Introduction
Device fingerprinting has emerged as a cornerstone of modern cybersecurity, providing a non-intrusive method to identify and track visitors without relying on traditional cookies. By aggregating hardware signals, browser configurations, and network telemetry, these tools generate a high-entropy identifier unique to a specific device. This technical fingerprint remains persistent even when a user clears their cache, uses incognito mode, or switches IP addresses via a VPN. For organizations managing high-risk transactions or sensitive user data, device fingerprinting offers a critical layer of defense against account takeovers, bot-driven credential stuffing, and sophisticated multi-accounting fraud.
The strategic deployment of these tools allows security engineers and data scientists to build a high-fidelity “trust profile” for every interaction. Unlike static authentication methods, device fingerprinting is dynamic; it analyzes the subtle nuances of how a device renders graphics, handles audio processing, and lists its system fonts. This creates a “digital DNA” that is nearly impossible for automated scripts to replicate accurately. As we transition toward a cookieless future, the ability to maintain session integrity and detect suspicious anomalies through device-level intelligence has become an essential competency for any robust AIOps or DevSecOps framework.
Best for: Fraud analysts, security engineers, and e-commerce platform owners who need to prevent bot attacks, account abuse, and payment fraud while maintaining a low-friction user experience.
Not ideal for: Simple informational websites or low-risk applications where basic session management is sufficient and the overhead of integrating a sophisticated fraud detection API is not justified.
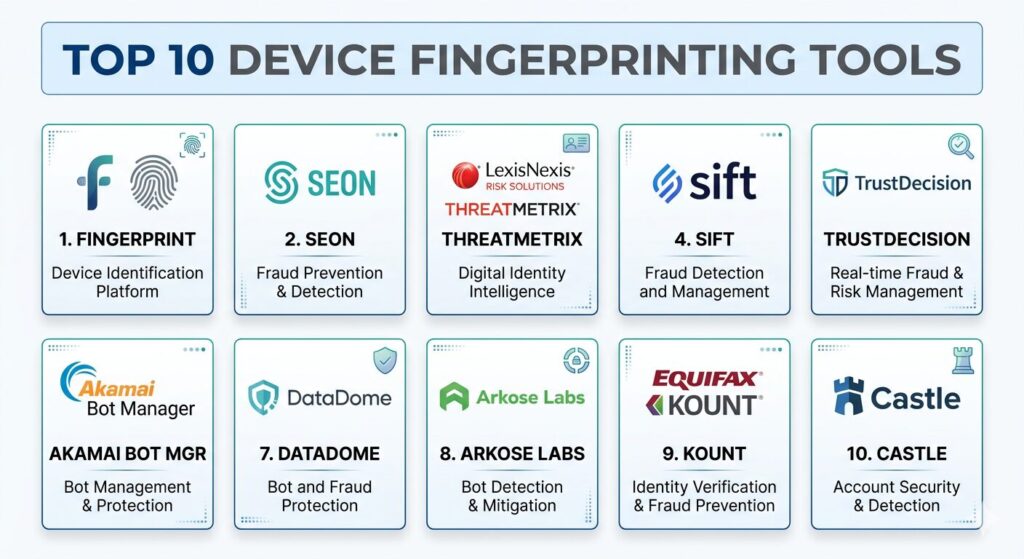
Key Trends in Device Fingerprinting Tools
A significant shift is occurring toward “behavioral fingerprinting,” which combines traditional hardware signals with the way a user interacts with their device—such as typing rhythm and mouse movements. This creates a multi-modal identity that is much harder to spoof than hardware parameters alone. Additionally, as privacy regulations like GDPR and CCPA tighten, platforms are moving toward “privacy-first” fingerprinting. These methods use anonymized hashes that can identify a recurring device without exposing personal identifiable information (PII), striking a balance between security and regulatory compliance.
