runtime” value requires the deployment of an agent, which some “agentless-only” teams may resist. The cost can be high for large-scale container environments.
Platforms and Deployment
Hybrid model utilizing a single lightweight agent and API-based scanning.
Security and Compliance
Focuses on “adversary-centric” security, mapping cloud threats to the MITRE ATT&CK framework.
Integrations and Ecosystem
Part of the Falcon platform, offering a unified console for endpoint, identity, and cloud.
Support and Community
Industry-leading support and access to elite threat intelligence reports.
6. Sysdig Secure
Sysdig is the platform of choice for teams that are “Kubernetes-first.” Built on open-source Falco, it provides the deepest possible visibility into container runtimes and Kubernetes system calls, making it essential for complex container orchestration environments.
Key Features
The suite features “Falco” as its core engine for real-time threat detection in containers. It provides “Risk-Based Prioritization” that filters vulnerabilities based on what is actually “in-use” at runtime. Sysdig includes “Kubernetes Security Posture Management” (KSPM) to audit cluster configurations and network policies. Its “Cloud Detection and Response” (CDR) module provides a forensic “time-machine” to reconstruct security incidents. It also features “Just-in-Time” (JIT) access management for developers to reduce the risk of permanent over-privileged roles.
Pros
The most advanced container and Kubernetes security on the market. Excellent at reducing vulnerability noise by identifying “active” versus “dormant” code.
Cons
Can be more technically demanding than general-purpose CNAPPs. While it supports multi-cloud, its primary strength remains in the Kubernetes layer.
Platforms and Deployment
Agent-based (eBPF) and agentless deployment for K8s, Serverless (Fargate), and Cloud APIs.
Security and Compliance
Built-in compliance for Kubernetes-specific benchmarks (CIS) and standard frameworks.
Integrations and Ecosystem
Native integrations with Prometheus, Grafana, and all major Kubernetes distributions (EKS, GKE, AKS).
Support and Community
Strong roots in the open-source community and excellent technical support for DevOps teams.
7. SentinelOne Singularity Cloud
SentinelOne has rapidly expanded its “Singularity” platform into a full CNAPP suite. It is known for its “Autonomous AI” which can detect and remediate threats without human intervention, making it a powerful tool for understaffed security teams.
Key Features
The platform features an “Offensive Security Engine” that continuously simulates attacks to find exploitable paths. It provides a “Verified Exploit Paths” methodology that proves a risk is real before alerting the team. The “Purple AI” assistant helps security analysts investigate alerts using conversational language. It includes “Secret Scanning” across code repositories to prevent credential leakage. The runtime protection uses “Storyline” technology to correlate all events into a single, understandable forensic trail.
Pros
The autonomous remediation capabilities are a significant force-multiplier for lean teams. Very high automation levels for both discovery and response.
Cons
The offensive security simulations require careful configuration to avoid interference with development environments. Newer to the “posture” market compared to Wiz or Prisma.
Platforms and Deployment
SaaS platform with options for both agentless scanning and high-performance agents.
Security and Compliance
Strong emphasis on “Data Security” and compliance for sensitive workloads.
Integrations and Ecosystem
Integrates with the Singularity XDR ecosystem and major IT service management (ITSM) tools.
Support and Community
Offers a 24/7 “Vigilance” MDR service for organizations that want outsourced cloud monitoring.
8. Aqua Security
Aqua Security is a pioneer in the “Cloud-Native” space, focusing heavily on the “Shift Left” philosophy. It is designed to stop attacks before they ever reach production by enforcing strict security policies throughout the entire CI/CD lifecycle.
Key Features
The suite includes a powerful “Supply Chain Security” module that audits everything from source code to the build environment. It features “Zero-Drift” technology for containers, which prevents any unauthorized changes to a running container image. Aqua provides “KubeEnforcer” to manage Kubernetes admission controllers and prevent risky deployments. Its “Lightning Agentless” scanning provides rapid visibility into cloud accounts. The platform also includes a dedicated module for “Serverless” security (Lambda, Cloud Functions).
Pros
Unbeatable at “preventative” security; its ability to enforce immutable workloads is a key differentiator. Strong focus on the developer experience and GitOps workflows.
