Introduction
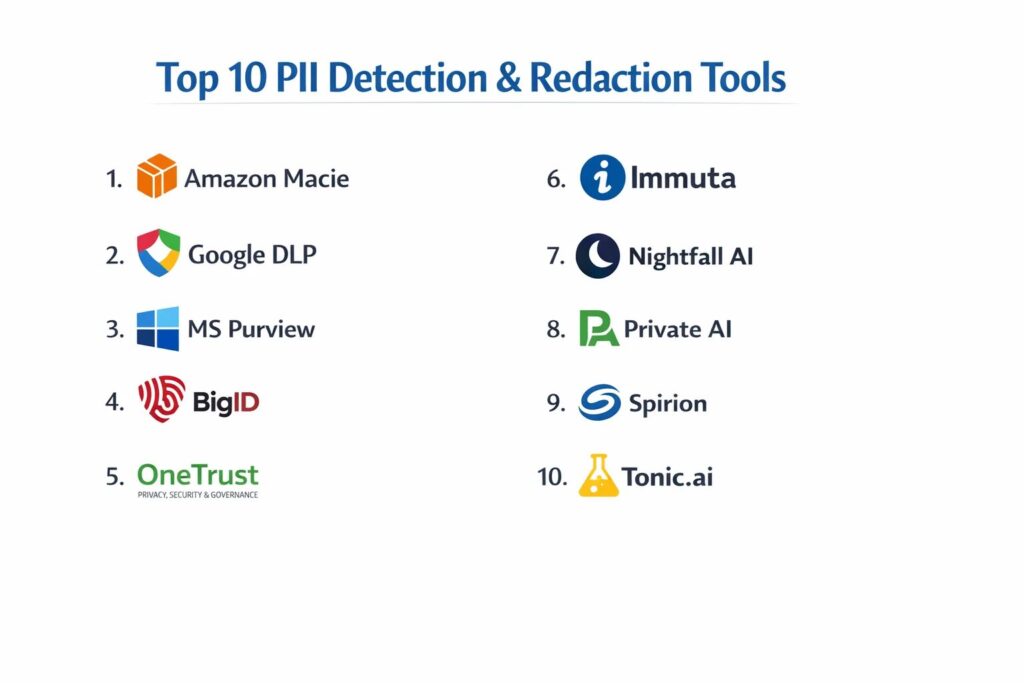
Personally Identifiable Information (PII) detection and redaction tools have become a critical component of the modern data security and compliance stack. As organizations transition toward data-centric security models, the ability to automatically identify, classify, and mask sensitive data—such as social security numbers, medical records, and financial details—is no longer optional. These platforms leverage advanced pattern matching and natural language processing to scan structured databases, unstructured documents, and even image files to ensure that sensitive information is not exposed during data sharing, analysis, or storage. For the modern enterprise, this technology serves as the primary defense against data breaches and the legal complexities of global privacy regulations.
The necessity for automated redaction is driven by the sheer volume of data generated across cloud environments and collaborative platforms. Manual redaction is not only prone to human error but is also impossible to scale in an era where petabytes of data are processed daily. A robust PII detection tool enables organizations to maintain “data utility” while ensuring “data privacy,” allowing teams to perform analytics on sanitized datasets without compromising individual identities. When selecting a platform, technical leaders must evaluate the accuracy of the detection engine, the breadth of supported file formats, the seamlessness of integration with existing data lakes, and the strength of the cryptographic methods used for masking and anonymization.
Best for: Data protection officers, security engineers, compliance managers, and legal teams who need to automate the discovery and protection of sensitive information across diverse digital environments.
Not ideal for: Basic document editing that does not require automated scanning, or small-scale operations where sensitive data is not handled or shared externally.
