Introduction
Digital identity wallets have emerged as the foundational layer of the modern “Trust Economy,” allowing individuals to store and share verified credentials without relying on physical plastic cards. These applications utilize advanced cryptography and decentralized protocols to give users a secure way to prove their age, citizenship, and qualifications in both the physical and digital worlds. By 2026, the transition from simple “payment wallets” to comprehensive “identity wallets” has accelerated, driven by global regulations and the need for more secure, privacy-preserving methods of online authentication.
As cyber threats like deepfakes and sophisticated phishing attempts rise, a verified digital identity has become a primary defense for both individuals and enterprises. These wallets allow for “Selective Disclosure,” a feature where a user can prove they are over 18 without revealing their exact birth date or home address. This shift toward user-centric data control is not just about convenience; it is a fundamental redesign of how personal information is managed, ensuring that people remain the ultimate owners of their digital footprints.
Real-World Use Cases
- Seamless Travel and Border Crossing: Travelers use their wallets to store digital versions of passports and visas, enabling biometric “walk-through” experiences at airport security and hotel check-ins.
- Instant Financial Onboarding: When opening a new bank account, users can share verified residency and identity documents instantly, reducing a multi-day verification process to a few seconds.
- Reusable Workplace Identity: Employees can carry verified “employment badges” that grant them access to physical offices and secure digital systems across different corporate partners.
- Age Verification for Restricted Services: Online retailers and entertainment platforms verify age through a simple wallet “handshake,” ensuring legal compliance without collecting unnecessary personal data.
- Education and Degree Verification: Graduates hold digital diplomas in their wallets, allowing them to instantly share tamper-proof academic credentials with potential employers or licensing boards.
Buyer Evaluation Criteria
- Level of Assurance (LoA): Check if the wallet meets high-level regulatory standards (like NIST IAL2 or eIDAS High), which determines if the identity is legally valid for government and banking use.
- Privacy and Zero-Knowledge Proofs: Evaluate if the tool supports “Zero-Knowledge” protocols, allowing you to share “proof” of an attribute without sharing the actual raw data.
- Interoperability Standards: Ensure the wallet follows global standards like W3C Verifiable Credentials and ISO 18013-5 to prevent being locked into a single vendor’s ecosystem.
- Biometric Security Integration: Look for deep integration with hardware-level security, such as Apple’s Secure Enclave or Android’s StrongBox, for multi-factor biometric authentication.
- Offline Functionality: Determine if the wallet can function without an active internet connection, which is essential for presenting IDs at remote checkpoints or during travel.
- Self-Sovereign Identity (SSI) Principles: Assess whether the vendor has access to your data or if the wallet is truly “Self-Sovereign,” meaning only the user holds the private keys to their identity.
- Revocation Management: The platform must have a robust way to instantly revoke or update credentials (like a driver’s license) if they are lost, stolen, or expired.
- Multi-Device Synchronization: Check if the wallet can be safely backed up and synchronized across multiple devices without compromising the security of the private keys.
- Ecosystem and Acceptance: A wallet is only as good as the places that accept it; evaluate the number of government agencies and private businesses that are already part of the network.
- User Experience (UX): The interface must be simple enough for non-technical users to navigate, especially when managing complex consent requests for their data.
Best for: Individuals seeking a paperless lifestyle, government agencies digitizing public services, and highly regulated enterprises in finance and healthcare.
Not ideal for: Organizations in regions where digital ID laws are not yet established or users who do not have access to a modern smartphone with biometric capabilities.
Key Trends in Digital Identity Wallets
- The Rise of Government-Mandated Wallets: Major economic zones are now mandating that every citizen has access to a state-certified digital wallet for public services.
- Decentralized Identifiers (DIDs): Wallets are moving away from centralized usernames and passwords toward DIDs, which are unique, self-owned identifiers that cannot be taken away by a service provider.
- Agentic AI Identity: New wallets are beginning to feature “Identity Agents” that can negotiate on the user’s behalf, ensuring only the minimum required data is shared with third-party apps.
- Post-Quantum Cryptography: As quantum computing advances, leading wallets are upgrading their encryption methods to ensure identity data remains secure for decades.
- Unified Payment and Identity: The line between financial wallets and identity wallets is blurring, with platforms allowing users to prove their identity and pay for a service in a single encrypted transaction.
- Biometric Re-verification: To combat “Shadow Identity,” wallets now require periodic “Live” biometric checks to ensure the person holding the device is still the verified owner.
- Open Source Frameworks: Public trust is being built through open-source codebases, allowing security researchers to verify that no “backdoors” exist in the wallet software.
- Cross-Border Interoperability: New international agreements are allowing a digital identity issued in one country to be legally recognized and used in another.