Artificial Intelligence is also playing a larger role in fingerprinting persistence. Modern engines use machine learning to “heal” fingerprints; if a user updates their browser version or changes a minor setting, the AI recognizes the underlying device patterns and maintains the link to the original ID. We are also seeing the rise of edge-based fingerprinting, where the identification logic is processed on CDN edges rather than the origin server. This reduces latency to near-zero, allowing for real-time bot mitigation at the very first point of contact.
How We Selected These Tools
The tools featured in this list were selected based on their technical robustness in high-stakes production environments. We prioritized platforms that demonstrate high “stickiness” or persistence—the ability to recognize a device accurately over long periods and across various attempts to hide its identity. Market mindshare was a significant factor, as platforms with larger data networks benefit from “network effects,” where a fraudster identified on one site can be instantly flagged across all other sites using the same tool.
Technical integration was also a key metric. We looked for tools that offer lightweight SDKs and well-documented APIs, ensuring they can be seamlessly woven into a CI/CD pipeline without introducing performance bottlenecks. Finally, we evaluated the depth of the “signal stack”—the variety of data points collected, ranging from WebGL rendering to TCP/IP header analysis. The goal was to provide a diverse list that serves everyone from lean startups needing a simple API to global enterprises requiring a full-scale fraud orchestration engine.
1. Fingerprint (formerly FingerprintJS)
Fingerprint is the industry standard for developer-centric device identification. Originally gaining fame as an open-source project, the Pro version offers a highly accurate, long-lived identifier that is resilient to browser updates and privacy-clearing actions. It is designed for engineers who want a clean, high-performance API that returns a stable ID in milliseconds.
Key Features
The platform utilizes a combination of browser fingerprinting, cookies, and local storage to maximize identification accuracy. It features a unique “Probability Score” that helps developers understand the confidence level of a match. The Pro version includes advanced bot detection that can distinguish between human users and automated scripts like Playwright or Puppeteer. It provides comprehensive support for web, iOS, and Android, ensuring a cross-platform view of the user. Additionally, its dashboard offers detailed insights into the specific signals used to generate each unique fingerprint.
Pros
Extremely easy to integrate with a single line of JavaScript. It offers one of the highest accuracy rates in the market, often exceeding 99% for recurring visitors.
Cons
The cost scales rapidly with the number of identifications, which can be expensive for high-traffic sites. Some of the most advanced features are gated behind higher pricing tiers.
Platforms and Deployment
Web (JavaScript SDK), iOS, and Android. Cloud-based API delivery.
Security and Compliance
SOC 2 Type II certified and fully compliant with GDPR and CCPA via anonymized hashing.
Integrations and Ecosystem
Native integrations with major cloud platforms and a robust set of webhooks for real-time fraud workflows.
Support and Community
Excellent developer documentation and an active community surrounding its open-source version.
2. SEON
SEON is an “all-in-one” fraud prevention platform that treats device fingerprinting as a core pillar of its broader risk engine. It is particularly effective because it combines device data with social media profiling and email/phone lookups to create a holistic view of a user’s digital footprint.
Key Features
The device fingerprinting module collects over 100 parameters, including hardware details, software versions, and network anomalies. It features a sophisticated “Rule Engine” where security teams can create custom logic (e.g., “block if the user is using a VPN and has a high-risk device fingerprint”). It includes a “social lookup” tool that checks if an email or phone number is associated with 50+ social networks. The platform provides real-time risk scores that can be used to trigger MFA or block transactions. It also offers a “GUI-based” dashboard that is accessible to fraud analysts, not just developers.
Pros
Provides a complete fraud-fighting suite beyond just device ID. The ability to link device data with social media presence significantly reduces false positives.
Cons
The sheer volume of data can be overwhelming for teams just looking for a simple device identifier. The pricing model is geared toward holistic fraud prevention rather than standalone fingerprinting.
Platforms and Deployment
Web, iOS, and Android SDKs. Cloud-based deployment.
Security and Compliance
Adheres to strict ISO 27001 standards and provides granular control over data retention.