Key Trends in PII Detection & Redaction Tools
The integration of deep learning and transformer-based models has significantly improved the “contextual awareness” of detection engines, allowing them to distinguish between a string of numbers that is a phone number and one that is a serial number. We are seeing a major shift toward “Privacy-as-Code,” where PII detection is integrated directly into the software development lifecycle, ensuring that data is redacted before it ever reaches a production database. Real-time redaction is also becoming a standard requirement for communication platforms, enabling the masking of sensitive data in live chat, voice calls, and video streams to protect both customers and employees.
Confidential computing and edge-based detection are emerging as dominant trends, allowing data to be scanned and redacted locally on a device before being transmitted to the cloud. This “zero-trust” approach to data privacy ensures that sensitive information is never exposed to the service provider. Furthermore, the rise of synthetic data generation is complementing redaction tools, where platforms replace PII with realistic but fake data to allow for high-fidelity testing and machine learning model training. Finally, there is an increased focus on multi-modal detection, where tools can simultaneously redact text within images (OCR) and identify sensitive audio patterns in recorded conversations.
How We Selected These Tools
Our selection process involved a rigorous assessment of technical accuracy and the breadth of “out-of-the-box” classifiers provided by each platform. We prioritized tools that demonstrate high precision and recall rates in identifying PII across various languages and cultural contexts. A key criterion was the platform’s ability to handle both structured data, such as SQL databases, and unstructured data, such as PDFs, emails, and images. We looked for a balance between cloud-native services that offer high scalability and self-hosted solutions that provide maximum data sovereignty.
Integration capabilities were a major factor; we selected tools that can plug directly into popular cloud storage providers, communication tools, and data pipelines. Security certifications and compliance alignments were scrutinized to ensure that the tools themselves meet the rigorous standards they help their users achieve, such as SOC 2 and GDPR. We also assessed the flexibility of the redaction methods, looking for platforms that offer multiple options including masking, hashing, and tokenization. Finally, we evaluated the user interface and reporting capabilities, ensuring that compliance teams can easily audit and validate the redaction process across the entire organization.
1. Amazon Macie
Amazon Macie is a fully managed data security and data privacy service that uses machine learning and pattern matching to discover and protect sensitive data in AWS. It is designed for organizations heavily invested in the Amazon ecosystem that need to automate the protection of data stored in S3 buckets.
Key Features
The platform features automated discovery of sensitive data at scale, providing a constant visibility layer across all S3 storage. It includes a robust library of managed data identifiers for common PII, financial data, and credentials. The system provides “Sensitivity Scores” for S3 buckets to help security teams prioritize their remediation efforts. It features a dashboard that highlights where unencrypted or publicly accessible buckets reside. It also integrates seamlessly with AWS Step Functions to trigger automated redaction or quarantine workflows when PII is detected.
Pros
Native integration with AWS services makes it incredibly easy to deploy for existing cloud users. The machine learning models are continuously updated by Amazon to improve detection accuracy.
Cons
It is strictly limited to the AWS environment and cannot directly scan data in other cloud providers or on-premises. Costs can scale quickly if not managed through careful bucket selection.
Platforms and Deployment
Cloud-native (AWS).
Security and Compliance
Adheres to all AWS global security standards and helps organizations meet GDPR, HIPAA, and PCI DSS requirements.
Integrations and Ecosystem
Deeply integrated with AWS Security Hub, Amazon EventBridge, and AWS S3.
Support and Community
Supported by AWS Enterprise Support and a massive global community of cloud security architects.
2. Google Cloud Cloud DLP
Google Cloud Data Loss Prevention (Cloud DLP) is a highly sophisticated service for discovering, classifying, and redacting sensitive data. It offers one of the most powerful inspection engines in the market, capable of handling text, images, and structured databases.
Key Features
The platform features over 150 built-in “infoTypes” for detecting PII, credentials, and sensitive records globally. It includes advanced de-identification techniques such as “Format-Preserving Encryption” and “K-Anonymity” to maintain data utility. The system provides powerful Image OCR capabilities to detect and redact text within pictures and scanned documents. It features a “Risk Analysis” tool that helps quantify the probability of an individual being re-identified in a dataset. It also offers a streaming API for real-time redaction of data in transit.