How We Selected These Tools (Methodology)
Our selection of the top 10 identity wallets for the current landscape focuses on security, regulatory compliance, and widespread adoption. We prioritized tools that offer a balance between consumer convenience and enterprise-grade security.
- Security Architecture: We analyzed the underlying technology, giving preference to wallets that use hardware-backed security and end-to-end encryption.
- Regulatory Compliance: Every tool on this list adheres to major global standards such as GDPR, eIDAS, or NIST, ensuring they are suitable for legal use.
- User Adoption and Ecosystem: We looked for wallets that are widely accepted by airlines, banks, and government institutions to ensure immediate utility for the user.
- Innovation in Privacy: We prioritized platforms that have successfully implemented “Selective Disclosure” and other privacy-preserving technologies.
- Cross-Platform Availability: The list includes solutions that work across iOS and Android to ensure inclusivity for all smartphone users.
- Enterprise Integration: For B2B tools, we evaluated how easily the wallet infrastructure can be integrated into existing corporate HR and security stacks.
- Financial Stability and Backing: We selected vendors that have the longevity and financial resources to maintain high-security infrastructure over the long term.
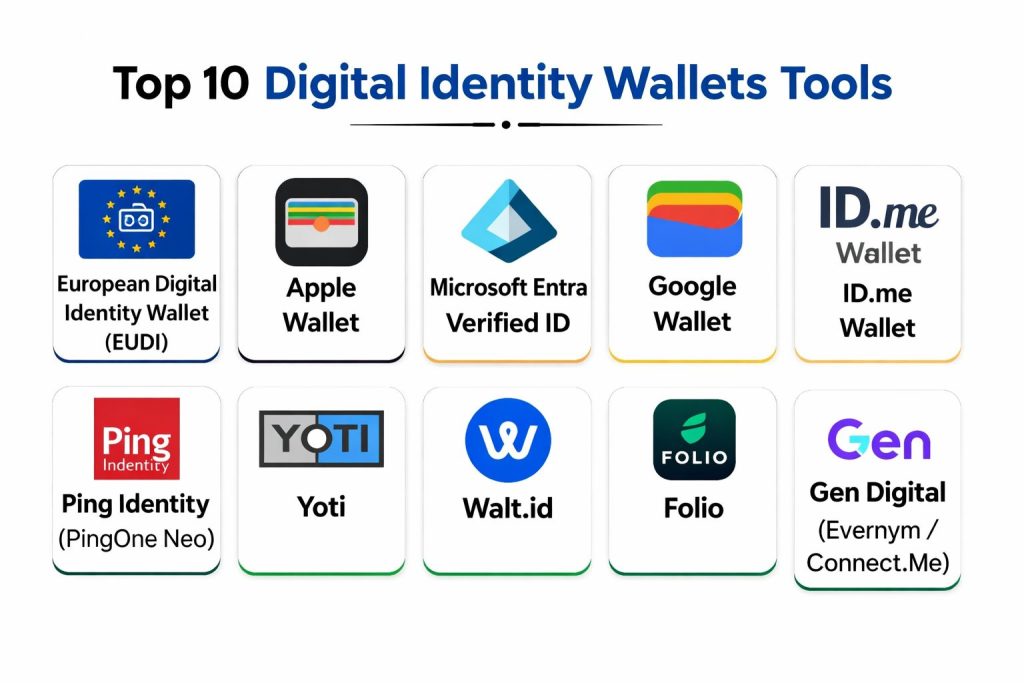
Top 10 Digital Identity Wallets
1. European Digital Identity Wallet (EUDI)
Description: The EUDI Wallet is a landmark initiative designed to provide a secure, interoperable digital identity for all residents across the European Union. It allows users to store national IDs, professional certificates, and even bank details, ensuring they can access services seamlessly in any member state.
Key Features
- Cross-Border Interoperability: A single wallet that is legally recognized for opening bank accounts or enrolling in universities in any EU country.
- Qualified Electronic Signatures: Built-in capability to sign legal documents with the same legal weight as a handwritten signature.
- Full Data Control: Users choose exactly which “attributes” to share, such as proving age without sharing their full name or address.
- Multi-Source Credentials: Can pull and verify data from multiple government departments, including tax offices and health ministries.
- Public and Private Acceptance: Designed for use with both government portals (like filing taxes) and private businesses (like renting a car).
- Open Source Toolbox: The technical architecture is built on an open-source framework to ensure transparency and public trust.
- High Assurance Levels: Meets the strictest security requirements under the eIDAS regulation for high-stakes transactions.
Pros
- Backed by the legal force of the European Union, ensuring nearly universal acceptance across the continent.
- Eliminates the need for multiple usernames and passwords for government and essential services.
- Strongest privacy protections in the world, strictly adhering to GDPR and data minimization principles.