Integrations and Ecosystem
Strong support for Shopify, Magento, and various payment gateways.
Support and Community
Offers 24/7 technical support and has a strong reputation for hands-on onboarding.
3. ThreatMetrix (LexisNexis)
ThreatMetrix is an enterprise-grade solution that leverages the “Digital Identity Network,” one of the largest shared databases of anonymized user data in the world. It is a heavy-duty tool designed for financial institutions and global retailers that need to identify patterns of organized cybercrime across millions of transactions.
Key Features
The platform utilizes “SmartID” technology to recognize returning devices even when users clear cookies or use private browsing. It features behavioral biometrics that track how a user interacts with a page to detect bot behavior. The Digital Identity Network allows for “crowdsourced” security, where a device flagged on a bank site is immediately recognized as high-risk on an e-commerce site. It provides deep analysis of proxy and VPN usage, often uncovering the “true” IP address behind a spoofing attempt. The system also includes a robust case management tool for fraud investigators.
Pros
Access to a massive global intelligence network provides unparalleled detection of known bad actors. It is highly effective at stopping large-scale, coordinated bot attacks.
Cons
The integration process is complex and usually requires a significant professional services engagement. The pricing is strictly enterprise-level and opaque.
Platforms and Deployment
Web and mobile SDKs. Hybrid deployment options are available for highly regulated industries.
Security and Compliance
Top-tier compliance with banking and financial regulations globally.
Integrations and Ecosystem
Integrates deeply with enterprise IAM (Identity and Access Management) and banking cores.
Support and Community
Dedicated account managers and specialized fraud consulting services.
4. Sift
Sift is a “Digital Trust & Safety” platform that uses machine learning to score the risk of every user interaction. Their device fingerprinting tool, known as “Sift Device ID,” is a critical input into their ML models, helping to link seemingly unrelated accounts to a single fraud ring.
Key Features
Sift uses a persistent device ID that stays consistent across multiple sessions and IP changes. The core of the platform is its “Global Trust Network,” which learns from over 70 billion events per month. It features a “Workflow Engine” that allows teams to automate responses based on device risk (e.g., “allow,” “block,” or “challenge”). The platform includes behavioral analysis that tracks user journeys to find anomalies. It also provides a visual “Link Analysis” tool that allows fraud analysts to see the connections between different accounts, devices, and payment methods.
Pros
The machine learning engine is exceptionally good at adapting to new, “zero-day” fraud patterns. The user interface is one of the most intuitive for fraud analysts.
Cons
The “black box” nature of machine learning can sometimes make it difficult to explain exactly why a specific device was flagged. It requires a high volume of data to reach peak accuracy.
Platforms and Deployment
Web and mobile SDKs. Cloud-based SaaS.
Security and Compliance
SOC 2 Type II certified with a strong focus on maintaining user privacy.
Integrations and Ecosystem
Excellent integrations with e-commerce platforms like Shopify and BigCommerce.
Support and Community
Very active community and extensive training resources via “Sift University.”
5. TrustDecision
TrustDecision is an enterprise fraud platform that specializes in high-risk environments like iGaming and fintech. It is known for its “spoof-resistant” fingerprinting technology, which is specifically tuned to detect emulators, virtual machines, and sophisticated device-spoofing tools.
Key Features
The platform features a “Device Health” check that looks for rooted or jailbroken mobile devices. It uses a proprietary “persistent ID” that remains stable even if the browser is reinstalled or the OS is updated. It includes built-in emulator detection, which is critical for mobile-first apps that are targeted by automated click farms. The system provides a real-time decision engine that combines device intelligence with transactional data. It also offers a “Graph Database” view to help investigators visualize and dismantle complex fraud networks.
Pros
Particularly strong in the mobile space, with deep detection of mobile-specific fraud tactics. It provides very low latency, making it suitable for real-time transaction approval.