Pros
The detection accuracy is world-class, particularly for diverse and international datasets. It offers the most flexible set of de-identification transformations in the cloud market.
Cons
The configuration can be complex, requiring a deep understanding of data transformation concepts. Pricing is based on the volume of data scanned, which requires careful budget planning.
Platforms and Deployment
Cloud-native (Google Cloud) with API access for multi-cloud use.
Security and Compliance
SOC 2, ISO 27001, and HIPAA compliant, providing a secure foundation for global data privacy.
Integrations and Ecosystem
Integrates natively with BigQuery, Cloud Storage, and Datastore, as well as third-party apps via API.
Support and Community
Comprehensive documentation and support through Google Cloud’s professional services and developer community.
3. Microsoft Purview Information Protection
Microsoft Purview is an integrated data governance and protection suite that helps organizations discover and secure sensitive information across the Microsoft 365 environment and beyond. It is the standard for organizations built on the Azure and Office 365 stack.
Key Features
The platform features “Sensitivity Labels” that can be applied to documents and emails to trigger automatic encryption and redaction. It includes a massive library of sensitive information types and trainable classifiers for industry-specific data. The system provides “Exact Data Matching” (EDM) to detect sensitive information based on actual records in a customer’s database. It features integrated data loss prevention (DLP) across Teams, SharePoint, and Exchange. It also offers a “Content Explorer” for a centralized view of all sensitive data within the tenant.
Pros
Provides a seamless experience for end-users as protection is built directly into their daily productivity tools. It offers exceptional visibility into data movement across the entire Microsoft ecosystem.
Cons
The licensing model can be confusing and often requires higher-tier enterprise plans for full functionality. Integration with non-Microsoft cloud services is less native.
Platforms and Deployment
Cloud-native (Azure/M365) with endpoint agents for Windows and macOS.
Security and Compliance
Standard-setting security including FedRAMP High, GDPR, and HIPAA compliance.
Integrations and Ecosystem
Deeply integrated with all Microsoft 365 apps, Azure, and a growing list of third-party SaaS applications.
Support and Community
Extensive documentation and support through Microsoft’s global partner network and enterprise support teams.
4. BigID
BigID is a specialized data intelligence platform that goes beyond simple detection to provide deep discovery and classification of PII. it is designed for enterprise-scale organizations with complex, multi-cloud, and on-premises data landscapes.
Key Features
The platform features “Correlation Technology” that identifies relationships between data points to find “dark” PII that others might miss. It includes an automated “Data Subject Access Request” (DSAR) fulfillment engine. The system offers a “Data Risk Dashboard” that quantifies the impact of potential breaches. It features native redaction and masking for both structured and unstructured data sources. It also includes “Data Lineage” tracking to show where sensitive information originated and where it has traveled.
Pros
It is one of the most comprehensive tools for discovering PII across fragmented data environments. The platform is highly effective at automating complex privacy compliance workflows.
Cons
The implementation is an enterprise-level undertaking and requires significant time and expertise. It is a premium product with a price point reflecting its deep capabilities.
Platforms and Deployment
Hybrid cloud, self-hosted, or SaaS.
Security and Compliance
SOC 2 certified and designed specifically to meet the most stringent requirements of GDPR, CCPA, and LGPD.
Integrations and Ecosystem
Extensive connectors for Snowflake, SAP, Salesforce, and all major cloud storage providers.
Support and Community
Provides dedicated account management and a professional services team for large-scale deployments.
5. OneTrust Data Discovery
OneTrust is a leader in the privacy and compliance space, providing a highly automated data discovery and classification tool as part of its broader Trust Intelligence Platform. It is favored by compliance officers for its focus on regulatory alignment.
