Introduction
Confidential computing represents the final frontier of data protection, addressing the vulnerability of “data in use.” While traditional security measures have long protected data at rest (on disks) and data in transit (across networks), confidential computing ensures that sensitive information remains encrypted even while being processed in a computer’s memory. This is achieved through hardware-based Trusted Execution Environments (TEEs), often referred to as “enclaves,” which isolate code and data from the rest of the system—including the operating system, hypervisor, and even the cloud service provider itself. For organizations handling high-stakes workloads like financial transactions, medical records, or proprietary AI models, this technology provides a “zero-trust” execution layer that is cryptographically verifiable.
The adoption of confidential computing is no longer a niche requirement but a strategic imperative for the modern enterprise. As organizations migrate their most sensitive intellectual property to multi-cloud and hybrid environments, the risk of insider threats and infrastructure compromises has grown exponentially. Confidential computing platforms facilitate secure multi-party data collaboration, enabling different entities to combine datasets for analysis without ever exposing the underlying raw data to one another. By shifting the trust from human administrators to silicon-based hardware roots of trust, these platforms allow businesses to maintain absolute data sovereignty while still benefiting from the scalability and flexibility of the public cloud.
Best for: Highly regulated industries such as banking, healthcare, and defense, as well as AI developers who need to protect large-scale proprietary models and sensitive training datasets from infrastructure-level exposure.
Not ideal for: General-purpose, low-risk web applications or static websites where the performance overhead of hardware-based encryption outweighs the security benefits and where data sensitivity is minimal.
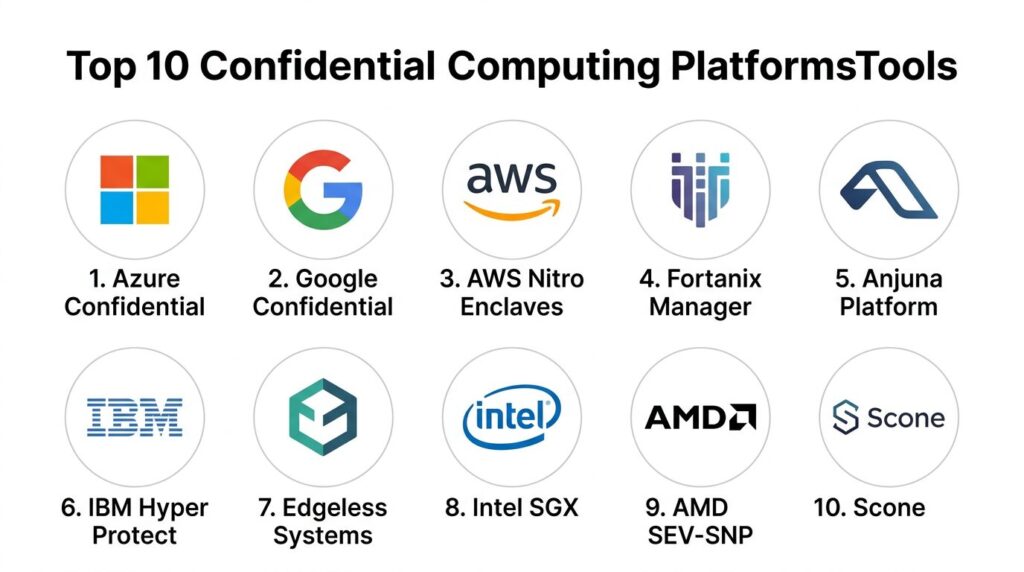
Key Trends in Confidential Computing Platforms
The industry is currently seeing a massive shift toward “Confidential AI,” where platforms are being optimized specifically to protect GPU-accelerated workloads. With the rise of generative AI, protecting model weights and user prompts has become a primary use case, leading to the development of rack-scale confidential systems that encompass CPUs, GPUs, and high-speed interconnects. Another significant trend is the rise of “Confidential Kubernetes,” which allows entire containerized clusters to run within hardware-enforced boundaries, making it easier for DevOps teams to deploy secure workloads without refactoring their entire microservices architecture.