Cons
The product documentation is less accessible than developer-first tools like Fingerprint. It is primarily focused on the Asian and European markets.
Platforms and Deployment
Web, iOS, Android, and mini-programs (like WeChat). Cloud-based.
Security and Compliance
Compliant with major global data protection laws and payment security standards.
Integrations and Ecosystem
Strong API focus for custom integrations into banking and gaming platforms.
Support and Community
Offers localized support in multiple regions and a dedicated technical account team.
6. Akamai Bot Manager
As a leader in the Content Delivery Network (CDN) space, Akamai offers a Bot Manager that utilizes device fingerprinting at the “edge.” This allows it to identify and mitigate bot traffic before it ever reaches your application servers, significantly reducing infrastructure costs and improving performance.
Key Features
The platform uses “Edge Intelligence” to collect device signals during the initial TLS handshake and HTTP request phase. It features a massive “Bot Directory” that classifies thousands of known bots as either “good” (search engines) or “bad” (scrapers). It includes behavioral biometrics that analyze keystroke patterns and touch events. The system can apply different “responses” to suspicious devices, such as serving a CAPTCHA, slowing down the connection (tarpitting), or serving fake data. It also provides deep visibility into bot traffic trends across your entire digital estate.
Pros
Stopping threats at the edge prevents server-side resource exhaustion. It is ideal for massive-scale enterprises that already use Akamai’s CDN.
Cons
It is not a standalone tool; you typically need to be part of the Akamai ecosystem to use it. The setup and tuning of bot rules can be highly technical.
Platforms and Deployment
Edge-based deployment (CDN).
Security and Compliance
World-class security infrastructure with comprehensive compliance certifications.
Integrations and Ecosystem
Integrates natively with Akamai’s WAF (Web Application Firewall) and other security products.
Support and Community
Enterprise-grade support with a 24/7 Security Operations Center (SOC).
7. DataDome
DataDome is a specialized bot protection and online fraud prevention solution that prides itself on being “invisible” to the end-user. It uses advanced device fingerprinting to protect against account takeovers, scraping, and layer-7 DDoS attacks in real time.
Key Features
The platform utilizes a 100% automated detection engine that makes decisions in under 2 milliseconds. It uses a combination of client-side fingerprinting and server-side behavior analysis. The system is designed to detect “low and slow” bot attacks that try to mimic human behavior. It features a transparent dashboard that shows exactly why a request was blocked. DataDome also includes its own privacy-focused CAPTCHA that is only shown to devices that are highly likely to be bots, minimizing friction for real users.
Pros
The automation is highly effective, requiring very little manual intervention from security teams. The “time-to-protect” is incredibly fast due to its optimized architecture.
Cons
It is strictly focused on bot and fraud prevention; it doesn’t provide the broader “user identity” tracking that some other tools offer. It can be more expensive than generalist security tools.
Platforms and Deployment
Web, mobile SDKs, and integrations for all major web servers (NGINX, Apache) and CDNs.
Security and Compliance
GDPR compliant and focuses on minimizing the collection of PII.
Integrations and Ecosystem
Extensive integrations with CDNs like Cloudflare, AWS CloudFront, and Fastly.
Support and Community
Strong technical support and a library of research on emerging bot threats.
8. Arkose Labs
Arkose Labs takes a unique “economic” approach to fraud. It uses device fingerprinting to identify suspicious traffic and then presents “impossible-to-automate” challenges that bankrupt the business model of bot operators while remaining easy for legitimate human users.
Key Features
The platform features “Arkose Match,” a device profiling tool that detects emulators, spoofed headers, and virtual machines. It uses a “Global Intelligence Network” to share risk signals across its customer base. The standout feature is its “Challenge-Response” mechanism, which uses interactive puzzles that are specifically designed to be difficult for AI and computer vision to solve. It provides a “fraud-loss guarantee,” showing high confidence in its ability to stop attacks. The system also includes detailed telemetry on how “attackers” interact with the challenges.
