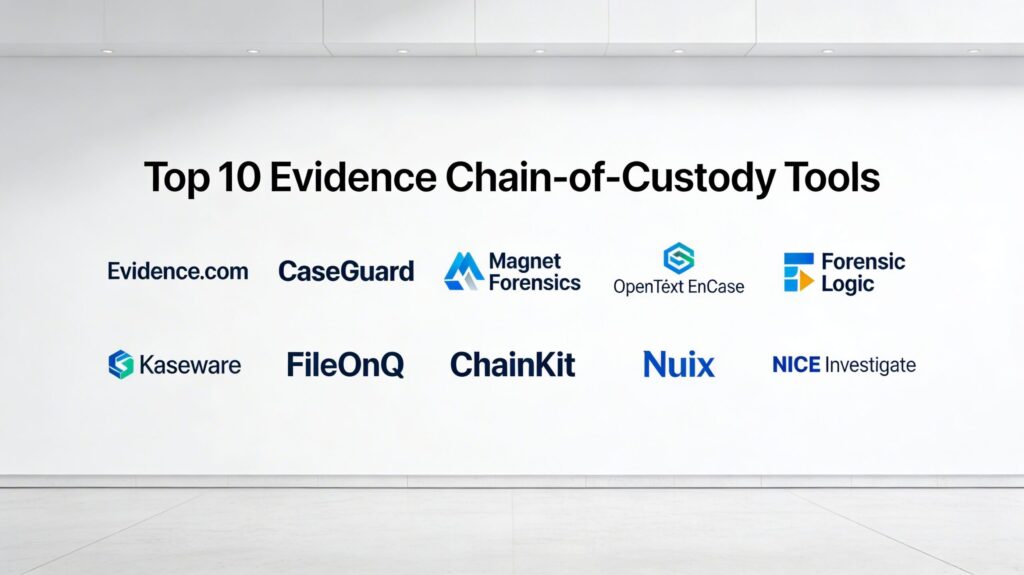
Introduction
Evidence chain-of-custody (CoC) tools are specialized digital systems designed to maintain a meticulous, chronological record of evidence handling, from the initial point of seizure to its final presentation in a court of law. In the modern investigative landscape, where digital artifacts are increasingly volatile and prone to claims of tampering, these tools serve as the ultimate guarantor of integrity and authenticity. By documenting every individual who accessed, transferred, or modified an item—along with precise timestamps and geographic data—these platforms create a defensible audit trail that ensures evidence remains admissible under strict legal scrutiny.
The technical core of a robust CoC tool involves cryptographic hashing, secure access controls, and automated logging mechanisms that eliminate the risk of human error or deliberate fabrication. As physical and digital evidence management converge, these systems act as a centralized “source of truth” for law enforcement, corporate security teams, and forensic laboratories. Transitioning from manual, paper-based logs to automated digital custody ensures that investigations are not derailed by procedural technicalities. A failure to maintain an unbroken chain of custody is one of the most common reasons for evidence to be suppressed, making these tools a critical investment for any organization tasked with fact-finding or legal compliance.
Best for: Law enforcement agencies, digital forensics and incident response (DFIR) teams, eDiscovery professionals, and corporate legal departments who must provide a legally defensible history of evidence handling.
Not ideal for: General administrative task management or simple document storage where legal-grade auditability and cryptographic integrity verification are not required.
Key Trends in Evidence Chain-of-Custody Tools
The most significant trend is the adoption of blockchain and distributed ledger technology (DLT) to create immutable custody records. By decentralizing the audit log, these tools ensure that even a system administrator cannot alter the history of who handled a piece of evidence. Another major shift is the move toward “cloud-native” evidence management, allowing field officers and lab technicians to sync evidence data in real-time via mobile devices, significantly reducing the “custody gap” that occurs between collection and formal intake.
Artificial intelligence is also playing a larger role, specifically in automated redaction and evidence categorization. Modern tools can now automatically identify and mask sensitive personal information (PII) in video evidence while maintaining a logged history of that redaction process. Furthermore, there is an increasing emphasis on “vendor-neutral” ecosystems, where CoC tools must integrate seamlessly with various hardware—ranging from body-worn cameras to high-end forensic workstations—to ensure that the digital thread remains unbroken regardless of the data source.