Sustainability and sovereign cloud initiatives are also influencing the market, with providers now offering localized confidential zones that comply with specific regional data residency laws. We are also seeing the emergence of decentralized confidential compute networks that use blockchain for attestation and resource discovery, providing a trustless way to access secure hardware globally. Furthermore, the standardization led by the Confidential Computing Consortium is resulting in more portable workloads, allowing enterprises to move their “enclave-ready” applications between different cloud providers with less vendor lock-in than ever before.
How We Selected These Tools
Our selection process focused on platforms that provide a comprehensive “control plane” for managing the lifecycle of confidential workloads. We prioritized providers that support the leading hardware standards—primarily Intel Software Guard Extensions (SGX), Intel Trust Domain Extensions (TDX), and AMD Secure Encrypted Virtualization (SEV-SNP). We looked for solutions that offer “lift-and-shift” capabilities, allowing existing applications to run in TEEs without requiring developers to rewrite their code in specialized languages or use complex low-level SDKs.
Technical robustness was measured by the quality of the platform’s attestation services—the mechanism that proves the hardware and software are indeed in a secure state. We also evaluated the integration of these tools within broader DevOps and MLOps ecosystems, ensuring that security doesn’t become a bottleneck for deployment velocity. Finally, we considered the certifications and compliance postures of each platform, selecting those that have been vetted against international standards like SOC 2, HIPAA, and GDPR, making them ready for immediate production use in high-compliance sectors.
1. Microsoft Azure Confidential Computing
Microsoft Azure is a pioneer in the confidential space, offering a wide array of TEE-enabled hardware options integrated directly into its cloud ecosystem. It provides a mature environment for running both confidential virtual machines and confidential containers, making it the most versatile choice for large-scale enterprise migrations.
Key Features
The platform supports Intel SGX for application-level isolation and AMD SEV-SNP for full virtual machine encryption. It features the “Azure Confidential Ledger,” a tamper-proof data store backed by a hardware-based blockchain. Native integration with Azure Key Vault allows for secure key management within enclaves. The platform also offers “Confidential GKE” patterns and specific AI-ready instances that use NVIDIA’s confidential computing capabilities. It provides a comprehensive attestation service that verifies the integrity of the environment before any sensitive data is released for processing.
Pros
Offers the most diverse range of confidential hardware and service types in the public cloud. Integration with the broader Microsoft security and identity stack is seamless for existing enterprise customers.
Cons
The complexity of choosing between different hardware types (SGX vs. SEV-SNP) can be overwhelming for new users. High-end confidential instances carry a price premium over standard VMs.
Platforms and Deployment
Cloud-based via Azure Portal, CLI, and APIs; supports hybrid deployments via Azure Arc.
Security and Compliance
FIPS 140-2 Level 3, GDPR, HIPAA, and SOC 2 compliant; uses hardware-rooted attestation.
Integrations and Ecosystem
Deeply integrated with Azure Kubernetes Service (AKS), Azure Key Vault, and Azure Machine Learning.
Support and Community
Extensive documentation, dedicated security support teams, and active participation in the Confidential Computing Consortium.
2. Google Cloud Confidential Computing
Google Cloud takes a “simple-by-design” approach, focusing on making confidential computing accessible with minimal configuration. Their flagship offering focuses on “Confidential VMs,” which allow users to encrypt data in use with the click of a button.
Key Features
The platform is built primarily on AMD SEV-SNP technology, providing transparent memory encryption for entire virtual machines. It includes “Confidential GKE nodes,” allowing Kubernetes users to protect their containerized workloads with hardware-level isolation. Google Cloud uses a specialized “Shielded VM” foundation to ensure the integrity of the boot process. It offers an automated attestation service that integrates with the cloud’s Identity and Access Management (IAM) system. The platform also supports “Confidential Space,” a secure image execution environment designed specifically for multi-party data collaboration and privacy-preserving analytics.
Pros
Requires zero code changes to enable, making it the easiest “lift-and-shift” option for existing workloads. Excellent for multi-party data clean rooms where data privacy is paramount.
Cons
Has historically been more focused on VM-level isolation rather than the granular application-level enclaves offered by competitors. Hardware choices are primarily centered on AMD.
Platforms and Deployment
Native cloud service available across global Google Cloud regions.