Pros
Effectively stops bots by making the cost of the attack higher than the potential reward. The challenges are much more user-friendly than traditional, grainy CAPTCHAs.
Cons
The interactive challenges can still introduce some friction for high-risk human users. It is an enterprise solution with a price point to match.
Platforms and Deployment
Web and mobile SDKs. Cloud-based.
Security and Compliance
High-level enterprise security compliance and privacy protections.
Integrations and Ecosystem
Integrates well with major IAM providers and e-commerce stacks.
Support and Community
Provides a dedicated “Security Operations Center” that monitors client traffic for emerging threats.
9. Kount (An Equifax Company)
Kount is a long-standing leader in the fraud space, now backed by the massive data resources of Equifax. It combines device fingerprinting with vast identity and credit data to provide “Identity Trust” scoring for payments and account creation.
Key Features
The platform uses the “Omniscore” machine learning engine to provide a single risk score for every transaction. It features “Link Analysis” to find connections between devices, email addresses, and physical shipping locations. The device fingerprinting module is specifically designed to work across the entire customer journey, from login to checkout. It includes a robust “Policy Engine” that allows businesses to set different risk thresholds for different regions or product types. Since its acquisition by Equifax, it also integrates broader credit and identity data into its risk assessments.
Pros
The combination of device ID and Equifax’s identity data is extremely powerful for financial services. It is highly effective at reducing chargebacks in e-commerce.
Cons
The user interface can feel a bit dated compared to newer SaaS competitors. The integration can be more data-heavy, requiring more effort to get the best results.
Platforms and Deployment
Web and mobile SDKs. Cloud-based.
Security and Compliance
Compliant with PCI DSS, GDPR, and other major financial regulations.
Integrations and Ecosystem
Deep integrations with major payment processors and e-commerce platforms like Magento.
Support and Community
Strong enterprise support and a large network of professional fraud analysts.
10. Castle
Castle is a modern, developer-friendly security platform that focuses on protecting user accounts from takeovers and automated abuse. It is known for its “passive” fingerprinting approach, which requires no user interaction and has a minimal impact on page load times.
Key Features
The platform features “Session Intelligence,” which tracks the entire lifecycle of a user session, not just a single point in time. It uses device fingerprinting to detect “impossible travel” (e.g., a device logging in from London and then 10 minutes later from New York). It provides a simple API for “risk-based authentication,” allowing developers to trigger MFA only when the device fingerprint or behavior is suspicious. The dashboard offers a very clean “Timeline View” of all security events related to a specific user. It also includes automated detection of leaked credentials.
Pros
The implementation is very clean and aligns perfectly with modern DevSecOps workflows. It is highly effective at reducing “MFA fatigue” by only challenging high-risk sessions.
Cons
It is less focused on payment fraud and more on account security. The free tier is somewhat limited for growing applications.
Platforms and Deployment
Web and mobile SDKs. Cloud-based API.
Security and Compliance
SOC 2 Type II certified and GDPR compliant.
Integrations and Ecosystem
Native integrations with Segment, Okta, and various backend languages via official libraries.
Support and Community
Responsive support and a very active Slack community for developers and security pros.