Key Features
The platform features automated “Identity Correlation” to link PII to specific individuals across different systems. It includes a “Privacy Impact Assessment” (PIA) module that is directly linked to discovered data. The system offers automated redaction for document sharing and legal discovery. It features a “Global Regulatory Library” that automatically updates classifiers based on new laws. It also includes an “Inventory Mapping” tool to visualize data flows and residency across the organization.
Pros
Excellent for organizations that want to integrate PII detection directly into their privacy and ethics reporting. The platform is highly automated and reduces the manual burden on legal teams.
Cons
The interface can be overwhelming due to the sheer breadth of the OneTrust platform. Some users find the discovery engine less granular than specialized security tools.
Platforms and Deployment
Cloud SaaS with local scanning agents.
Security and Compliance
ISO 27001, SOC 2 Type II, and Cyber Essentials certified.
Integrations and Ecosystem
Integrates with over 500 applications including Slack, Jira, and various cloud databases.
Support and Community
Offers a robust “OneTrust University” and a global network of privacy professionals.
6. Immuta
Immuta is a data access control platform that provides automated PII detection and dynamic redaction for data engineering and analytics teams. It is designed to ensure that sensitive data is protected while it is being used for business intelligence.
Key Features
The platform features “Dynamic Data Masking,” which redacts PII at the time of the query without changing the underlying data. It includes an automated “Sensitive Data Discovery” engine that tags PII across multiple data sources. The system offers “Attribute-Based Access Control” (ABAC) to restrict data views based on user roles and purposes. It features “Privacy-Preserving Technologies” like differential privacy and k-anonymization. It also provides a centralized “Audit Trail” of every data access request and redaction event.
Pros
Ideal for data scientists who need to work with sensitive datasets in a compliant manner. It allows for “read-only” protection that doesn’t break existing data pipelines.
Cons
It is focused on the data analytics layer and is not a general-purpose document redaction tool. The setup requires coordination between security and data engineering teams.
Platforms and Deployment
Cloud SaaS, hybrid, or self-hosted.
Security and Compliance
SOC 2 Type II compliant and designed to facilitate HIPAA and GDPR compliance in analytics.
Integrations and Ecosystem
Deeply integrated with Snowflake, Databricks, Amazon Redshift, and Starburst.
Support and Community
Provides high-quality technical support and a community of data engineers focused on secure analytics.
7. Nightfall AI
Nightfall is a cloud-native DLP platform that uses machine learning to detect and redact PII across various SaaS applications. It is known for its “developer-first” approach and ease of integration into modern cloud workflows.
Key Features
The platform features “Deep Learning Detectors” that go beyond regex to find PII, secrets, and keys in text. It includes real-time protection for Slack, GitHub, and Jira. The system offers a “Developer SDK” for embedding PII detection directly into custom applications. It features automated remediation workflows that can delete, redact, or quarantine sensitive messages in chat apps. It also provides a centralized “Alerts Dashboard” for monitoring security incidents across all connected SaaS tools.
Pros
Extremely fast to set up and provides immediate visibility into sensitive data leaking through communication channels. The API is robust and very friendly for engineering teams.
Cons
The focus is primarily on SaaS and developer tools, making it less suitable for deep scanning of legacy on-premises databases. Some high-volume environments may find the alerting noisy.
Platforms and Deployment
Cloud-native SaaS and API.
Security and Compliance
SOC 2 Type II and HIPAA compliant, with data encryption in transit and at rest.
Integrations and Ecosystem
Native integrations with Slack, GitHub, Confluence, Jira, and Google Drive.
Support and Community
Offers a responsive support team and extensive documentation for its API and SDK.
8. Private AI
Private AI is a specialized provider of PII detection and redaction technology that focuses on high accuracy and data sovereignty. Its engine is designed to be integrated into existing products to ensure privacy at the source.
Key Features
The platform features a “Context-Aware” engine capable of detecting PII in over 50 languages. It includes specialized detectors for medical data (HIPAA) and financial records. The system offers high-performance redaction for text, images, and audio files. It features a “Local Deployment” model that ensures data never leaves the customer’s infrastructure for scanning. It also provides “Synthetic Data Replacement” where PII is replaced with realistic, non-identifiable entities.