Security and Compliance
Compliant with major global standards including SOC, ISO, and HIPAA; supports hardware-based memory encryption keys.
Integrations and Ecosystem
Strong ties with Google Kubernetes Engine (GKE), BigQuery for secure analytics, and Google Cloud IAM.
Support and Community
Reliable enterprise support and a strong focus on open-source contributions to the confidential computing ecosystem.
3. AWS Nitro Enclaves
Amazon Web Services provides a unique architectural approach through Nitro Enclaves, which are isolated compute environments carved out of a parent EC2 instance. This model is designed specifically for processing highly sensitive data like private keys and personally identifiable information (PII).
Key Features
Nitro Enclaves have no persistent storage, no interactive access, and no external networking; they communicate only with the parent EC2 instance via a secure local channel. The environment uses the AWS Nitro System, a custom hardware and software stack that minimizes the attack surface. It provides a dedicated “Nitro Enclaves SDK” for developing applications that run inside the enclave. Integration with AWS Key Management Service (KMS) allows enclaves to decrypt sensitive data only after successful attestation. It also supports “ACM for Nitro Enclaves” to protect SSL/TLS certificates during processing.
Pros
Provides an exceptionally small attack surface by stripping away all non-essential components of a typical OS. Deeply integrated with the AWS ecosystem for key and identity management.
Cons
Requires some application refactoring and use of the specific SDK to communicate with the enclave. Limited to the AWS environment, making it less portable for multi-cloud strategies.
Platforms and Deployment
Available on most Intel and AMD-based Amazon EC2 instance types.
Security and Compliance
Hardware-level isolation with cryptographically signed attestation documents; compliant with PCI DSS and HIPAA.
Integrations and Ecosystem
Native integration with AWS KMS, IAM, and CloudWatch for monitoring and security logs.
Support and Community
Robust AWS technical support and extensive developer guides for enclave-based programming.
4. Fortanix Confidential Computing Manager
Fortanix is a software-centric leader that provides a unified management layer for confidential computing across multi-cloud and on-premises environments. It is designed to orchestrate enclaves and manage keys without requiring deep hardware expertise from the user.
Key Features
The platform features a centralized management console that can handle enclaves across Azure, AWS, and GCP. It provides a “lift-and-shift” capability that allows standard applications (like databases or web servers) to run inside TEEs without modification. It includes an integrated Secret Management system that only releases keys to verified, attested enclaves. The platform supports the latest “Confidential AI” workflows, specifically protecting model inference on NVIDIA GPUs. It also features a “DevSecOps” pipeline integration that signs and verifies confidential images during the build process.
Pros
The best choice for multi-cloud strategies, providing a single pane of glass for different TEE technologies. significantly simplifies the technical hurdles of implementing Intel SGX.
Cons
Adding a third-party management layer can introduce additional subscription costs. Users are dependent on Fortanix for updates to supported hardware and cloud features.
Platforms and Deployment
Available as a SaaS offering or as an on-premises software deployment.
Security and Compliance
Designed for FIPS 140-2 Level 3 environments; supports GDPR, HIPAA, and international data sovereignty laws.
Integrations and Ecosystem
Supports all major public clouds and integrates with Kubernetes, Docker, and various CI/CD tools.
Support and Community
Industry-leading expertise in confidential computing and a very active participant in security standards bodies.
5. Anjuna Confidential Computing Platform
Anjuna focuses on making the transition to confidential computing completely transparent. Their platform acts as an abstraction layer that allows enterprises to run complex, unmodified applications inside secure enclaves in minutes.
Key Features
Anjuna provides a “Confidential Runtime” that automatically handles the complexities of memory management and attestation for the application. It supports a wide range of workloads, including high-performance databases, Big Data clusters, and machine learning models. The platform enables “lift-and-shift” for any Linux-based application into TEEs like Intel SGX or AWS Nitro. It includes a comprehensive attestation server that ensures only authorized code runs on authorized hardware. The system also provides detailed audit logs of enclave activities for compliance reporting.
Pros
Extreme ease of use for legacy and complex enterprise applications. Cloud-agnostic approach helps prevent vendor lock-in for confidential workloads.
