Introduction
Post-Quantum Cryptography (PQC) migration tools are specialized software solutions designed to identify, assess, and replace cryptographic algorithms that are vulnerable to being broken by future cryptanalytically relevant quantum computers (CRQCs). The urgency for these tools has escalated due to the “Harvest Now, Decrypt Later” threat, where adversaries collect encrypted data today to decrypt it once powerful quantum hardware becomes available. These tools facilitate the transition from classical public-key standards like RSA and ECC to NIST-standardized quantum-resistant algorithms such as ML-KEM (Kyber), ML-DSA (Dilithium), and SLH-DSA (SPHINCS+).
For enterprise leaders, PQC migration is not merely a patch update but a multi-year architectural transformation. These tools provide the necessary visibility through Cryptographic Bill of Materials (CBOM) and enable “crypto-agility”—the ability to swap algorithms without re-engineering entire systems. Selecting the right toolset is critical for maintaining long-term data confidentiality and regulatory compliance in a landscape where quantum readiness is becoming a mandatory audit requirement.
- Best for: Financial institutions, government contractors, healthcare providers, and critical infrastructure operators managing long-lived data.
- Not ideal for: Small businesses with low-sensitivity data or systems with very short data lifecycles that do not require multi-decade protection.
Key Trends in PQC Migration Tools
- Rise of the CBOM: The Cryptographic Bill of Materials has become a standard requirement for software supply chain transparency, listing every algorithm and key length used.
- Hybrid Cryptographic Suites: Tools are increasingly supporting “dual-stack” or hybrid modes, combining classical and PQC algorithms to ensure security against both current and future threats.
- AI-Assisted Code Refactoring: Modern scanners now use machine learning to identify hardcoded cryptographic calls in legacy code and suggest PQC-ready replacements.
- Automated Algorithm Rotation: High-end tools allow for policy-based algorithm switching at the network layer without requiring application redeployment.
- Continuous Posture Monitoring: The shift from one-time “readiness audits” to real-time monitoring of cryptographic health across cloud and on-premise environments.
- Standardization Alignment: Tools are now natively supporting the finalized FIPS 203, 204, and 205 standards released by NIST.
How We Selected These Tools
- Algorithm Compliance: Verification that the tools support finalized NIST PQC standards (ML-KEM, ML-DSA).
- Discovery Depth: Ability of the tool to find “hidden” cryptography in compiled binaries, third-party SDKs, and firmware.
- Remediation Capability: Evaluation of whether the tool merely identifies risks or provides active paths for algorithm replacement and testing.
- Crypto-Agility Support: Assessment of how well the tool enables future-proofing against new cryptographic vulnerabilities.
- Integration Maturity: Strength of the tool’s connectors with existing PKI, DevOps pipelines, and Cloud KMS providers.
- Enterprise Scalability: Performance reliability when scanning global infrastructures with thousands of applications.