How We Selected These Tools
Our selection process focused on tools that meet the highest standards of legal admissibility, specifically prioritizing those that offer CJIS (Criminal Justice Information Services) compliance. We evaluated each platform based on the robustness of its cryptographic hashing (such as SHA-256 or SHA-3) and its ability to handle both physical and digital evidence within a single, unified interface. Market reputation and courtroom track record were also significant factors; we selected tools that are frequently cited in legal proceedings and endorsed by major investigative bodies.
Technically, we looked for platforms with granular role-based access control (RBAC) and multifactor authentication to ensure that only authorized personnel can touch sensitive data. Performance was measured by the speed of automated ingestion and the reliability of the system’s audit logging under high-volume data conditions. Finally, we prioritized tools that offer strong integration capabilities with existing Records Management Systems (RMS) and Laboratory Information Management Systems (LIMS), ensuring they fit naturally into established investigative workflows.
1. Evidence.com (Axon)
Evidence.com is a market-leading cloud-based digital evidence management system (DEMS) that serves as the backbone for many modern law enforcement agencies. It is designed to ingest and manage vast amounts of data, particularly from body-worn cameras and in-car video systems, while maintaining a rigorous, automated chain of custody.
Key Features
The platform features an automated “ingest-to-archive” workflow that logs every interaction with a file. It includes a powerful redaction suite that uses AI to blur faces and license plates automatically. The “Justice Link” feature allows for secure, logged sharing of evidence with prosecutors and defense attorneys. It provides a mobile app for field officers to tag and upload evidence instantly. The system also supports high-speed ingestion of third-party video and forensic images, ensuring all case materials are stored in a CJIS-compliant cloud environment with an unbroken audit trail.
Pros
Exceptional integration with Axon’s hardware ecosystem, making collection nearly hands-free. The security architecture is among the best in the industry, meeting federal standards for data protection.
Cons
The platform is primarily optimized for Axon hardware, which may lead to vendor lock-in. Subscription costs can be significant for smaller agencies with limited budgets.
Platforms and Deployment
Cloud-based SaaS with mobile application support for iOS and Android.
Security and Compliance
Fully CJIS, GDPR, and HIPAA compliant with AES-256 encryption at rest and in transit.
Integrations and Ecosystem
Seamlessly integrates with Axon hardware and major Records Management Systems (RMS) via API.
Support and Community
Offers 24/7 technical support and a massive user community of law enforcement professionals.
2. CaseGuard
CaseGuard is a comprehensive evidence management and redaction platform that focuses on making the chain of custody user-friendly for both digital and physical items. It is particularly known for its powerful media processing capabilities combined with strict investigative logging.
Key Features
The tool provides an all-in-one workspace for managing video, audio, and documents while automatically generating a time-stamped audit log of all changes. It features advanced hashing algorithms to verify file integrity throughout the investigation. The system allows for “bulk processing,” where thousands of files can be categorized and logged for custody simultaneously. It also includes a robust reporting engine that generates court-ready documentation of every handler’s activity. The software supports both cloud and on-premise deployments, providing flexibility for organizations with strict data residency requirements.
Pros
Highly intuitive interface that reduces the training time for investigators. The redaction tools are natively built into the custody workflow, ensuring no separate tools are needed.
Cons
Advanced AI features for automated tagging can require significant processing power for on-premise installations.
Platforms and Deployment
Available as a Windows-based application or a secure cloud deployment.
Security and Compliance
Supports CJIS requirements and provides detailed role-based access controls to prevent unauthorized evidence viewing.
Integrations and Ecosystem
Integrates with popular case management and cloud storage providers like Azure and AWS.
Support and Community
Provides dedicated technical account managers and extensive video training resources.
3. Magnet Forensics (Magnet AXIOM)
Magnet Forensics is a gold standard in the digital forensics world, offering tools that not only analyze data but strictly document the acquisition and handling process to ensure legal admissibility.
Key Features
Magnet AXIOM focuses on “complete” evidence recovery, pulling artifacts from mobile, cloud, and computer sources into a single case file. It automatically records the “acquisition hash” the moment data is collected, providing a baseline for integrity verification. The platform includes a “Portable Case” feature that allows investigators to share evidence with stakeholders while maintaining a secure, read-only audit environment. It features a built-in “Timeline View” that visualizes the chain of custody and evidence activity chronologically. The tool also supports remote acquisition, allowing teams to collect evidence over a network while maintaining strict CoC.
Pros
Unrivaled ability to recover and document evidence from a wide variety of digital sources. The reporting is specifically designed to meet the rigorous standards of forensic laboratory audits.