Cons
- Implementation varies slightly by country, leading to a staggered rollout across different member states.
- Primarily designed for EU residents, limiting its utility for users based in the Americas or Asia.
- Requires a fairly modern smartphone with specific security hardware for full functionality.
Platforms / Deployment
- iOS / Android / Web
- State-issued SaaS and Local Apps
Security & Compliance
- eIDAS 2.0 High-Level Assurance compliant.
- Full GDPR compliance with localized data hosting requirements.
Integrations & Ecosystem
- Integrates with all major EU government portals and public registries.
- Partnerships with major European banks for instant KYC (Know Your Customer) onboarding.
- Support for a wide range of “relying parties” including telecom providers and utility companies.
- Connectivity with educational databases for digital diploma verification.
Support & Community
Support is provided by individual member state governments with a central EU technical oversight group. The project maintains a massive “Toolbox” of technical specifications for developers and service providers.
2. Apple Wallet
Description: Apple Wallet has evolved into a high-assurance identity hub, allowing users in supported regions to add state IDs, driver’s licenses, and passports. It leverages the iPhone’s advanced biometric hardware to offer one of the most secure and user-friendly identity experiences available today.
Key Features
- Secure Enclave Storage: Identity data is stored in a dedicated hardware-level chip, making it inaccessible even to the OS or Apple itself.
- On-Device Verification: Uses Face ID and Touch ID for every identity presentation, ensuring only the owner can use the ID.
- Privacy-First Sharing: When presenting an ID, the device only displays the specific information requested by the reader (e.g., just “Age 21+”).
- TSA Integration: Supported at major airports for seamless identity verification at security checkpoints without showing a physical card.
- Digital Car Keys & Badges: Extends identity to include employee badges and digital keys for homes, offices, and vehicles.
- Zero-Knowledge Presentation: Uses encrypted communication with the reader so that Apple never knows when or where you showed your ID.
- In-App Identity Proofing: Allows third-party apps to verify your identity directly through the wallet for secure account creation.
Pros
- Provides the most polished and frictionless user experience in the digital identity market.
- Hardware-level security makes it extremely difficult for bad actors to extract or spoof identity data.
- Massive adoption among retailers and travel hubs, particularly in North America.
Cons
- Completely locked into the Apple ecosystem; not available for Android users or other platforms.
- Availability of state ID and driver’s license features is currently limited to specific participating regions.
- Apple maintains control over the platform’s features, limiting customization for enterprise users.
Platforms / Deployment
- iOS (iPhone) / watchOS (Apple Watch)
- Hardware-integrated app
Security & Compliance
- ISO 18013-5 (Mobile Driver’s License) compliant.
- SOC 2 and FIPS 140-2 Level 3 equivalent security architecture.
Integrations & Ecosystem
- Deeply integrated with the TSA and US state DMV systems.
- Partnership with major hotel chains for “digital key” and identity check-in.
- Support for enterprise badges via HID Global and other major security providers.
- Native integration with Apple Pay for combined identity and payment workflows.
Support & Community
Apple provides standard consumer support and a dedicated developer portal for integrating “Passes” and identity features. They have a global community of developers building for the iOS ecosystem.
3. Microsoft Entra Verified ID
Description: Microsoft Entra Verified ID is an enterprise-grade identity platform that allows organizations to issue and verify digital credentials. It is built on decentralized identity standards, making it ideal for corporate environments where secure employee and partner onboarding is a priority.
Key Features
- Decentralized Identity (SSI): Uses open standards (W3C) to ensure that the user, not Microsoft or the employer, owns the credential.
- Verified Employee Credentials: Allows companies to issue digital badges that employees can use to prove their employment status to third parties.
- Rapid Onboarding: Automates the verification of new hires by checking their previous digital credentials or government IDs.
- Microsoft Authenticator Integration: The wallet functionality is built directly into the widely used Microsoft Authenticator app.
- Privacy-Preserving Verification: Uses “Selective Disclosure” to allow users to share only what is necessary for a specific task.
- Partner Ecosystem Integration: Pre-built connectors for identity verification services like ID.me and Onfido.
- Developer SDKs: Comprehensive libraries for building identity verification into custom corporate web and mobile apps.
Pros
- The natural choice for organizations already using the Microsoft 365 or Azure ecosystems.
- High degree of flexibility for custom use cases, such as student IDs or professional certifications.
- Strong focus on interoperability, ensuring credentials can be used outside of the Microsoft environment.
Cons
- The user experience is more corporate and functional, lacking the “sleekness” of consumer-focused wallets.
- Requires an Azure subscription for organizations wishing to issue and manage credentials.
- Can be complex for small businesses without a dedicated IT or security team.