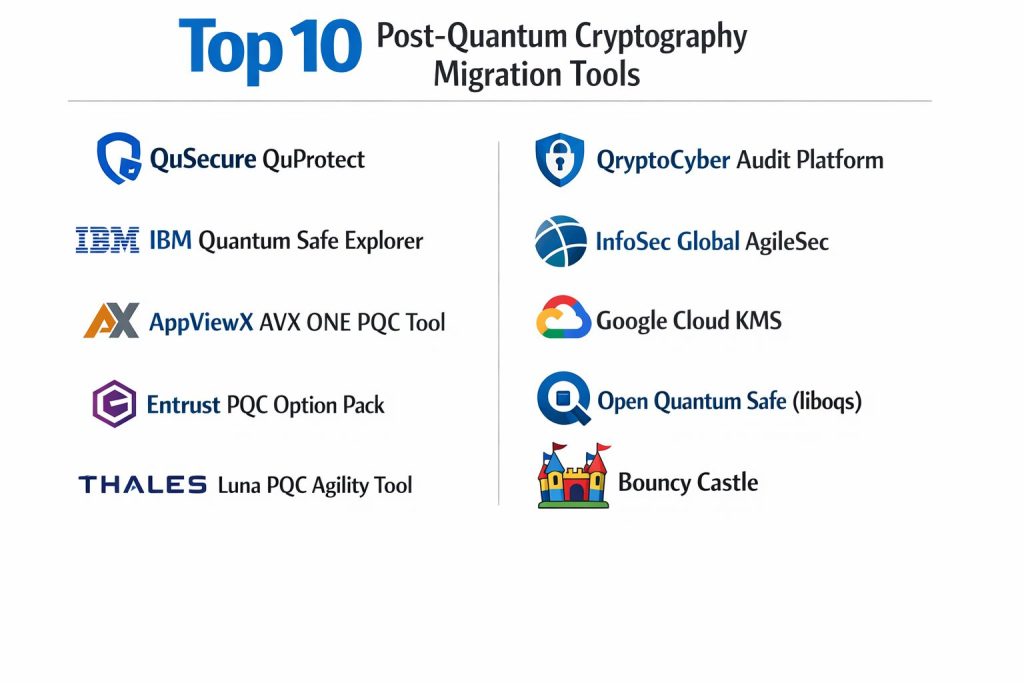
Top 10 Post-Quantum Cryptography Migration Tools
1. QuSecure QuProtect
QuProtect is a comprehensive end-to-end PQC orchestration platform that provides real-time remediation and crypto-agility at the network layer.
Key Features
- Dynamic Algorithm Rotation: Switches algorithms via policy without changing application code.
- Quantum-Safe Tunneling: Protects data-in-transit using hybrid classical/PQC tunnels.
- CBOM Generation: Automatically inventories cryptographic assets and generates compliance reports.
- Centralized Policy Management: Orchestrates crypto-agility across cloud, edge, and on-premise sites.
- Side-Channel Protection: Implements algorithms with protections against hardware-level attacks.
Pros
- Allows for immediate PQC protection without requiring a full application “rip-and-replace.”
- Strong compliance mapping to CNSA 2.0 and NIST guidelines.
Cons
- Higher cost compared to simple scanning tools due to its active remediation features.
- Requires careful integration into the networking stack to avoid latency issues.
Platforms / Deployment
- Cloud / On-Premise / Edge
- SaaS & Software Appliance
Security & Compliance
- FIPS 140-3 compliant, MFA, and role-based access control for policy changes.
Integrations & Ecosystem
Integrates with major load balancers, firewalls, and Cloud Service Providers (CSPs) to act as a security overlay.
Support & Community
High-level enterprise support with dedicated transition specialists and architectural reviews.
2. IBM Quantum Safe Explorer
A specialized discovery tool from IBM’s Quantum Safe portfolio designed to scan source code and binaries for cryptographic vulnerabilities.
Key Features
- Deep Binary Scanning: Identifies hardcoded keys and legacy algorithms within compiled software.
- Vulnerability Prioritization: Ranks cryptographic risks based on data sensitivity and exposure.
- Dependency Mapping: Visualizes how cryptographic calls flow through complex software supply chains.
- NIST-Aligned Reporting: Generates audit-ready dashboards showing quantum readiness scores.
- Continuous Integration: Plugs into CI/CD pipelines to prevent new “quantum-weak” code from reaching production.
Pros
- Leverages IBM’s extensive research and leadership in the PQC standards process.
- Exceptional accuracy in finding hidden crypto in legacy enterprise applications.
Cons
- Primarily focused on discovery; requires other IBM services for full remediation.
- Best suited for very large organizations with complex, custom-built software stacks.
Platforms / Deployment
- Hybrid Cloud
- SaaS
Security & Compliance
- Enterprise-grade security protocols managed within the IBM Cloud ecosystem.
Integrations & Ecosystem
Strongest when paired with IBM’s broader “Quantum Safe” advisory and management services.
Support & Community
Direct access to IBM’s Cryptography Center of Excellence and global consulting teams.
3. AppViewX AVX ONE PQC Tool
An automated assessment and inventory tool that focuses on certificate lifecycle management and PQC readiness.
Key Features
- Automated Crypto Inventory: Scans network endpoints to identify all SSL/TLS certificates and their algorithms.