Pros
The detection accuracy for unstructured text is among the best in the industry. The ability to deploy completely offline is a major advantage for highly regulated sectors.
Cons
It is primarily a “building block” for other applications rather than a standalone governance suite. It requires development effort to integrate into a wider workflow.
Platforms and Deployment
Docker containers for self-hosting or private cloud.
Security and Compliance
Designed to enable GDPR and HIPAA compliance by preventing the storage of PII in the first place.
Integrations and Ecosystem
Provides a simple REST API that can be integrated into any data pipeline or application.
Support and Community
Provides high-touch technical support for developers and detailed API documentation.
9. Spirion
Spirion is a veteran in the data privacy space, offering a robust platform for discovering and protecting PII with a focus on “Data Fingerprinting” and high-accuracy classification.
Key Features
The platform features “AnyFind” technology that accurately locates PII regardless of where it is stored. It includes automated classification based on sensitivity levels and regulatory requirements. The system offers “Data Minimization” tools to delete or redact information that is no longer needed. It features integrated protection for endpoints, servers, and cloud storage. It also provides a “Privacy Risk Score” to help organizations track their compliance posture over time.
Pros
The tool is highly effective at finding PII in complex, legacy data environments. It offers a very mature set of classification rules that have been refined over decades.
Cons
The user interface can feel dated compared to modern cloud-native entrants. Implementation on legacy endpoints can be resource-intensive.
Platforms and Deployment
On-premises, cloud, or hybrid.
Security and Compliance
Standard-setting security with a long history of helping organizations meet PCI and HIPAA standards.
Integrations and Ecosystem
Integrates with various security tools like SIEMs and DLP solutions to provide a unified defense.
Support and Community
Offers professional services and a dedicated support team with deep expertise in data privacy.
10. Tonic.ai
Tonic is a leader in “Fake Data” generation, providing a platform that automatically discovers PII and replaces it with synthetic data that looks and acts like the real thing. It is the go-to tool for developers who need realistic test data.
Key Features
The platform features automated “Database Scanning” to identify PII across all columns and tables. It includes a library of “Smart Generators” for creating realistic names, addresses, and credit card numbers. The system ensures “Differential Privacy” so that no real information can be reverse-engineered from the synthetic data. It features a “Consistency Engine” that ensures the same fake value is used for a specific entity across all databases. It also provides a “Compliance Report” to prove that production data has been safely desensitized.
Pros
The best solution for teams that need to use production-like data in development and staging environments. It completely eliminates the risk of PII leaks in the dev-test cycle.
Cons
It is a specialized tool for database synthesis and is not designed for redacting individual PDF documents. It requires a solid understanding of database schemas.
Platforms and Deployment
Self-hosted Docker or cloud-native.
Security and Compliance
SOC 2 Type II compliant and an essential tool for maintaining GDPR compliance in development.
Integrations and Ecosystem
Native support for PostgreSQL, MySQL, SQL Server, Oracle, and Snowflake.
Support and Community
Provides excellent technical documentation and a “Customer Success” model for engineering teams.