Platforms / Deployment
- iOS / Android (via Microsoft Authenticator)
- Azure Cloud-based SaaS
Security & Compliance
- ISO 27001, SOC 2 Type II, and GDPR compliant.
- Supports OIDC4VC and other modern decentralized identity protocols.
Integrations & Ecosystem
- Native integration with Microsoft 365, LinkedIn, and Azure Active Directory.
- Connections to a wide network of identity verification providers (IDVs).
- Support for a broad range of HR and ITSM systems for automated workflows.
- Part of the “Entra” security suite, connecting with Global Secure Access and ID Governance.
Support & Community
Microsoft offers enterprise-tier support, detailed documentation, and a massive community of IT professionals. They actively contribute to the decentralized identity open-source community.
4. Google Wallet
Description: Google Wallet provides a highly inclusive and accessible platform for digital identity, catering to billions of Android users globally. It focus on versatility, allowing users to store everything from government IDs and health passes to digital car keys and boarding passes.
Key Features
- Android StrongBox Security: Leverages dedicated hardware on supported Android devices to protect identity and payment keys.
- Inclusive Global Reach: Designed to work across a vast range of device manufacturers and price points, not just premium phones.
- Smart Suggestion Engine: Automatically surface your boarding pass or ID when you arrive at an airport or a participating venue.
- Find My Device Integration: Allows for remote locking and wiping of identity data if the phone is lost or stolen.
- Verifiable Health Credentials: Secure storage for digital vaccination records and health insurance cards.
- Identity Pass Integration: Allows users to create a digital ID pass using their physical passport in participating regions.
- Cross-Google Integration: Syncs with Google Calendar and Assistant to provide a unified travel and identity experience.
Pros
- The most accessible identity wallet for the global population, supporting thousands of different Android devices.
- Extremely easy to set up, with many credentials automatically imported from Gmail.
- Strong integration with the broader Google ecosystem for a seamless “lifestyle” experience.
Cons
- Security levels can vary depending on the hardware quality of the specific Android device being used.
- The “open” nature of Android can occasionally lead to a less consistent user experience across different phone brands.
- Data privacy concerns associated with the broader Google advertising ecosystem may worry some users.
Platforms / Deployment
- Android / Wear OS
- Integrated system app
Security & Compliance
- Android StrongBox and TEE (Trusted Execution Environment) protection.
- GDPR and W3C Verifiable Credentials compliant.
Integrations & Ecosystem
- Deeply integrated with Google Search, Maps, and Gmail.
- Partnerships with major airlines and transit systems globally.
- Support for digital car keys with BMW, Hyundai, and other manufacturers.
- Connectivity with many US state DMV systems for digital driver’s licenses.
Support & Community
Google provides extensive consumer help centers and a robust developer platform for the Android ecosystem. They are a founding member of many digital identity and mobile payment standards groups.
5. ID.me Wallet
Description: ID.me is a leading identity network in the United States, used by millions to access government benefits and healthcare services. Its digital wallet allows users to verify their identity once and then “reuse” that verification across thousands of different public and private sites.
Key Features
- NIST IAL2 Compliance: Meets the high-level identity proofing standards required for access to the IRS and Social Security Administration.
- Community-Based Identity: Specific “cards” for military members, first responders, nurses, teachers, and students to access exclusive benefits.
- Multi-Channel Verification: Offers both a digital self-service path and a video-call path with a live “Video Chat Agent” for those who need help.
- Pre-Verified Network: Once a user is verified in the ID.me wallet, they can log into any partner site with a single click.
- In-Person Verification: Partnerships with retail locations (like UPS Stores) for users who prefer to verify their identity in person.
- Control Dashboard: A central location where users can see exactly which organizations have access to their data and revoke it at any time.
- Health & Rx Cards: Includes digital health credentials and prescription discount cards within the same wallet interface.
Pros
- The de-facto standard for accessing US government digital services, providing immediate and high-value utility.
- Exceptional “Reuse” capability; one verification unlocks thousands of discounts and services across the web.
- High success rates for identity proofing due to multiple verification methods (digital and human-assisted).
Cons
- Primarily focused on the United States market, with limited utility for international users.
- Some users have raised privacy concerns regarding the centralization of so much sensitive identity data in one private company.
- The requirement for a “selfie” and biometric scan can be a barrier for some privacy-conscious individuals.
Platforms / Deployment
- iOS / Android / Web
- Cloud-based SaaS + Mobile App
Security & Compliance
- NIST 800-63-3 IAL2 and AAL2 compliant.
- SOC 2 Type II, HIPAA, and CCPA certified.
Integrations & Ecosystem
- Integrated with over 30 US states and multiple federal agencies (IRS, SSA, VA).
- Partnerships with thousands of retailers for “Community” discounts.