- PQC Readiness Scoring: Assigns a risk score to every certificate based on its quantum vulnerability.
- Quantum-Ready PKI: Facilitates the issuance of PQC and hybrid certificates through integrated CAs.
- Crypto-Agile Orchestration: Automates the replacement of certificates across thousands of devices.
- Compliance Dashboards: Provides real-time visibility for auditors into the PQC migration progress.
Pros
- Excellent for organizations already using AppViewX for Certificate Lifecycle Management.
- Streamlines the transition of PKI, which is often the most vulnerable part of an enterprise.
Cons
- Less focus on application-level code scanning than some competitors.
- Requires a mature PKI environment to realize its full automation value.
Platforms / Deployment
- Windows / Linux / Cloud
- SaaS
Security & Compliance
- RBAC, MFA, and comprehensive audit logs for all certificate operations.
Integrations & Ecosystem
Integrates natively with major CAs (DigiCert, Sectigo) and cloud KMS providers.
Support & Community
Professional enterprise support and a robust library of PQC transition whitepapers.
4. Entrust PQC Option Pack
A suite of tools and hardware-accelerated libraries designed to make Entrust HSMs and PKI systems quantum-safe.
Key Features
- HSM-Based PQC: Generates and protects quantum-resistant keys within FIPS-validated hardware.
- SDK for PQC: Provides developers with libraries to build quantum-resistant digital signatures.
- Hybrid Certificate Support: Issues certificates that work with both legacy and PQC-aware clients.
- Cryptographic Health Check: A professional service tool that inventories an organization’s PKI state.
- Firmware-Level Agility: Allows for upgrading HSM algorithms as standards evolve.
Pros
- Ideal for securing the “Root of Trust” using high-assurance hardware.
- Backed by Entrust’s deep expertise in global PKI and identity standards.
Cons
- Dependent on purchasing or leasing specific Entrust hardware (HSMs).
- Focused more on the infrastructure layer than the application code layer.
Platforms / Deployment
- On-Premise / HSM-as-a-Service
- Hardware/Software Hybrid
Security & Compliance
- Rooted in FIPS 140-3 Level 3 hardware security standards.
Integrations & Ecosystem
Seamlessly integrates with the Entrust nShield ecosystem and enterprise CAs.
Support & Community
Dedicated high-priority support for enterprise and government clients.
5. Thales Luna PQC Agility Tool
A set of software and firmware updates for Thales Luna HSMs that enable testing and deployment of PQC algorithms.
Key Features
- Algorithm Evaluation Mode: Allows users to test PQC performance in a secure “sandbox” on the HSM.
- Quantum Random Number Generation: Integrates with QRNG for high-entropy key creation.
- High-Speed Encryption: Field-upgradeable FPGAs support PQC for data-in-motion.
- Crypto-Agile APIs: Standardized interfaces (PKCS#11) for implementing PQC in custom apps.
- Hybrid Key Exchange: Supports the transition from classical DH/ECDH to quantum-safe key encapsulation.
Pros
- Enables a gradual, low-risk testing path for existing Thales customers.
- High-performance hardware acceleration for computationally heavy PQC algorithms.
Cons
- Limited to the Thales hardware ecosystem.
- Primarily a tool for technical teams rather than a high-level executive dashboard.
Platforms / Deployment
- On-Premise / Hybrid Cloud
- Hardware Appliance
Security & Compliance
- Military-grade hardware security with extensive compliance certifications.
Integrations & Ecosystem
Deeply integrated with Thales CipherTrust Data Security Platform.
Support & Community
Global enterprise support and a large partner ecosystem for PQC implementation.
6. QryptoCyber Audit Platform
A startup-driven platform specifically designed to automate the discovery and financial quantification of quantum risk.
Key Features
- Automated CBOM Generation: Creates a detailed inventory of all cryptographic assets across the enterprise.
- Financial Risk Quantification: Translates cryptographic vulnerabilities into potential financial loss metrics.
- Compliance Mapping: Maps PQC readiness to specific regulatory frameworks like HIPAA or GDPR.
- Executive Dashboards: Simplifies complex technical data for C-level decision-makers.