Comparison Table
| Tool Name | Best For | Platform(s) Supported | Deployment | Standout Feature | Public Rating |
| 1. Fingerprint | Developer Teams | Web, iOS, Android | Cloud | 99.5% ID Accuracy | 4.8/5 |
| 2. SEON | SMB / Fraud Suite | Web, Mobile, API | Cloud | Social Media Lookup | 4.7/5 |
| 3. ThreatMetrix | Enterprise Banking | Web, Mobile, SDK | Hybrid | Digital Identity Network | 4.5/5 |
| 4. Sift | ML-Driven Trust | Web, Mobile, API | Cloud | Graph Link Analysis | 4.6/5 |
| 5. TrustDecision | iGaming / Mobile | Web, iOS, Android | Cloud | Emulator Detection | 4.4/5 |
| 6. Akamai Bot Mgr | Edge Security | CDN / Edge | Edge | Zero-Latency Mitigation | 4.7/5 |
| 7. DataDome | Bot Protection | Web, Mobile, CDN | Hybrid | 100% Automated Logic | 4.8/5 |
| 8. Arkose Labs | High-Stake Auth | Web, Mobile | Cloud | Economic Disincentives | 4.5/5 |
| 9. Kount | E-commerce / PMT | Web, Mobile | Cloud | Equifax Data Linkage | 4.3/5 |
| 10. Castle | SaaS Account Sec | Web, Mobile, API | Cloud | Passive Session Intel | 4.6/5 |
Evaluation & Scoring of Device Fingerprinting Tools
The scoring below is a comparative model intended to help shortlisting. Each criterion is scored from 1–10, then a weighted total from 0–10 is calculated using the weights listed. These are analyst estimates based on typical fit and common workflow requirements, not public ratings.
Weights:
- Core features – 25%
- Ease of use – 15%
- Integrations & ecosystem – 15%
- Security & compliance – 10%
- Performance & reliability – 10%
- Support & community – 10%
- Price / value – 15%
| Tool Name | Core (25%) | Ease (15%) | Integrations (15%) | Security (10%) | Performance (10%) | Support (10%) | Value (15%) | Weighted Total |
| 1. Fingerprint | 10 | 10 | 9 | 9 | 10 | 9 | 8 | 9.35 |
| 2. SEON | 9 | 9 | 10 | 9 | 9 | 9 | 9 | 9.15 |
| 3. ThreatMetrix | 10 | 5 | 8 | 10 | 8 | 9 | 6 | 8.10 |
| 4. Sift | 9 | 8 | 9 | 9 | 9 | 10 | 7 | 8.65 |
| 5. TrustDecision | 9 | 7 | 8 | 9 | 9 | 8 | 8 | 8.25 |
| 6. Akamai Bot Mgr | 9 | 6 | 7 | 10 | 10 | 9 | 7 | 8.20 |
| 7. DataDome | 10 | 8 | 9 | 9 | 10 | 8 | 7 | 8.85 |
| 8. Arkose Labs | 8 | 7 | 8 | 9 | 8 | 9 | 7 | 7.85 |
| 9. Kount | 9 | 7 | 8 | 9 | 8 | 8 | 8 | 8.15 |
| 10. Castle | 8 | 9 | 9 | 9 | 9 | 9 | 9 | 8.70 |
How to interpret the scores:
- Use the weighted total to shortlist candidates, then validate with a pilot.
- A lower score can mean specialization, not weakness.
- Security and compliance scores reflect controllability and governance fit, because certifications are often not publicly stated.
- Actual outcomes vary with assembly size, team skills, templates, and process maturity.
Which Device Fingerprinting Tool Is Right for You?
Solo / Freelancer
If you are an independent developer or a small startup, Fingerprint or Castle are your best options. They offer “plug-and-play” simplicity with high accuracy and transparent pricing, allowing you to secure your app in minutes without needing a dedicated security team.
SMB
For small to medium businesses that need broader protection, SEON provides the best value. It doesn’t just give you a device ID; it gives you a complete fraud toolkit that includes social and email verification, which is often more useful for manual review processes.
Mid-Market
Growing platforms with high transaction volumes should look at Sift or DataDome. These tools offer the machine learning capabilities and automated response logic necessary to handle increasing levels of sophisticated bot traffic without scaling your internal headcount.
Enterprise
For global enterprises, particularly in the financial sector, ThreatMetrix (LexisNexis) is the gold standard. The depth of their global identity network is unmatched, making it the most reliable choice for identifying professional fraud rings operating across multiple countries.
Budget vs Premium
If budget is the primary concern, start with the open-source version of Fingerprint or Castle’s free tier. For those willing to pay a premium for total protection, Akamai Bot Manager and Arkose Labs offer “platinum” levels of security and support.