- Connections to financial institutions for secure loan and bank account applications.
- Support for a wide range of healthcare portals and insurance providers.
Support & Community
ID.me provides 24/7 technical support and has a massive self-service knowledge base. They are one of the most recognizable names in the American digital identity landscape.
6. Ping Identity (PingOne Neo)
Description: Ping Identity is an enterprise leader that provides the “PingOne Neo” platform, a decentralized identity and digital wallet solution. It is designed for large organizations that want to offer their customers and employees a privacy-first, white-label identity experience.
Key Features
- Zero-Knowledge Biometrics: Uses advanced cryptography to verify a user’s identity without ever storing their actual biometric data on a server.
- White-Label Wallet: Allows companies to build their own branded identity wallet using Ping’s underlying technology.
- Orchestration Engine: A powerful drag-and-drop tool for creating complex identity verification workflows (e.g., check ID -> check age -> check background).
- Verifiable Credentials (VC): Full support for the W3C VC standard, ensuring credentials can be shared across different platforms.
- Identity Runtime Mesh: Provides continuous, real-time security signals to detect if an identity has been compromised during a session.
- Legacy System Bridge: Connects modern digital wallets with older, on-premise identity systems (like Active Directory).
- Dynamic Step-Up Authentication: Automatically asks for a biometric scan or wallet proof only when a high-risk transaction is detected.
Pros
- The most powerful option for large enterprises that need to manage millions of identities across complex global networks.
- Exceptional security features, including the newly acquired “Zero-Knowledge Biometrics” technology.
- Provides a level of customization and “brand control” that Apple or Google wallets cannot match.
Cons
- Highly complex to implement, requiring a skilled internal security and development team.
- The pricing model is geared toward large-scale enterprise deployments, making it expensive for small firms.
- Not a “consumer” wallet that you can just download; it is a platform used to build other wallets.
Platforms / Deployment
- iOS / Android / Web (via SDKs)
- Cloud-based SaaS / Hybrid
Security & Compliance
- ISO 27001, SOC 2 Type II, FIDO2, and GDPR compliant.
- Supports eIDAS 2.0 and the emerging PSD3 standards.
Integrations & Ecosystem
- Integrates with virtually every major enterprise software (SAP, Salesforce, Workday).
- Native support for all major IAM (Identity and Access Management) protocols.
- Extensive marketplace of “Integrations” for background checks, fraud detection, and biometrics.
- Deep ties to the FIDO Alliance for passwordless authentication.
Support & Community
Ping Identity offers world-class 24/7 enterprise support and professional services. They host “Identiverse,” one of the largest annual conferences for the identity industry.
7. Yoti
Description: Yoti is a “tech-for-good” company that offers a highly secure, reusable digital identity app. It is widely used in the UK and internationally for age verification, secure document signing, and as a digital alternative to physical ID cards.
Key Features
- Reusable Digital ID: Users verify once with a government document and a biometric selfie, then use the app to verify themselves anywhere Yoti is accepted.
- Anonymous Age Estimation: Uses AI to estimate a user’s age without requiring any personal documents, ideal for low-stakes age checks.
- Secure Document Signing: Includes a built-in feature for signing contracts and agreements with a verified identity.
- Private Attribute Sharing: Allows users to share a single “verified” fact (like “Over 18” or “Verified Name”) without revealing anything else.
- Yoti Key: A feature that turns the smartphone into a secure physical key for accessing offices or unlocking smart devices.
- Global Document Support: Capable of verifying over 6,000 different types of government-issued IDs from around the world.
- Transparent Ethics: Guided by a “Guardian Council” to ensure the company always prioritizes user privacy and ethical AI use.
Pros
- One of the most privacy-respecting platforms, with a business model that does not involve selling user data.
- Excellent for “Age Tech” and retail compliance, where fast and anonymous verification is required.
- Very easy for individuals to set up and use for both online and in-person verification.
Cons
- While growing, its network of “relying parties” is not yet as large as global giants like Google or Apple.
- Some users may find the “Age Estimation” AI to be less accurate than traditional document-based checks.
- The app is a third-party installation, which adds a layer of friction compared to native system wallets.
Platforms / Deployment
- iOS / Android
- Cloud-based SaaS + Mobile App
Security & Compliance
- SOC 2 Type II and ISO 27001 certified.
- Certified for the UK Digital Identity & Attributes Trust Framework (DIATF).
Integrations & Ecosystem
- Over 70 integrations with major SaaS platforms and e-commerce tools.
- Partnership with the UK Post Office for a co-branded digital identity.
- Support for a wide range of retail age-verification systems.
- API for developers to add “Verify with Yoti” to any web or mobile application.
Support & Community
Yoti provides dedicated business support and a comprehensive developer portal. They are known for their advocacy in the “Privacy-Preserving Technology” space.