- Prioritization Engine: Identifies which systems need PQC migration first based on business impact.
Pros
- Unique focus on the “business case” for PQC migration through financial metrics.
- Modern, intuitive interface designed for ease of use by risk officers.
Cons
- Newer player in the market compared to established giants like IBM or Thales.
- Less focused on the actual “execution” or remediation of the cryptography.
Platforms / Deployment
- SaaS / Cloud-Native
- Managed Service
Security & Compliance
- Standard cloud security protocols and encrypted data storage.
Integrations & Ecosystem
Connects to cloud APIs and internal code repositories for continuous scanning.
Support & Community
Personalized support for early adopters and detailed risk assessment reporting.
7. InfoSec Global AgileSec
AgileSec is a platform that provides total visibility and control over an organization’s cryptographic landscape.
Key Features
- AgileSec Scanner: Discovers cryptographic use in applications, servers, and network devices.
- Cryptographic Policy Engine: Defines and enforces which algorithms are allowed across the enterprise.
- AgileSec SDK: A multi-platform library that allows developers to easily implement PQC algorithms.
- Discovery as a Service: Managed service for finding and cataloging cryptographic assets.
- Hybrid Remediation: Supports the parallel use of RSA/ECC and PQC during the migration phase.
Pros
- Highly effective at finding “shadow” cryptography that standard security tools miss.
- The SDK is designed to be “crypto-agile,” making future algorithm swaps easier.
Cons
- Implementation of the SDK requires significant development effort for legacy apps.
- Can be complex to configure for massive, heterogeneous environments.
Platforms / Deployment
- Windows / Linux / Cloud
- Hybrid
Security & Compliance
- Policy-based enforcement ensures adherence to internal and external standards.
Integrations & Ecosystem
Strong partnerships with system integrators and cloud providers for large-scale rollouts.
Support & Community
Expert consulting services and a deep technical knowledge base.
8. Google Cloud KMS (PQC Features)
Google Cloud’s Key Management Service now includes native tools for creating and managing quantum-safe keys.
Key Features
- ML-KEM Key Exchange: Native support for the NIST standard for quantum-safe key exchange.
- Quantum-Safe Digital Signatures: Allows for the creation of ML-DSA signatures for data integrity.
- Cloud KMS Inventory: Built-in tools to inventory and rotate keys used across GCP services.
- Hybrid TLS Support: Protects traffic between users and Google Cloud using PQC-hybrid protocols.
- Tink Library Integration: Open-source cryptographic library that simplifies PQC usage for developers.
Pros
- Easiest entry point for organizations already fully invested in the Google Cloud ecosystem.
- Beneficiary of Google’s world-class security research and early adoption of PQC.
Cons
- Limited to assets and data within the Google Cloud Platform.
- Lacks the deep “discovery” features for on-premise legacy systems found in other tools.
Platforms / Deployment
- Cloud-Native (GCP)
- SaaS
Security & Compliance
- Managed by Google’s high-assurance infrastructure and global compliance team.
Integrations & Ecosystem
Perfectly integrated with all GCP services and the BoringSSL library.
Support & Community
Standard GCP support tiers and extensive documentation for developers.
9. Open Quantum Safe (liboqs)
The premier open-source project for prototyping and experimenting with quantum-resistant cryptography.
Key Features
- liboqs C Library: A comprehensive collection of all major PQC algorithm implementations.
- OQS-OpenSSL Provider: Allows the world’s most popular crypto library to use PQC algorithms.
- Prototype Integrations: Pre-built forks of OpenSSH and BoringSSL for testing quantum-safe connections.
- Benchmarking Suite: Tools to measure the performance impact of PQC on your specific hardware.
- Community-Driven Updates: Rapidly updated to include the latest algorithm tweaks and standards.
Pros
- Completely free and open-source; the foundation for many commercial PQC products.
- Essential for developers and researchers who need to “get their hands dirty” with the code.
Cons
- No formal enterprise support; requires high internal technical expertise.
- Not a “commercial product,” so it lacks executive dashboards and management UIs.