Cons
The “preventative” focus can sometimes be seen as rigid or restrictive for teams used to more flexible cloud environments. Can require more “upfront” policy configuration.
Platforms and Deployment
Cloud-native platform with agents for runtime and API-based scanning for posture.
Security and Compliance
Highly detailed compliance reporting for containerized and regulated workloads.
Integrations and Ecosystem
Excellent support for the entire CNCF landscape and all major container registries.
Support and Community
Deep technical expertise in container security and a supportive enterprise customer base.
9. Check Point CloudGuard
Check Point’s CloudGuard is a mature, enterprise-grade CNAPP that excels in multi-cloud network security and compliance. It is the logical choice for organizations that need to extend their on-premises Check Point firewall policies into the cloud.
Key Features
The platform features “High-Fidelity Posture Management” that uses a contextual graph to prioritize risks. It includes a powerful “Cloud Network Security” module that provides automated, industry-leading threat prevention. Its “AppSec” module utilizes machine learning to protect web applications and APIs without manual tuning. CloudGuard offers “Intelligence and Response” (CDR) to hunt for threats using cloud-native logs. It also features a “Workload Protection” module that secures containers and serverless functions across multi-cloud.
Pros
Outstanding network security and firewall integration. The platform’s “Governance and Compliance” features are some of the most advanced for large, regulated entities.
Cons
The user interface can feel more “traditional” and less “developer-first” compared to newer startups. Integration with non-Check Point ecosystems may require more effort.
Platforms and Deployment
Hybrid SaaS platform supporting public, private, and hybrid cloud environments.
Security and Compliance
World-class threat intelligence from Check Point Research (CPR).
Integrations and Ecosystem
Deeply integrated with the Check Point Infinity architecture and major cloud providers.
Support and Community
Extensive global support infrastructure and a long history of serving enterprise customers.
10. Lacework (by Fortinet)
Lacework, now part of the Fortinet ecosystem, uses a unique “behavioral” approach to cloud security. Instead of relying purely on static rules, it uses machine learning to “learn” what is normal for your environment and alert you only when something deviates.
Key Features
The platform’s “Polygraph” technology visualizes all relationships and communications between cloud entities. It features automated “Anomaly Detection” that can spot zero-day attacks or compromised credentials. Lacework includes “IaC Scanning” to fix misconfigurations before they are deployed. It provides a “Unified Search” capability for cloud forensic investigations. The “Identity Security” module identifies over-privileged roles and “toxic combinations” of permissions. It also features a comprehensive vulnerability scanner for hosts, containers, and serverless.
Pros
Drastically reduces alert volume by focusing on “deviations from normal” rather than thousands of minor misconfigurations. Excellent for fast-scaling, complex environments.
Cons
The behavioral learning period (baselining) means the platform may not be fully effective on day one. Now that it is part of Fortinet, the future integration roadmap is still evolving.
Platforms and Deployment
SaaS-based behavioral platform with both agentless and agent-based options.
Security and Compliance
Automates compliance across dozens of frameworks with historical “time-travel” reporting.
Integrations and Ecosystem
Strong integrations with Snowflake for data analysis and major developer platforms.
Support and Community
Transitioning into Fortinet’s massive global support network, offering increased scale.
Comparison Table
| Tool Name | Best For | Deployment | Key Differentiator | Standout Feature | Rating |
| 1. Wiz | Multi-Cloud/Fast ROI | Agentless | Security Graph | Attack Path Analysis | 4.8/5 |
| 2. Prisma Cloud | Large Enterprise | Hybrid | Feature Breadth | Code-to-Cloud Suite | 4.7/5 |
| 3. Orca Security | Low Overhead | Agentless | SideScanning | API/Data Security | 4.6/5 |
| 4. Defender Cloud | Azure Ecosystem | Native/Arc | Microsoft Native | Secure Score | 4.5/5 |
| 5. CrowdStrike | Runtime Detection | Hybrid | EDR Pedigree | Indicators of Attack | 4.7/5 |
| 6. Sysdig Secure | Kubernetes Teams | Agent (eBPF) | Falco-Based | Deep K8s Forensics | 4.6/5 |
| 7. SentinelOne | Autonomous SOC | Hybrid | Offensive Engine | Purple AI Assistant | 4.5/5 |
| 8. Aqua Security | Preventative Security | Hybrid | Zero-Drift K8s | Supply Chain Security | 4.4/5 |
| 9. CloudGuard | Network Focus | Hybrid | Firewall Heritage | Network Topology | 4.3/5 |
| 10. Lacework | Anomaly Detection | Hybrid | Polygraph ML | Behavioral Analysis | 4.4/5 |
Evaluation & Scoring of Security Posture Management Suites
The scoring below is a comparative model intended to help shortlisting. Each criterion is scored from 1–10, then a weighted total from 0–10 is calculated using the weights listed. These are analyst estimates based on typical fit and common workflow requirements, not public ratings.