8. Walt.id
Description: Walt.id is an open-source leader in the digital identity space, providing a holistic “identity and wallet” infrastructure. It is the preferred choice for developers and organizations that want to build custom, interoperable identity solutions without being tied to a specific vendor.
Key Features
- Full Open-Source Stack: The entire core infrastructure is available under the Apache 2.0 license, allowing for complete transparency and customization.
- Multi-Ecosystem Support: Can issue and verify credentials across many different blockchains, cloud environments, and trust frameworks.
- Wallet-as-a-Service: Offers a managed cloud platform for organizations that want the power of their infrastructure without managing servers.
- Universal SDKs: High-quality libraries for all major programming languages, making it easy to add identity features to any app.
- Interoperability First: Strictly follows W3C, ISO, and OpenID Connect standards to ensure credentials work everywhere.
- Modular Architecture: Users can pick and choose only the components they need, such as “Issuance,” “Verification,” or “Wallet.”
- eIDAS 2.0 Ready: Specifically designed to help European organizations comply with the new digital identity regulations.
Pros
- The ultimate “Developer’s Choice,” offering the most flexibility and control of any tool on this list.
- Open-source nature eliminates vendor lock-in and allows for extensive security auditing.
- Highly cost-effective for organizations that have the technical talent to manage the open-source stack.
Cons
- Requires significant technical knowledge to deploy and maintain the self-managed version.
- Lends itself more to B2B and “build-your-own” scenarios than to immediate consumer use.
- The “Community” support model may not be sufficient for enterprise organizations requiring strict SLAs.
Platforms / Deployment
- iOS / Android / Web
- Self-Managed / Cloud SaaS (Walt.id Cloud)
Security & Compliance
- Aligned with W3C, ISO 18013-5, and GDPR.
- Supports various decentralized identity (DID) methods and cryptographic formats.
Integrations & Ecosystem
- Integrations with major cloud providers (AWS, Google Cloud, Azure).
- Support for a wide range of decentralized storage and blockchain networks.
- Connectors for major IAM systems and identity verification providers.
- Used by government and educational institutions for building regional identity pilots.
Support & Community
Walt.id has a very active developer community on GitHub and Discord. They offer “Enterprise Support” and professional services for companies that need guaranteed assistance.
9. Folio
Description: Folio is a smart digital wallet designed to organize and protect all of a user’s essential documents, from IDs and passports to travel tickets and loyalty cards. It focuses on privacy through strong encryption and a clean, “timeline-based” user experience.
Key Features
- Smart ID Scanner: Uses advanced OCR to scan physical IDs and passports once, making the data instantly accessible for filling out forms.
- Travel Organizer: Automatically parses flight and hotel confirmation emails into a clean, searchable timeline within the wallet.
- AES 256-bit Encryption: Every document is individually encrypted with industry-standard protocols; even the Folio team cannot see your data.
- Expiry Alerts: Automatically notifies users when their passport, driver’s license, or insurance is about to expire.
- Secure Backup: Allows users to create an encrypted backup to restore their documents if they lose their phone.
- Offline Access: All documents and tickets are stored locally on the device for access during flights or in areas with poor signal.
- Privacy-First Design: The app does not track user identity or sell data, focusing purely on secure document management.
Pros
- Excellent for frequent travelers who need a single place to manage identity and trip logistics.
- Much more private than storing photos of IDs in a standard photo gallery app.
- The interface is exceptionally clean and intuitive, making it a great choice for non-technical users.
Cons
- It acts more as a “secure container” than a platform for sharing verified credentials with third parties.
- It does not have the same level of “official” government backing as the Apple or EUDI wallets.
- Some advanced features, like cloud backup and certain travel organizing tools, require a premium subscription.
Platforms / Deployment
- iOS / Android
- Mobile-first App
Security & Compliance
- SOC 2 and ISO 27001 certified.
- Uses multilayer AES 256-bit encryption for all stored data.
Integrations & Ecosystem
- Integrates with email providers to automatically import travel bookings.
- Support for a wide range of digital “passes” and loyalty card formats.
- Connects with native device biometrics for app-level locking.
- Built to interact with standard airline and event ticketing systems.
Support & Community
Folio provides standard email-based support and a helpful knowledge base. They are popular among the “digital nomad” and frequent flyer communities.
10. Gen Digital (Evernym / Connect.Me)
Description: Backed by the security giant Gen Digital (the parent company of Norton and Avast), Evernym and its “Connect.Me” wallet are pioneers in the decentralized identity space. They provide a highly stable, privacy-focused environment for managing verifiable credentials.
Key Features
- Privacy-First (SSI): Based on the Sovrin network, ensuring that no central authority can track your identity usage or turn off your identity.