Platforms / Deployment
- Linux / macOS / Windows / Source Code
- Local / CI-CD
Security & Compliance
- Subject to intense peer review by the global cryptographic community.
Integrations & Ecosystem
Acts as the engine for many other projects in the Post-Quantum Cryptography Alliance (PQCA).
Support & Community
Extremely active developer community on GitHub and Discord.
10. Bouncy Castle (Java/C# PQC APIs)
A widely used, lightweight cryptographic API that has been at the forefront of providing PQC support for Java and .NET.
Key Features
- Comprehensive PQC Support: Early and complete implementations of NIST finalists (Kyber, Dilithium).
- FIPS-Certified Versions: Offers a certified path for organizations requiring strict compliance.
- Low-Level Control: Provides granular control over algorithm parameters for expert developers.
- Hybrid Support: Tools to easily wrap classical keys with PQC layers.
- Cross-Platform Compatibility: Identical API support across Java and .NET environments.
Pros
- The standard for Java-based enterprise applications; very easy to drop into existing projects.
- Long history of reliability and rapid response to security vulnerabilities.
Cons
- Requires manual development work; it is a library, not an automated scanning tool.
- No built-in discovery or management dashboard features.
Platforms / Deployment
- Java Virtual Machine / .NET Framework
- Embedded / Server / Mobile
Security & Compliance
- Trusted by governments and banks worldwide; offers FIPS 140-2/3 certified modules.
Integrations & Ecosystem
Integrates with almost any Java or .NET build system (Maven, Gradle, NuGet).
Support & Community
Strong community support and options for commercial support through partners like Crypto Workshop.
Comparison Table
| Tool Name | Best For | Platform(s) Supported | Deployment | Standout Feature | Public Rating |
| 1. QuSecure | Enterprise Remediate | Win, Lin, Cloud | SaaS/Appliance | Dynamic Remediation | N/A |
| 2. IBM Explorer | Legacy Discovery | Cloud, Hybrid | SaaS | Deep Binary Scanning | N/A |
| 3. AppViewX | PKI / Certificates | Win, Lin, Cloud | SaaS | Readiness Scoring | N/A |
| 4. Entrust | Root of Trust | On-Premise, HSM | Hardware/SaaS | HSM-based PQC | N/A |
| 5. Thales | Performance Test | On-Premise | Hardware | FPGA-based Agility | N/A |
| 6. QryptoCyber | Risk Quantification | Cloud, Managed | SaaS | Financial Risk Scoring | N/A |
| 7. InfoSec Global | Crypto Policy | Win, Lin, Cloud | Hybrid | AgileSec SDK | N/A |
| 8. Google Cloud | GCP Native Users | Google Cloud | SaaS | ML-KEM Native Support | N/A |
| 9. Open Quantum Safe | Developers/Labs | Lin, Mac, Win | Source Code | liboqs Libraries | N/A |
| 10. Bouncy Castle | App Development | Java, .NET | Embedded/Server | FIPS-certified APIs | N/A |
Evaluation & Scoring of PQC Migration Tools
The scoring below is a comparative model intended to help shortlisting. Each criterion is scored from 1–10, then a weighted total from 0–10 is calculated using the weights listed. These are analyst estimates based on typical fit and common workflow requirements, not public ratings.
Weights:
- Core features – 25%
- Ease of use – 15%
- Integrations & ecosystem – 15%
- Security & compliance – 10%
- Performance & reliability – 10%
- Support & community – 10%
- Price / value – 15%
| Tool Name | Core (25%) | Ease (15%) | Integrations (15%) | Security (10%) | Performance (10%) | Support (10%) | Value (15%) | Total |
| 1. QuSecure | 10 | 7 | 9 | 9 | 8 | 8 | 7 | 8.45 |
| 2. IBM Explorer | 9 | 6 | 8 | 10 | 9 | 9 | 6 | 8.05 |
| 3. AppViewX | 8 | 8 | 10 | 8 | 9 | 8 | 8 | 8.40 |
| 4. Entrust | 9 | 5 | 7 | 10 | 10 | 9 | 6 | 7.80 |
| 5. Thales | 8 | 5 | 7 | 10 | 10 | 9 | 6 | 7.55 |
| 6. QryptoCyber | 7 | 9 | 7 | 7 | 8 | 7 | 8 | 7.40 |
| 7. InfoSec Global | 9 | 6 | 8 | 8 | 8 | 8 | 7 | 7.60 |
| 8. Google Cloud | 7 | 9 | 10 | 9 | 10 | 8 | 9 | 8.45 |
| 9. Open Quantum Safe | 10 | 2 | 8 | 8 | 9 | 6 | 10 | 7.60 |
| 10. Bouncy Castle | 9 | 4 | 9 | 9 | 9 | 7 | 10 | 8.00 |
How to interpret the scores:
- Use the weighted total to shortlist candidates, then validate with a pilot.