Comparison Table
| Tool Name | Best For | Platform(s) Supported | Deployment | Standout Feature | Public Rating |
| 1. Amazon Macie | AWS Ecosystem | AWS Cloud | Cloud-Native | Native S3 Integration | 4.5/5 |
| 2. Google Cloud DLP | High-Accuracy De-id | Google Cloud | Cloud-Native | 150+ infoTypes | 4.7/5 |
| 3. MS Purview | Microsoft 365 Users | Win, Mac, Cloud | Cloud-Native | Sensitivity Labels | 4.6/5 |
| 4. BigID | Fragmented Data | Hybrid Cloud | Hybrid | Correlation Discovery | 4.8/5 |
| 5. OneTrust | Privacy Governance | Web-Based | Cloud SaaS | Regulatory Library | 4.5/5 |
| 6. Immuta | Data Analytics | Cloud / Hybrid | Cloud-Native | Dynamic Masking | 4.7/5 |
| 7. Nightfall AI | SaaS Protection | Cloud / API | Cloud SaaS | ML-based SaaS DLP | 4.7/5 |
| 8. Private AI | Local / Multi-lingual | Docker, API | Self-hosted | Local PII Redaction | 4.9/5 |
| 9. Spirion | Legacy / Endpoints | Win, Mac, Linux | Hybrid | AnyFind Technology | 4.3/5 |
| 10. Tonic.ai | Test Data Synthesis | Docker, Cloud | Self-hosted | Synthetic Generators | 4.8/5 |
Evaluation & Scoring of PII Detection & Redaction Tools
The scoring below is a comparative model intended to help shortlisting. Each criterion is scored from 1–10, then a weighted total from 0–10 is calculated using the weights listed. These are analyst estimates based on typical fit and common workflow requirements, not public ratings.
Weights:
- Core features – 25%
- Ease of use – 15%
- Integrations & ecosystem – 15%
- Security & compliance – 10%
- Performance & reliability – 10%
- Support & community – 10%
- Price / value – 15%
| Tool Name | Core (25%) | Ease (15%) | Integrations (15%) | Security (10%) | Performance (10%) | Support (10%) | Value (15%) | Weighted Total |
| 1. Amazon Macie | 8 | 9 | 7 | 10 | 9 | 8 | 9 | 8.35 |
| 2. Google DLP | 10 | 6 | 9 | 10 | 10 | 8 | 8 | 8.75 |
| 3. MS Purview | 9 | 8 | 10 | 10 | 8 | 9 | 7 | 8.65 |
| 4. BigID | 10 | 4 | 9 | 10 | 8 | 9 | 6 | 8.15 |
| 5. OneTrust | 8 | 7 | 8 | 9 | 8 | 10 | 8 | 8.10 |
| 6. Immuta | 9 | 7 | 9 | 9 | 9 | 9 | 8 | 8.50 |
| 7. Nightfall AI | 8 | 10 | 9 | 9 | 10 | 9 | 9 | 8.95 |
| 8. Private AI | 10 | 6 | 8 | 10 | 10 | 8 | 9 | 8.70 |
| 9. Spirion | 9 | 5 | 7 | 9 | 7 | 8 | 7 | 7.35 |
| 10. Tonic.ai | 9 | 8 | 9 | 10 | 9 | 9 | 9 | 8.95 |
How to interpret the scores:
- Use the weighted total to shortlist candidates, then validate with a pilot.
- A lower score can mean specialization, not weakness.
- Security and compliance scores reflect controllability and governance fit, because certifications are often not publicly stated.
- Actual outcomes vary with assembly size, team skills, templates, and process maturity.
Which PII Detection & Redaction Tool Is Right for You?
Solo / Founder-Led
For startups where the founder is often the lead engineer, a developer-first tool like Nightfall AI is the best starting point. Its ability to quickly plug into Slack and GitHub ensures that sensitive data doesn’t leak during early-stage development, providing immediate protection with almost zero configuration.
Small Nonprofit
Organizations with limited technical resources should look for a user-friendly, SaaS-based solution that integrates with their existing productivity tools. A platform that offers automated document redaction and easy-to-read compliance reports will help meet legal requirements without needing a dedicated security officer.
Mid-Market
Growing companies should prioritize “Dynamic Masking” and tools that can scale with their data analytics needs. Immuta or Google Cloud DLP are excellent choices here, as they allow for secure data sharing between departments while maintaining high-speed performance for business intelligence.
Enterprise
Large organizations with massive, fragmented data landscapes require the deep discovery capabilities of BigID or Spirion. These tools are built to handle the “dark data” problem, ensuring that PII is found and secured across decades of legacy systems and multi-cloud environments.