Cons
The software has a steep learning curve and requires specialized forensic training to use effectively. It is among the more expensive forensic suites on the market.
Platforms and Deployment
Primarily Windows-based for laboratory use, with cloud-based collaboration components.
Security and Compliance
ISO 17025 compliant workflows with encrypted case containers.
Integrations and Ecosystem
Integrates with other forensic tools and Case Management Systems through standardized export formats.
Support and Community
Offers a world-class training academy and an extremely active community of forensic examiners.
4. OpenText EnCase
EnCase is one of the most established names in digital investigations, widely recognized by courts worldwide for its “forensic-grade” evidence preservation and chain-of-custody tracking.
Key Features
The platform uses a proprietary evidence file format (.E01) that incorporates internal hashing and compression to ensure the evidence cannot be modified without detection. It provides deep visibility into the file system, allowing for the discovery of hidden or deleted data while maintaining a permanent log of the examiner’s actions. It features automated “Condition” checks that alert the user if the integrity of the evidence has been compromised. The enterprise version allows for “dead-box” and “live” forensic imaging across thousands of endpoints while documenting the custody of each digital image.
Pros
Immense credibility in the legal system; EnCase reports are standard in international courts. The proprietary file format is a benchmark for digital evidence integrity.
Cons
The user interface is dated and can be complex for non-specialists. Processing speeds for very large datasets can be slower than more modern competitors.
Platforms and Deployment
Windows-based software with options for enterprise-wide networked deployment.
Security and Compliance
FIPS 140-2 compliant encryption and robust audit logging for regulatory compliance.
Integrations and Ecosystem
Wide support for third-party forensic plugins and integration with OpenText’s broader Information Management suite.
Support and Community
Extensive documentation and a long-standing certification program (EnCE).
5. Forensic Logic
Forensic Logic is a cloud-native platform that excels in aggregating investigative data from across multiple jurisdictions, providing a unified chain of custody for large-scale operations.
Key Features
The platform features a powerful “LEAP” search engine that allows investigators to track evidence across different agencies and cases. It provides real-time status updates and alerts whenever evidence is moved or accessed. The system includes a digital evidence vault that automatically handles the upload and hashing of media files from the field. It features a simplified handoff workflow where transfers between officers and evidence technicians are digitally signed and time-stamped. The tool also provides data visualization tools to map the movement of evidence over time.
Pros
Excellent for multi-agency task forces that need to share evidence while maintaining a centralized custody record. The search capabilities are exceptionally fast for large datasets.
Cons
The platform’s strength lies in its network effect; it is less effective for isolated, single-user investigative units.
Platforms and Deployment
Fully cloud-based SaaS optimized for web and mobile browsers.
Security and Compliance
Exceeds CJIS standards and utilizes advanced encryption for cross-jurisdictional data sharing.
Integrations and Ecosystem
Strongest when integrated with existing CAD (Computer-Aided Dispatch) and RMS systems.
Support and Community
Provides proactive monitoring of system health and 24/7 support for critical investigations.
6. Kaseware
Kaseware is an investigative case management platform built by former FBI agents, specifically designed to unify evidence tracking with the broader investigative workflow.
Key Features
The platform offers a single interface to manage physical inventory and digital files, using barcode and RFID scanning to automate the movement of physical evidence. It features an “Immutable Audit Log” that records every view, edit, and transfer within the system. Kaseware includes a built-in map interface to track where evidence was collected and where it is currently stored. It provides custom workflow builders to ensure that evidence handoffs follow the organization’s specific legal protocols. The tool also supports bulk evidence ingestion from various digital sources with automated hash verification.
Pros
Unified management of both physical and digital evidence reduces the need for multiple siloed systems. Designed by investigators for investigators, resulting in highly practical workflows.
Cons
The broad feature set may be overkill for organizations that only need simple digital evidence storage.
Platforms and Deployment
Cloud-native with full mobile compatibility for field operations.
Security and Compliance
CJIS-ready with SOC 2 Type II certification and robust encryption protocols.
Integrations and Ecosystem
Offers a wide range of APIs to connect with external databases and forensic tools.
Support and Community
Offers personalized onboarding and dedicated support for large enterprise deployments.
7. FileOnQ
FileOnQ is a highly specialized evidence management system that focuses on the lifecycle of physical evidence while offering a bridge to digital evidence tracking.