Feature Depth vs Ease of Use
Fingerprint wins on ease of use, while SEON and Sift win on feature depth. If you have the engineering resources to build your own logic, go with a pure identification tool; if you want the platform to make the decisions for you, choose a broader fraud engine.
Integrations & Scalability
DataDome and Akamai are the winners here because they integrate at the CDN level. This means they scale automatically with your traffic and protect your infrastructure at the edge, which is vital for high-growth SaaS and e-commerce companies.
Security & Compliance Needs
All listed tools are secure, but ThreatMetrix and Kount have a longer track record in highly regulated environments like banking. If your compliance needs are strictly focused on GDPR, Fingerprint and Castle offer the most transparent “privacy-first” implementations.
Frequently Asked Questions (FAQs)
1. How is device fingerprinting different from cookies?
Cookies are small files stored on the user’s browser that can be easily deleted or blocked. Device fingerprinting collects technical attributes of the hardware and software itself, making the identification persistent even if the user attempts to hide their identity.
2. Does device fingerprinting work in Incognito Mode?
Yes. Modern fingerprinting tools use signals like canvas rendering, system fonts, and hardware specifications that are not hidden by Incognito or Private browsing modes.
3. Can a device fingerprint change?
Yes, if a user updates their operating system or installs a new version of their browser, some signals will change. However, advanced tools like Fingerprint Pro use AI to “fuzzy match” these changes and keep the unique ID consistent.
4. Is device fingerprinting compliant with GDPR?
It can be. While it is more persistent than cookies, it is compliant as long as the data is used for “legitimate interests” like fraud prevention and the data is properly anonymized and hashed so it cannot be linked back to a real name without consent.
5. Can fraudsters spoof their device fingerprint?
Yes, sophisticated fraudsters use “anti-detect” browsers. However, top-tier tools like TrustDecision and DataDome are specifically designed to detect the subtle inconsistencies and “leaks” that these spoofing tools create.
6. Does fingerprinting impact website performance?
Most modern SDKs are asynchronous and lightweight, meaning they load in the background without slowing down the initial page render. Edge-based solutions like Akamai have zero impact on the origin server’s performance.
7. Is device fingerprinting 100% accurate?
No tool is 100% accurate, but the best in the industry achieve over 99% accuracy. Accuracy is measured by how often the tool can correctly identify a returning device after it has attempted to clear its identity.
8. Can I use device fingerprinting for marketing?
While technically possible, most providers in this list focus on security and fraud. Using fingerprinting for marketing is subject to much stricter privacy regulations and is generally discouraged compared to its use in security.
9. How many signals does a fingerprinting tool collect?
Basic tools may collect 20-30 signals, while enterprise engines like SEON or ThreatMetrix collect over 100, ranging from screen resolution and battery level to detailed TCP/IP packet headers.
10. Do I need to inform users about device fingerprinting?
Yes. Most privacy regulations require you to disclose the use of tracking and security technologies in your privacy policy, even if they are used solely for the purpose of fraud prevention.
Conclusion
Implementing a robust device fingerprinting strategy is no longer optional for organizations operating in the digital-first economy. As automated attacks become more sophisticated and traditional tracking methods like third-party cookies are phased out, the ability to identify a device through its unique technical signature has become a fundamental security requirement. The tools reviewed here represent the pinnacle of current identification technology, ranging from lean, developer-first APIs to massive global intelligence networks. Choosing the right partner depends on your specific risk profile, technical maturity, and the scale of your operations. However, the end goal remains the same: creating a secure environment where legitimate users can interact without friction, while bad actors and automated bots are identified and stopped at the threshold. Investing in high-fidelity device intelligence is not just about stopping fraud; it is about protecting your brand’s reputation and ensuring the long-term integrity of your digital ecosystem in an increasingly complex threat landscape.