Budget vs Premium
Cloud-native tools like Amazon Macie offer a great “pay-as-you-go” entry point for those on a budget. However, premium platforms like BigID provide a much higher return on investment for complex organizations by automating the entire privacy lifecycle, from discovery to the fulfillment of regulatory requests.
Feature Depth vs Ease of Use
If your primary goal is to provide developers with safe test data, Tonic.ai offers unparalleled feature depth in synthetic generation. If you simply need to label and protect files within your daily workflow, Microsoft Purview offers the best ease of use by integrating protection directly into Office 365.
Integrations & Scalability
For organizations running high-volume data pipelines, the ability of a tool to scale horizontally is vital. Tools like Private AI or Google Cloud DLP that offer high-throughput APIs are the best fit for ensuring that PII detection doesn’t become a bottleneck in your data processing architecture.
Security & Compliance Needs
If you handle extremely sensitive medical or financial data, look for tools that offer local or “on-premise” scanning options. Private AI and Tonic.ai are strong contenders for organizations that must ensure their sensitive data never leaves their secure perimeter, even for the purpose of redaction.
Frequently Asked Questions (FAQs)
1. What is the difference between PII detection and redaction?
Detection is the process of identifying where sensitive information exists within a dataset or document. Redaction is the subsequent action of masking, removing, or replacing that information so that it can no longer be seen or used to identify an individual.
2. Can these tools detect PII in images and scanned documents?
Yes, most modern tools use Optical Character Recognition (OCR) to scan images and PDFs. They can identify sensitive text within these files and apply a “black bar” redaction to the image before it is shared.
3. Is “masking” the same as “anonymization”?
Not necessarily. Masking often refers to hiding parts of the data (like the last four digits of a credit card). True anonymization involves transforming the data so that re-identification is mathematically impossible, often through techniques like k-anonymity or differential privacy.
4. How accurate are these automated tools?
Accuracy depends on the quality of the machine learning models. High-end tools provide over 95% accuracy for common identifiers, but human review is still recommended for highly sensitive or complex legal documents to ensure 100% compliance.
5. Do I need to be a developer to use a PII redaction tool?
No, many tools like Microsoft Purview and OneTrust are designed for compliance and legal professionals. However, “developer-first” tools and APIs like Nightfall or Private AI do require technical expertise to integrate into custom software.
6. Can these tools help with GDPR and HIPAA compliance?
Yes, they are specifically designed to automate the requirements of these laws. They provide the discovery, protection, and auditing capabilities necessary to prove to regulators that sensitive personal and medical data is being handled securely.
7. Does redacting data break my analytics dashboards?
Traditional redaction can break data types, but “Dynamic Masking” and “Format-Preserving Encryption” allow you to hide the sensitive values while keeping the data format intact, ensuring your dashboards still function correctly.
8. What is “Synthetic Data” and why is it used?
Synthetic data is fake data generated to have the same statistical properties as real data. It is used in development and testing because it contains no real PII, making it 100% safe to use in non-secure environments while still providing realistic results.
9. Can these tools redact audio and video?
A growing number of tools can transcribe audio in real-time and identify sensitive spoken patterns. For video, they can identify and blur faces or redact sensitive text that appears on a screen during a recording.
10. How do these tools handle multiple languages?
Global tools like Google Cloud DLP and Private AI use specialized language models trained on international data types, ensuring they can accurately identify PII across different countries, naming conventions, and address formats.
Conclusion
In a digital landscape where data privacy is becoming a fundamental human right, PII detection and redaction tools are no longer just security features—they are the bedrock of corporate trust. Implementing these technologies allows organizations to navigate the fine line between data-driven innovation and regulatory compliance, ensuring that sensitive information is never a liability. By automating the discovery and protection of personal data, teams can focus on their core mission while maintaining a robust defense against breaches and legal risks. The ideal redaction strategy is one that integrates seamlessly into your existing workflows, providing invisible but impenetrable protection for every constituent’s data.