Weights:
- Core features – 25%
- Ease of use – 15%
- Integrations & ecosystem – 15%
- Security & compliance – 10%
- Performance & reliability – 10%
- Support & community – 10%
- Price / value – 15%
| Tool Name | Core (25%) | Ease (15%) | Integrations (15%) | Security (10%) | Performance (10%) | Support (10%) | Value (15%) | Weighted Total |
| 1. Wiz | 10 | 10 | 9 | 9 | 10 | 9 | 8 | 9.35 |
| 2. Prisma Cloud | 10 | 7 | 10 | 10 | 9 | 10 | 7 | 8.95 |
| 3. Orca Security | 9 | 10 | 9 | 9 | 9 | 9 | 9 | 9.05 |
| 4. Defender Cloud | 9 | 9 | 8 | 9 | 9 | 10 | 10 | 9.10 |
| 5. CrowdStrike | 9 | 8 | 9 | 10 | 10 | 9 | 8 | 8.95 |
| 6. Sysdig Secure | 9 | 7 | 10 | 10 | 10 | 8 | 8 | 8.75 |
| 7. SentinelOne | 9 | 8 | 8 | 9 | 9 | 9 | 9 | 8.70 |
| 8. Aqua Security | 8 | 8 | 9 | 10 | 9 | 9 | 8 | 8.60 |
| 9. CloudGuard | 9 | 7 | 8 | 10 | 9 | 9 | 8 | 8.50 |
| 10. Lacework | 8 | 9 | 8 | 9 | 9 | 8 | 9 | 8.55 |
How to interpret the scores:
- Use the weighted total to shortlist candidates, then validate with a pilot.
- A lower score can mean specialization, not weakness.
- Security and compliance scores reflect controllability and governance fit, because certifications are often not publicly stated.
- Actual outcomes vary with assembly size, team skills, templates, and process maturity.
Which CNAPP Suite Is Right for You?
Solo / Freelancer
Cloud security suites of this magnitude are generally over-engineered for solo developers. However, if you are managing a small production app on Azure, the “Free” tier of Microsoft Defender for Cloud provides essential posture checks at no cost. For AWS or GCP users, a simple open-source tool like Prowler or Aqua Trivy may be more appropriate for a single-person operation.
SMB
Small to medium businesses should look for “agentless” simplicity to avoid the burden of infrastructure management. Wiz or Orca Security are the standout choices here, as they provide immediate value with minimal configuration. If budget is a major concern, Microsoft Defender offers the best pricing flexibility for teams already within the Azure or Office 365 ecosystem.
Mid-Market
Organizations in this tier usually have a dedicated DevSecOps person or a small security team. CrowdStrike Falcon Cloud Security or SentinelOne are excellent choices because they combine posture management with high-fidelity runtime protection, acting as a force-multiplier for a small team that needs to detect and respond to threats quickly.
Enterprise
For large, multi-national corporations with complex compliance needs, Prisma Cloud is the gold standard. Its ability to cover everything from code to network security in a single platform is unmatched. Alternatively, if the enterprise is “Kubernetes-heavy,” Sysdig Secure provides the deep forensic visibility required for high-compliance container environments.
Budget vs Premium
If the primary goal is cost-efficiency, Microsoft Defender for Cloud and Orca Security offer competitive models tailored to usage. On the premium end, Wiz and Prisma Cloud command higher prices but offer more advanced features like attack path graphing and full supply-chain security that justify the investment for high-risk environments.