Key Features
The platform utilizes sophisticated barcode technology to track evidence from the crime scene to the courtroom to final disposition. It provides a “Check-in/Check-out” system that mirrors traditional library science but with forensic-level auditability. The software includes an automated notification system that alerts custodians when evidence is due for return or scheduled for destruction. It features a “Digital Evidence Portal” that allows officers to upload media directly into a case folder. The system also generates comprehensive “Disposition Reports” to ensure that evidence is legally and securely disposed of once a case is closed.
Pros
The most robust system for managing high volumes of physical evidence in large property rooms. The customization of data fields allows it to fit any agency’s specific needs.
Cons
The digital evidence features are not as advanced as those of dedicated DEMS like Evidence.com.
Platforms and Deployment
Available for on-premise servers or as a hosted cloud solution.
Security and Compliance
Adheres to strict CJIS and local legal requirements for evidence logging and data protection.
Integrations and Ecosystem
Integrates with barcode scanners, label printers, and existing RMS databases.
Support and Community
Known for exceptional customer service and on-site implementation support.
8. ChainKit
ChainKit is a disruptive player in the CoC market, utilizing blockchain technology to provide “stealth” integrity monitoring for digital evidence and audit trails.
Key Features
The tool acts as an “integrity layer” that can sit on top of existing storage systems like SharePoint, Azure, or local drives. It uses patent-pending blockchain integration to register the hash of every piece of evidence, creating an immutable record of its existence and state. ChainKit provides “Real-Time Integrity Alerts” that notify administrators if any file has been tampered with or moved outside of authorized channels. It features a “Proof of Custody” certificate that can be generated for any item, providing a cryptographically verifiable history for court use. The system requires no changes to existing workflows, as it monitors evidence in the background.
Pros
Provides a level of tamper-proofing that traditional databases cannot match. It is highly cost-effective as it enhances existing infrastructure rather than replacing it.
Cons
It is a specialized integrity tool and does not provide a full “case management” interface or redaction tools.
Platforms and Deployment
Cloud-based API or lightweight agents for on-premise servers.
Security and Compliance
Military-grade security using decentralized verification to prevent internal or external tampering.
Integrations and Ecosystem
Designed to integrate with almost any existing storage or case management system via API.
Support and Community
Focuses on technical documentation and enterprise-level developer support.
9. Nuix (Nuix Discover)
Nuix is a high-performance data processing engine that is essential for investigations involving massive amounts of electronic evidence and complex chain-of-custody needs.
Key Features
Nuix excels in “Early Case Assessment” (ECA), allowing investigators to ingest and hash terabytes of data daily to identify relevant evidence quickly. It maintains a “Global Master Index” that tracks every item’s location and custody status across different storage silos. The platform includes advanced visualization tools to map communication networks and data transfers. It features a robust “Audit Export” that provides a line-by-line history of how data was filtered and processed for legal review. The system is highly effective at handling “problematic” data types that other tools might fail to hash or index correctly.
Pros
Unmatched speed and scalability for investigations involving massive data volumes. Excellent for identifying “insider threats” by tracking data movement across an entire enterprise.
Cons
The complexity and cost make it unsuitable for small teams or routine investigations. Requires high-end hardware for optimal on-premise performance.
Platforms and Deployment
Cloud-native options or high-performance on-premise workstations.
Security and Compliance
Certified for use in the most highly regulated government and financial environments.
Integrations and Ecosystem
Deep integrations with eDiscovery platforms and forensic imaging tools.
Support and Community
Extensive enterprise support and a specialized certification program for high-end users.
10. NICE Investigate
NICE Investigate is a comprehensive digital evidence management solution that focuses on “case correlation” and breaking down data silos across different investigative units.
Key Features
The platform provides a “Digital Evidence Folder” for every case, automatically aggregating data from CCTV, body cameras, and public submissions. It features an automated “Chain of Custody Report” that summarizes all evidence activity in a court-ready format. The tool includes a “Business Portal” that allows private businesses to securely share security camera footage directly with law enforcement. It provides advanced search tools that use metadata to find links between different pieces of evidence in unrelated cases. The system also automates the process of “Digital Handoff” to the prosecutor’s office, tracking the transfer of custody digitally.
Pros
Excellent for collaborative investigations involving both public and private sector data. The automated case building features save investigators hundreds of hours in manual documentation.
Cons
Initial implementation can be complex due to the number of external data sources it connects to.