Cons
May introduce a slight performance overhead due to the abstraction layer compared to native SDK-based development. Software-based management carries its own licensing fees.
Platforms and Deployment
Hybrid/Cloud-ready; works across AWS, Azure, and private data centers.
Security and Compliance
SOC 2 compliant; enables organizations to meet strict data privacy regulations like HIPAA and GDPR.
Integrations and Ecosystem
Strong support for Kubernetes, HashiCorp Vault, and various enterprise database systems.
Support and Community
Dedicated customer success teams and professional services for enterprise security architecture.
6. IBM Cloud Hyper Protect Services
IBM leverages its deep history in mainframe security to offer some of the most robust confidential computing services on the market. Their platform is built on IBM Z and LinuxONE hardware, providing a unique high-assurance environment for regulated sectors.
Key Features
The platform offers “Hyper Protect Virtual Servers” that provide absolute isolation of workloads, where even IBM administrators cannot access user data. It features a “Hyper Protect DBaaS” for running databases (like PostgreSQL or MongoDB) in a completely confidential environment. The hardware provides FIPS 140-2 Level 4 security, which is the highest industry standard for cryptographic modules. It supports “Secure Execution” for Linux, allowing thousands of enclaves to run on a single system. The service also includes a “Unified Key Orchestrator” for managing encryption keys across multiple clouds from a single high-security root.
Pros
Offers the highest levels of hardware security and tamper-resistance available in the cloud. Perfect for high-volume financial transactions and mission-critical government data.
Cons
The platform is built on specialized hardware (IBM Z), which may have a different operational model than standard x86 cloud services. The product catalog is more focused on specific high-security niches.
Platforms and Deployment
Available natively on IBM Cloud; supports hybrid cloud via Red Hat OpenShift.
Security and Compliance
FIPS 140-2 Level 4, HIPAA, GDPR, and ISO compliant; unique “Zero-Trust” administrative model.
Integrations and Ecosystem
Integrated with Red Hat OpenShift and IBM Cloud’s broader security and data platforms.
Support and Community
Expert-led professional services and dedicated global enterprise support for highly regulated industries.
7. Edgeless Systems (Constellation)
Edgeless Systems is a security-focused firm that created Constellation, the first “Confidential Kubernetes” distribution. Their goal is to make entire cloud-native infrastructures confidential by default.
Key Features
Constellation encrypts every layer of a Kubernetes cluster, including the control plane, worker nodes, and the network between them. It uses “Confidential VMs” as the building blocks for the cluster, ensuring that all data is protected in use. The platform provides a “verifiable build” process, allowing users to cryptographically prove that the software running in the cloud matches the source code. It handles the complex process of “Remote Attestation” for the entire cluster automatically. Constellation also integrates with Cilium and WireGuard to provide encrypted and isolated networking for all pods.
Pros
The most comprehensive solution for teams that want a completely confidential Kubernetes environment. Open-source core provides transparency and allows for independent security audits.
Cons
Currently supports a specific set of cloud providers (Azure, GCP) where the underlying hardware is available. Managing an entire confidential cluster requires strong Kubernetes expertise.
Platforms and Deployment
Kubernetes-native; deploys on public clouds or private hardware supporting TEEs.
Security and Compliance
Focuses on “Security by Design”; helps meet GDPR and German/EU-specific data sovereignty requirements.
Integrations and Ecosystem
Fully CNCF-certified; integrates with standard DevOps tools like Helm, Terraform, and Prometheus.
Support and Community
Strong presence in the open-source community and specialized support for confidential cloud-native architecture.
8. Intel Software Guard Extensions (SGX)
While Intel SGX is a hardware technology, its software ecosystem and “Intel Trust Authority” platform act as a foundational service for the entire industry. It provides the most granular level of protection by isolating specific portions of code in memory.
Key Features
SGX allows developers to define “enclaves” at the application layer, protecting sensitive routines even if the rest of the application or the OS is compromised. The “Intel Trust Authority” provides a unified attestation service that can verify enclaves across different cloud providers. It supports a massive library of developer tools and SDKs for C, C++, and Rust. The latest versions of Xeon processors have expanded the enclave memory limits to support large datasets and AI models. It also includes “Platform Firmware Resilience” to protect against low-level hardware attacks.