Feature Depth vs Ease of Use
Wiz is the winner for ease of use, providing a polished, graph-based experience that makes sense even to non-security specialists. Prisma Cloud and Sysdig Secure offer much more “feature depth” but require a dedicated engineer to tune the policies and manage the various modules effectively.
Integrations & Scalability
Scalability is a core strength of all these tools, but Prisma Cloud and Check Point CloudGuard have the edge in integrating with “hybrid” legacy environments. For cloud-native scalability, Wiz and Lacework are designed to handle millions of assets without breaking the UI or slowing down the scanning engine.
Security & Compliance Needs
Every tool on this list is “Compliance-Ready.” However, if you are in a highly specialized field like Finance or Defense, Check Point CloudGuard and Prisma Cloud offer the most granular policy customization to meet strict regulatory audits and “Zero Trust” mandates.
Frequently Asked Questions (FAQs)
1. What is the difference between CSPM and CNAPP?
CSPM (Cloud Security Posture Management) is a subset of CNAPP. CSPM focuses purely on misconfigurations and compliance, while CNAPP is an integrated suite that also includes workload protection (CWPP), identity management (CIEM), and application security.
2. Is agentless security as good as agent-based security?
Agentless security is excellent for visibility and finding misconfigurations. However, agent-based security is still superior for “active blocking” of threats in real-time, as an agent lives inside the workload and can see system calls that an API scanner cannot.
3. Does CNAPP replace my SIEM?
No, a CNAPP provides specialized cloud security signals, but a SIEM (like Splunk or Microsoft Sentinel) is still needed to correlate those signals with logs from your office network, firewalls, and identity providers for a full organizational view.
4. How long does it take to implement a CNAPP suite?
Agentless platforms like Wiz or Orca can be implemented in under 30 minutes via API. Agent-based platforms can take weeks or months to fully roll out, depending on the number of clusters and virtual machines you need to cover.
5. Can CNAPP prevent ransomware in the cloud?
Yes, suites with strong “Runtime Protection” (like CrowdStrike or Sysdig) can detect and block the behavioral patterns of ransomware, such as unauthorized file encryption or lateral movement across your cloud network.
6. What is “Attack Path Analysis”?
Attack Path Analysis is a feature that uses graph technology to show you exactly how an attacker could combine a minor vulnerability, an over-privileged identity, and a public-facing port to reach your most sensitive data.
7. Do I need a CNAPP if I only use AWS?
Even if you only use one cloud provider, the native tools (like AWS Security Hub) are often siloed. A CNAPP provides a much deeper, unified view of your applications, identities, and code that native tools often miss.
8. Can these tools scan my source code for secrets?
Yes, modern “Code-to-Cloud” CNAPPs like Aqua, Prisma Cloud, and Wiz include modules that scan GitHub/GitLab repositories for hardcoded API keys, passwords, and other sensitive secrets.
9. What is eBPF and why is it important for cloud security?
eBPF is a technology that allows security tools to monitor the Linux kernel without needing a heavy agent. It is important because it provides deep security visibility with almost zero impact on the application’s performance.
10. How much does a CNAPP suite cost?
Pricing is typically based on the number of “Workloads” (VMs or containers) or the total number of cloud resources. For a mid-sized enterprise, a CNAPP suite can range from $20,000 to over $200,000 per year depending on the feature set.
Conclusion
As we navigate the complexities of the current cloud landscape, the transition from fragmented security tools to a holistic CNAPP suite is no longer optional. The speed of cloud deployment and the sophistication of modern adversaries demand a security posture that is as dynamic and interconnected as the infrastructure it protects. Implementing a CNAPP is about more than just checking a compliance box; it is about building a proactive, risk-aware culture where security is woven into the very fabric of the development lifecycle. By consolidating posture, workload, and identity security into a single source of truth, organizations can move past the noise of thousands of alerts and focus on the specific threats that matter. Whether you choose a graph-native innovator or an established enterprise giant, the key to success lies in choosing a partner that aligns with your technical maturity and your long-term vision for a secure, resilient cloud future.