- A lower score can mean specialization, not weakness.
- Security and compliance scores reflect controllability and governance fit, because certifications are often not publicly stated.
- Actual outcomes vary with assembly size, team skills, templates, and process maturity.
Which PQC Migration Tool Is Right for You?
Solo / Developer
If you are a developer tasked with prototyping, Open Quantum Safe and Bouncy Castle are your best options. They provide the raw libraries needed to understand how PQC impacts your code without any upfront cost.
SMB
For smaller organizations that mostly use cloud services, Google Cloud KMS or AppViewX offer the most straightforward path. They focus on the high-level management of keys and certificates, which is where most of your risk lies.
Mid-Market
Mid-sized firms with a mix of cloud and on-premise infrastructure should look at QuSecure. Its ability to add a quantum-safe layer without rewriting every internal app provides a high ROI and faster protection timeline.
Enterprise
Global enterprises with decades of technical debt require a dual approach: IBM Quantum Safe Explorer for deep discovery of legacy code, and Entrust or Thales for securing the high-assurance root of trust in their data centers.
Frequently Asked Questions
1. When will quantum computers break current encryption?
Estimates vary, but many experts point to a “Q-Day” as early as 2029-2032. However, “Harvest Now, Decrypt Later” makes it a threat to long-lived data today.
2. What is a Cryptographic Bill of Materials (CBOM)?
A CBOM is an inventory of every cryptographic asset in a software system, including the algorithms, key lengths, and where they are located.
3. Do PQC algorithms make my systems slower?
Yes, most PQC algorithms have larger key sizes and higher computational requirements, which is why performance testing is a critical part of migration.
4. Can I just wait for my vendors to update their software?
While vendors will update, you are still responsible for your custom code and the “blind spots” in your internal infrastructure that vendors don’t see.
5. What is “Crypto-Agility”?
It is the architectural ability to quickly switch from one cryptographic algorithm to another without major changes to the system’s design.
6. Is hybrid encryption really safer?
Yes, it combines a classical algorithm (like RSA) with a PQC one. If one is broken, the other still provides a layer of protection.
7. How do I start a PQC migration?
The first step is always Discovery. You cannot protect what you don’t know exists. Start by generating a CBOM of your critical systems.
8. Are NIST PQC standards finalized?
Yes, NIST finalized the first three standards (ML-KEM, ML-DSA, and SLH-DSA) in late 2024, providing a stable target for migration tools.
9. Will I need new hardware for PQC?
In many cases, yes. Older HSMs and network devices may not have the memory or processing power to handle the larger PQC keys and signatures.
10. Is PQC the same as Quantum Key Distribution (QKD)?
No. PQC is math-based software encryption that runs on classical computers; QKD is physics-based hardware security that requires fiber-optic links.
Conclusion
The migration to Post-Quantum Cryptography is perhaps the most significant security overhaul in the history of modern computing. The transition has moved from a research curiosity to a board-level strategic priority. Success in this new era depends on moving beyond reactive patching to a proactive, automated, and crypto-agile security posture. By leveraging specialized tools for discovery, such as IBM Explorer, and orchestration platforms like QuProtect, organizations can systematically reduce their exposure to the quantum threat. The key is to start the inventory process immediately, as the average enterprise migration is predicted to take between 5 and 12 years. I suggest starting with a pilot project focused on your most sensitive, long-lived data assets to benchmark performance and establish a repeatable migration workflow.