Pros
Provides the most granular “least privilege” security model available. It is the most widely studied and academically vetted confidential computing technology.
Cons
Implementing SGX natively requires significant developer effort and specialized programming knowledge. It has a higher performance overhead for certain memory-intensive tasks.
Platforms and Deployment
Hardware-based; available on Intel-powered servers across all major cloud providers and on-premises.
Security and Compliance
Foundational hardware security used to meet the most stringent international compliance requirements.
Integrations and Ecosystem
Massive ecosystem of third-party wrappers (like Gramine and Graphene) and enterprise security platforms.
Support and Community
Unmatched documentation, global developer forums, and a decade of established security research.
9. AMD Secure Encrypted Virtualization (SEV)
AMD SEV-SNP is the hardware foundation that has made “Confidential VMs” a reality. It focuses on isolating entire virtual machines from the hypervisor, providing a high level of security with virtually no changes to the application.
Key Features
The technology uses a unique encryption key for each virtual machine, which is managed by a dedicated security processor on the CPU. “SEV-SNP” (Secure Nested Paging) adds strong memory integrity protection to prevent attacks from malicious hypervisors. It allows for “transparent” encryption, meaning any OS or application can run without modification. It supports high-performance workloads by offloading encryption tasks to dedicated hardware engines. Many platforms use SEV as the root of trust for their “Confidential VM” offerings.
Pros
Excellent performance-to-security ratio with minimal overhead. It is the easiest hardware technology to adopt for “lift-and-shift” cloud migrations.
Cons
Less granular than Intel SGX; it protects the entire VM, meaning you still have to trust the guest OS inside that VM. Attestation workflows are often handled by the cloud provider.
Platforms and Deployment
Hardware-level; available on AMD EPYC processors in Azure, Google Cloud, and Oracle Cloud.
Security and Compliance
Provides the hardware-rooted isolation necessary for GDPR, SOC 2, and HIPAA compliance in the cloud.
Integrations and Ecosystem
Broadly supported by major Linux distributions and all leading virtualization platforms.
Support and Community
Strong industry backing and deep integration with the Linux kernel and open-source virtualization projects.
10. Scone (Scontain)
Scone is a specialized platform designed for securing containerized applications using Intel SGX. It is particularly popular in the European market for its focus on industrial IoT and secure data processing.
Key Features
The platform features a “Configuration and Attestation Service” (CAS) that manages the secrets and policies for enclaves. It provides a specialized runtime that can execute unmodified Docker containers inside SGX enclaves. Scone supports “Confidential PyTorch” and “Confidential TensorFlow” for secure AI model training and inference. It includes a visual dashboard for monitoring the health and attestation status of distributed enclaves. The platform also offers tools for “Confidential Data Exchange,” allowing multiple parties to securely share data for collaborative processing.
Pros
Excellent support for modern container-native workflows and AI frameworks. Strong focus on “Zero-Trust” configuration management through its CAS system.
Cons
The licensing model can be complex for small-scale deployments. It is primarily focused on Intel SGX, which limits hardware flexibility.
Platforms and Deployment
Container-centric; works on Kubernetes and any platform supporting Docker and SGX.
Security and Compliance
Designed to meet stringent European data privacy laws and industrial security standards.
Integrations and Ecosystem
Strong integration with the Kubernetes ecosystem and common data science tools.
Support and Community
Provides high-quality technical support and is an active contributor to confidential computing research in Europe.