Platforms and Deployment
Cloud-based SaaS optimized for large-scale public safety deployments.
Security and Compliance
CJIS-compliant and hosted in secure government-grade cloud environments (e.g., AWS GovCloud).
Integrations and Ecosystem
Integrates with a wide variety of public safety hardware, RMS, and CAD systems.
Support and Community
Offers extensive training and 24/7 mission-critical support for law enforcement agencies.
Comparison Table
| Tool Name | Best For | Platform(s) Supported | Deployment | Standout Feature | Public Rating |
| 1. Evidence.com | Law Enforcement | Web, iOS, Android | Cloud | Axon Ecosystem Sync | 4.8/5 |
| 2. CaseGuard | Media Redaction | Windows, Web | Hybrid | AI-Driven Redaction | 4.7/5 |
| 3. Magnet Forensics | Digital Forensics | Windows, Web | Hybrid | Complete Artifact Recovery | 4.9/5 |
| 4. OpenText EnCase | Court Credibility | Windows | On-Prem | .E01 Forensic Format | 4.5/5 |
| 5. Forensic Logic | Multi-Agency Collab | Web, Mobile | Cloud | LEAP Cross-Agency Search | 4.4/5 |
| 6. Kaseware | Unified Case Mgmt | Web, iOS, Android | Cloud | Former FBI Design Logic | 4.6/5 |
| 7. FileOnQ | Physical Evidence | Windows, Web | Hybrid | Barcode/RFID Tracking | 4.7/5 |
| 8. ChainKit | Data Integrity | API-based | Cloud/Agent | Blockchain-backed Logs | 4.3/5 |
| 9. Nuix | Large-scale DFIR | Windows, Cloud | Hybrid | Terabyte-scale Processing | 4.6/5 |
| 10. NICE Investigate | Case Correlation | Web | Cloud | Public-Private Data Sharing | 4.5/5 |
Evaluation & Scoring of Evidence Chain-of-Custody Tools
The scoring below is a comparative model intended to help shortlisting. Each criterion is scored from 1–10, then a weighted total from 0–10 is calculated using the weights listed. These are analyst estimates based on typical fit and common workflow requirements, not public ratings.
Weights:
- Core features – 25%
- Ease of use – 15%
- Integrations & ecosystem – 15%
- Security & compliance – 10%
- Performance & reliability – 10%
- Support & community – 10%
- Price / value – 15%
| Tool Name | Core (25%) | Ease (15%) | Integrations (15%) | Security (10%) | Performance (10%) | Support (10%) | Value (15%) | Weighted Total |
| 1. Evidence.com | 10 | 9 | 10 | 10 | 9 | 10 | 7 | 9.30 |
| 2. CaseGuard | 9 | 10 | 8 | 9 | 9 | 9 | 8 | 8.85 |
| 3. Magnet Forensics | 10 | 6 | 9 | 10 | 10 | 10 | 7 | 9.00 |
| 4. OpenText EnCase | 10 | 5 | 8 | 9 | 8 | 9 | 7 | 8.15 |
| 5. Forensic Logic | 8 | 8 | 9 | 9 | 10 | 8 | 8 | 8.45 |
| 6. Kaseware | 9 | 8 | 9 | 9 | 8 | 9 | 9 | 8.80 |
| 7. FileOnQ | 10 | 8 | 8 | 9 | 8 | 10 | 8 | 8.85 |
| 8. ChainKit | 7 | 9 | 10 | 10 | 10 | 7 | 9 | 8.50 |
| 9. Nuix | 10 | 5 | 9 | 10 | 10 | 8 | 6 | 8.40 |
| 10. NICE Investigate | 9 | 8 | 10 | 9 | 9 | 9 | 7 | 8.70 |
How to interpret the scores:
- Use the weighted total to shortlist candidates, then validate with a pilot.
- A lower score can mean specialization, not weakness.
- Security and compliance scores reflect controllability and governance fit, because certifications are often not publicly stated.
- Actual outcomes vary with assembly size, team skills, templates, and process maturity.
Which Evidence Chain-of-Custody Tool Is Right for You?
Solo / Freelancer
For the independent forensic examiner, Magnet AXIOM is often the most comprehensive choice. It provides all the necessary documentation for a single investigator to handle a case from acquisition to report without needing a massive server infrastructure.
SMB
Small to medium-sized investigative firms should consider CaseGuard. Its ease of use and built-in redaction tools mean that a small team can handle digital evidence professionally without the high overhead of more complex enterprise systems.