- Enterprise-Ready Infrastructure: Provides the “backend” that many other companies use to build their own identity solutions.
- Connect.Me App: A clean, easy-to-use consumer wallet that allows individuals to receive and store credentials from various issuers.
- Peer-to-Peer (P2P) Messaging: Allows for secure, encrypted communication between the user and the organizations that issue or verify their data.
- Standard-Based Interoperability: Full support for Hyperledger Indy and Aries standards, ensuring global compatibility.
- Guardian Feature: Allows a trusted person (like a parent) to help manage the identity of someone else (like a child or elderly relative).
- Automated Revocation Check: Instantly checks if a credential is still valid without the verifier needing to contact the original issuer.
Pros
- Benefit from the massive security expertise and financial backing of Gen Digital.
- One of the most mature and “battle-tested” decentralized identity platforms in existence.
- Strong focus on ethical data use and preventing large-scale data breaches through decentralization.
Cons
- The “Connect.Me” consumer app is functional but has not seen as much visual polish as Apple or Google wallets.
- Decentralized identity is still a new concept for many consumers, leading to a steeper learning curve.
- To get the full benefit, you need to interact with organizations that are specifically part of the “Evernym” or “Sovrin” ecosystems.
Platforms / Deployment
- iOS / Android / Web
- Cloud-based SaaS + Mobile App
Security & Compliance
- FIPS 140-2, GDPR, HIPAA, and ISO standards compliant.
- Built on a “Privacy-by-Design” architecture.
Integrations & Ecosystem
- Strong presence in the financial services and insurance industries.
- Part of the “Global Identity” efforts via the Sovrin Foundation.
- Integrates with enterprise IAM systems via the “Evernym Verity” platform.
- Partnerships with a wide range of government and healthcare pilots globally.
Support & Community
Gen Digital provides professional enterprise-grade support and services. They are a founding member of the decentralized identity movement and maintain a strong presence in standards bodies.
Comparison Table (Top 10)
| Tool Name | Best For | Platform(s) Supported | Deployment | Standout Feature |
| 1. European Digital Identity Wallet | EU Citizens & Public Services | iOS, Android, Web | State-SaaS | Legal Cross-Border Status |
| 2. Apple Wallet | iOS Users & TSA Travel | iOS, Apple Watch | Hardware-Integrated | Secure Enclave Protection |
| 3. Microsoft Entra Verified ID | Corporate & Employee Identity | iOS, Android | Azure SaaS | Microsoft Ecosystem Sync |
| 4. Google Wallet | Global Android Users | Android, Wear OS | Integrated App | Inclusive Global Support |
| 5. ID.me Wallet | US Gov Access & Discounts | iOS, Android, Web | Cloud SaaS | Video-Call Verification |
| 6. Ping Identity | Large-Scale Enterprise White-Label | iOS, Android, Web | Cloud / Hybrid | Zero-Knowledge Biometrics |
| 7. Yoti | Age Tech & Privacy-First Users | iOS, Android | Cloud SaaS | Anonymous Age Estimation |
| 8. Walt.id | Developers & Open-Source Projects | iOS, Android, Web | Self-Managed | Full Apache 2.0 Stack |
| 9. Folio | Travel & Personal Doc Storage | iOS, Android | Mobile App | Timeline Travel Organizer |
| 10. Gen Digital | Decentralized SSI & High Security | iOS, Android, Web | Cloud SaaS | Backed by Norton/Avast |
Evaluation & Scoring of Digital Identity Wallets
The scoring below is a comparative model intended to help shortlisting. Each criterion is scored from 1–10, then a weighted total from 0–10 is calculated using the weights listed. These are analyst estimates based on typical fit and common workflow requirements, not public ratings.
Weights:
- Core features – 25%
- Ease of use – 15%
- Integrations & ecosystem – 15%
- Security & compliance – 10%
- Performance & reliability – 10%
- Support & community – 10%
- Price / value – 15%
| Tool Name | Security (25%) | Privacy (20%) | Interoperability (15%) | Ecosystem (15%) | UX (15%) | Regulatory (10%) | Weighted Total |
| 1. EUDI Wallet | 9 | 10 | 10 | 9 | 7 | 10 | 9.1 |
| 2. Apple Wallet | 10 | 9 | 7 | 10 | 10 | 9 | 9.2 |
| 3. MS Entra Verified ID | 9 | 9 | 9 | 8 | 7 | 9 | 8.4 |
| 4. Google Wallet | 8 | 8 | 9 | 10 | 9 | 9 | 8.7 |
| 5. ID.me Wallet | 8 | 7 | 8 | 10 | 8 | 10 | 8.3 |
| 6. Ping Identity | 10 | 9 | 9 | 7 | 7 | 10 | 8.8 |
| 7. Yoti | 9 | 10 | 8 | 8 | 9 | 9 | 8.9 |
| 8. Walt.id | 9 | 10 | 10 | 6 | 6 | 9 | 8.2 |
| 9. Folio | 8 | 9 | 6 | 6 | 10 | 7 | 7.7 |
| 10. Gen Digital | 9 | 10 | 10 | 7 | 7 | 9 | 8.7 |
How to interpret the scores:
- Use the weighted total to shortlist candidates, then validate with a pilot.