Comparison Table
| Tool Name | Best For | Platform(s) Supported | Deployment | Standout Feature | Public Rating |
| 1. Azure Confidential | Enterprise Ecosystems | Azure, Hybrid | Cloud/Hybrid | Wide Hardware Choice | 4.8/5 |
| 2. Google Confidential | Cloud-Native Teams | GCP | Cloud | One-Click Activation | 4.6/5 |
| 3. AWS Nitro Enclaves | Sensitive Key Processing | AWS (EC2) | Cloud | No External Network | 4.5/5 |
| 4. Fortanix Manager | Multi-Cloud Governance | AWS, Azure, GCP, On-Prem | SaaS/On-Prem | Unified Enclave Control | 4.7/5 |
| 5. Anjuna Platform | Legacy App Migration | AWS, Azure, On-Prem | Hybrid | Zero-Code Refactoring | 4.6/5 |
| 6. IBM Hyper Protect | Financial/High-Reg | IBM Cloud, OpenShift | Cloud/Hybrid | FIPS 140-2 Level 4 | 4.9/5 |
| 7. Edgeless (Constellation) | Confidential Kubernetes | Azure, GCP, Hybrid | Hybrid | Full-Cluster Encryption | 4.4/5 |
| 8. Intel SGX | Granular App Isolation | Global Hardware | On-Prem/Cloud | Application-Level Enclave | 4.7/5 |
| 9. AMD SEV-SNP | High-Performance VMs | Global Hardware | On-Prem/Cloud | Transparent VM Encryption | 4.6/5 |
| 10. Scone | Secure AI/IoT | Kubernetes, Docker | Hybrid | Confidential AI Support | 4.3/5 |
Evaluation & Scoring of Confidential Computing Platforms
The scoring below is a comparative model intended to help shortlisting. Each criterion is scored from 1–10, then a weighted total from 0–10 is calculated using the weights listed. These are analyst estimates based on typical fit and common workflow requirements, not public ratings.
Weights:
- Core features – 25%
- Ease of use – 15%
- Integrations & ecosystem – 15%
- Security & compliance – 10%
- Performance & reliability – 10%
- Support & community – 10%
- Price / value – 15%
| Tool Name | Core (25%) | Ease (15%) | Integrations (15%) | Security (10%) | Performance (10%) | Support (10%) | Value (15%) | Weighted Total |
| 1. Azure Confidential | 10 | 8 | 10 | 9 | 8 | 10 | 8 | 9.05 |
| 2. Google Confidential | 8 | 10 | 9 | 8 | 9 | 9 | 9 | 8.75 |
| 3. AWS Nitro Enclaves | 9 | 6 | 8 | 10 | 9 | 9 | 8 | 8.35 |
| 4. Fortanix Manager | 9 | 8 | 9 | 9 | 8 | 9 | 7 | 8.50 |
| 5. Anjuna Platform | 9 | 9 | 8 | 9 | 8 | 8 | 8 | 8.55 |
| 6. IBM Hyper Protect | 10 | 5 | 7 | 10 | 9 | 10 | 7 | 8.50 |
| 7. Edgeless Systems | 9 | 7 | 8 | 9 | 8 | 8 | 9 | 8.30 |
| 8. Intel SGX | 10 | 4 | 9 | 10 | 7 | 10 | 8 | 8.35 |
| 9. AMD SEV-SNP | 8 | 9 | 9 | 8 | 10 | 8 | 9 | 8.65 |
| 10. Scone | 8 | 7 | 8 | 9 | 8 | 8 | 8 | 8.05 |
How to interpret the scores:
- Use the weighted total to shortlist candidates, then validate with a pilot.
- A lower score can mean specialization, not weakness.
- Security and compliance scores reflect controllability and governance fit, because certifications are often not publicly stated.
- Actual outcomes vary with assembly size, team skills, templates, and process maturity.
Which Confidential Computing Platform Is Right for You?
Solo / Freelancer
For individual developers or privacy enthusiasts, Google Cloud Confidential VMs provide the lowest barrier to entry. With “one-click” activation and no code changes required, it allows a single user to secure their data without the need for an enterprise security team or specialized programming skills.
SMB
Small to medium businesses that are already cloud-native should look at the offerings from their primary provider, such as Azure or AWS. However, if an SMB is using a specialized Kubernetes stack, Edgeless Systems offers a path to full-cluster confidentiality that is easier to manage than custom enclave development.
Mid-Market
Organizations with a growing footprint across multiple clouds should prioritize Fortanix or Anjuna. These platforms provide the orchestration necessary to maintain consistent security policies across different hardware and cloud vendors, ensuring that the security team isn’t overwhelmed by fragmented tools.
Enterprise
For massive enterprises and global banks, IBM Cloud Hyper Protect and Azure Confidential Computing are the gold standards. These platforms offer the compliance certifications and high-assurance hardware (like IBM Z or Intel SGX on Xeon) that are mandatory for the most sensitive and regulated workloads.