Mid-Market
Organizations that handle a mix of physical and digital evidence, such as private security firms or mid-sized police departments, will find Kaseware or FileOnQ to be highly effective. These tools provide the necessary bridge between warehouse management and digital storage.
Enterprise
For global corporations or national law enforcement agencies, Evidence.com or Nuix offer the necessary scale. These platforms are designed to handle millions of files and provide the high-level security controls required for multi-site, multi-jurisdictional investigations.
Budget vs Premium
If the primary concern is ensuring data integrity on a budget, ChainKit offers a unique way to add blockchain-level security to your existing storage. However, if you need a full-featured “premium” ecosystem with hardware integration, Evidence.com is the industry leader for a reason.
Feature Depth vs Ease of Use
EnCase and Nuix offer unparalleled depth but require a dedicated technical staff. In contrast, NICE Investigate and Forensic Logic prioritize a streamlined user experience that allows non-technical officers to manage evidence with minimal training.
Integrations & Scalability
Scalability is the hallmark of cloud-native tools like Evidence.com and NICE Investigate. They can grow instantly to accommodate massive video datasets, whereas on-premise solutions like EnCase require significant hardware planning to scale effectively.
Security & Compliance Needs
All listed tools are secure, but for those requiring specific federal compliance (CJIS) or laboratory accreditation (ISO 17025), Magnet Forensics and Evidence.com provide the most detailed documentation and pre-configured workflows to meet those standards.
Frequently Asked Questions (FAQs)
1. What is a “hash” in the context of evidence?
A hash is a unique digital fingerprint of a file. If even a single pixel in an image or a character in a document is changed, the hash will change. Tools use this to prove that evidence is identical to the original version collected.
2. Can evidence be stored on any cloud provider?
No, for legal and law enforcement purposes, the cloud provider must be CJIS compliant. This ensures the data center has physical security, background-checked staff, and strict encryption protocols that meet government standards.
3. Does digital evidence ever expire?
Evidence doesn’t “expire,” but it is subject to “retention policies.” Tools like FileOnQ and Evidence.com automatically track these periods and alert custodians when evidence can be legally disposed of to save storage space and reduce liability.
4. How do these tools handle “Deepfakes”?
Modern forensic tools like Magnet AXIOM are beginning to integrate AI-driven detection to identify manipulated media. The chain of custody logs would show if a file was flagged as potentially altered during the initial ingestion phase.
5. What is the difference between a DEMS and an RMS?
A Digital Evidence Management System (DEMS) stores the actual large files like video and audio. A Records Management System (RMS) stores the written reports and case data. Most top tools integrate the two for a seamless workflow.
6. Can defense attorneys access these systems?
Yes, most enterprise tools have a “secure share” feature. Instead of mailing a DVD, the investigator sends a logged, time-limited link that allows the attorney to view or download evidence, with every action recorded in the audit trail.
7. Why is paper logging considered insufficient today?
Paper logs are prone to being lost, illegible, or backdated. Digital tools provide “active” security, recording the GPS location and the exact millisecond an action occurred, making them much harder to challenge in court.
8. Do these tools track the movement of physical items?
Yes, tools like FileOnQ and Kaseware use barcode or RFID tags. When a physical item is moved from a locker to a lab, it is scanned, and the digital record is updated instantly to reflect the new “custodian.”
9. Is training required to use forensic-grade tools?
For specialized software like EnCase or Magnet Forensics, professional certification is often required to testify as an expert witness. Simpler management tools usually only require basic software training.
10. What happens if the audit log itself is tampered with?
This is why many modern tools use blockchain or write-once-read-many (WORM) storage. These technologies make it technically impossible to delete or change an entry once it has been written to the audit log.
Conclusion
Maintaining a pristine chain of custody is not merely a technical requirement; it is the fundamental ethical obligation of any investigative professional. Where the volume of digital evidence is exploding and the sophistication of data manipulation is reaching new heights, relying on legacy logging methods is no longer a viable strategy. The tools highlighted in this guide represent the vanguard of evidence integrity, offering a blend of cryptographic certainty and operational efficiency. By selecting a platform that aligns with your organization’s scale, budget, and specific data sources, you protect not only the evidence itself but also the ultimate outcome of the justice process. Investing in a robust chain-of-custody system ensures that when you present your findings, the only thing the court needs to focus on is the facts of the case, not the history of the file.