- A lower score can mean specialization, not weakness.
- Security and compliance scores reflect controllability and governance fit, because certifications are often not publicly stated.
- Actual outcomes vary with assembly size, team skills, templates, and process maturity.
Which Digital Identity Wallet Tool Is Right for You?
Solo / Personal Use
If you are an iPhone user, Apple Wallet is the most seamless and secure starting point for your driver’s license and travel. Android users should look to Google Wallet for a similar integrated experience. For those who want maximum privacy and document organization without the ecosystem lock-in, Folio is an excellent choice.
EU Citizens and Residents
For anyone living or working in Europe, the European Digital Identity Wallet is essentially mandatory for the next phase of digital life. It is the only tool that will be universally accepted for both high-level government tasks and everyday cross-border activities.
US Government and Benefits
If you need to access the IRS, Social Security, or VA benefits in the United States, the ID.me Wallet is a requirement. It also provides the best “perks” system for specific communities like veterans or healthcare workers.
Small and Mid-Sized Businesses (SMBs)
SMBs that want to implement identity verification without a massive budget should look at Yoti or the managed version of Walt.id. These platforms offer “plug-and-play” features that can be added to a website or app in days.
Global Enterprises
Large organizations with thousands of employees and a complex security stack should prioritize Ping Identity or Microsoft Entra Verified ID. These tools offer the administrative controls and orchestration depth required for enterprise security.
Developers and Tech-Savvy Teams
If you want to build the future of identity without being reliant on a single software vendor, Walt.id is the clear winner. Its open-source stack allows you to create highly customized, future-proof wallets for any industry.
Privacy Purists
Users who are deeply concerned about “Big Tech” surveillance should look toward Gen Digital (Connect.Me) or Walt.id. These tools are built on the “Self-Sovereign” philosophy, ensuring that your data is never stored on a central server.
Frequently Asked Questions (FAQs)
What is the difference between a digital wallet and a digital identity wallet?
A standard digital wallet (like Google Pay) primarily stores financial information like credit cards. A digital identity wallet stores verified personal information (like a passport or diploma) that can be used for legal identification.
Is my identity data stored on a central server?
For most tools on this list, like Apple Wallet or EUDI, the data is stored only on your device. Decentralized wallets ensure that even the provider cannot see or access your identity without your permission.
What happens if I lose my phone?
Most wallets allow for secure, encrypted backups. If you lose your device, you can restore your identity on a new phone using a recovery key or by re-authenticating with the original issuer.
Can I use these wallets to travel internationally?
Currently, most digital IDs are for domestic use (e.g., TSA in the US or cross-border in the EU). However, global standards like the ISO mDL are paving the way for full digital international travel in the near future.
What is “Selective Disclosure”?
This is a privacy feature where you can prove a specific fact (e.g., “I am over 18”) without revealing your actual birth date, full name, or address to the person checking your ID.
Do I need an internet connection to show my ID?
Leading wallets like Apple Wallet, Google Wallet, and Folio allow you to present your ID offline using NFC or QR code technology, ensuring you can verify yourself anywhere.
Are these digital identities legally as valid as a physical ID?
In regions like the EU (under eIDAS) and participating US states, a digital ID is legally equivalent to its physical counterpart for certain tasks like age checks and government services.
Can someone steal my digital identity?
Stealing a digital identity is much harder than stealing a physical one, as these wallets are protected by device-level biometrics (Face ID) and high-level hardware encryption.
How do I add my ID to these wallets?
Most wallets allow you to scan your physical document using your phone’s camera and then verify it with a “biometric selfie” to ensure the document belongs to you.
Will digital wallets replace physical IDs entirely?
While we are moving toward a “digital-first” world, most experts recommend carrying a physical ID as a backup during the transitional years until digital readers are ubiquitous everywhere.
Conclusion
The shift toward digital identity wallets represents one of the most significant changes in the relationship between individuals and their data. Whether it is the state-backed security of the European Digital Identity Wallet, the enterprise power of Microsoft Entra, or the developer freedom of Walt.id, these tools are creating a more secure and efficient way to navigate the digital world. By adopting these wallets, users gain not only convenience but also a powerful new layer of privacy and protection in an increasingly complex online landscape.