Budget vs Premium
AMD SEV-based Confidential VMs (available on Google and Azure) generally offer the best “budget” performance, as they require no refactoring and have low overhead. Premium solutions like IBM Hyper Protect or custom Intel SGX implementations carry higher costs but offer superior, granular isolation.
Feature Depth vs Ease of Use
Intel SGX offers the most feature depth and granular control but is notoriously difficult to implement without a wrapper. For those who value ease of use, Google Cloud and Anjuna provide “transparent” encryption that prioritizes speed of deployment over code-level isolation.
Integrations & Scalability
Azure leads in terms of ecosystem integration, specifically for those using Microsoft’s AI and data science tools. For developers focused on container scalability, Scone and Edgeless Systems provide the most robust Kubernetes-native confidential computing workflows.
Security & Compliance Needs
If your primary goal is meeting FIPS 140-2 Level 4 or handling government-level classified data, IBM Hyper Protect is the clear choice. For general HIPAA and GDPR compliance in the public cloud, all platforms in the top five provide the necessary hardware-rooted attestation to satisfy auditors.
Frequently Asked Questions (FAQs)
1. What exactly is “Data in Use” protection?
It refers to protecting data while it is actively being processed in the CPU and RAM. Traditional encryption only protects data when it’s stored on a disk or moving through a cable. Confidential computing uses a TEE to ensure that even a person with physical access to the server cannot read the data in memory.
2. Does confidential computing slow down my application?
Yes, there is usually a “performance tax” because the CPU has to encrypt and decrypt data as it moves in and out of the enclave. For VM-level encryption (like AMD SEV), this is often less than 2–5%. For granular application enclaves (like Intel SGX), it can be higher depending on the workload.
3. Do I need to rewrite my code to use these platforms?
It depends on the platform. Tools like Google Confidential VMs or Anjuna require zero code changes (“lift-and-shift”). However, using the full security potential of Intel SGX or AWS Nitro Enclaves directly often requires using specific SDKs to define what code should be protected.
4. How is this different from a standard VPN or disk encryption?
A VPN protects data while it travels (transit), and disk encryption protects data when it’s off (rest). Neither prevents a malicious administrator or a hacker with “root” access from seeing your data while your program is actually running. Confidential computing stops those threats.
5. What is “Remote Attestation”?
Attestation is a cryptographic process where the hardware provides a signed “report” to the user, proving that the environment is a genuine secure enclave and that the specific code the user intended to run has not been tampered with before it starts.
6. Can I run AI models in a confidential environment?
Yes, “Confidential AI” is one of the fastest-growing use cases. Platforms like Azure, Scone, and Fortanix now support confidential GPUs (like NVIDIA H100/B200), allowing you to protect both your model weights and the sensitive data used for training or inference.
7. Is confidential computing only for the public cloud?
No, you can implement it on-premises if you have the right hardware (recent Intel Xeon or AMD EPYC CPUs). Management platforms like Fortanix allow you to manage these local enclaves just as you would cloud-based ones.
8. Who is the Confidential Computing Consortium?
It is a community under the Linux Foundation that includes major players like Google, Microsoft, Intel, and AMD. They work together to create open-source standards and ensure that confidential computing becomes a standard feature of modern architecture.
9. Can a cloud provider still see my data if I use these tools?
If implemented correctly, no. The encryption keys are managed by a security processor inside the CPU that the cloud provider’s software cannot access. Through attestation, you can verify that the provider is “blind” to your processing.
10. What are the main hardware technologies used?
The industry currently relies on three main ones: Intel SGX (for application enclaves), Intel TDX (for secure VMs), and AMD SEV-SNP (for secure VMs). ARM also has its “TrustZone” and “Confidential Compute Architecture” (CCA) for mobile and edge devices.
Conclusion
The transition to confidential computing is a fundamental evolution in how we define digital trust. As we move further into a decade dominated by artificial intelligence and distributed data collaboration, the ability to process information without exposing it to the underlying infrastructure is becoming a non-negotiable requirement. The platforms highlighted today provide the necessary bridge between sophisticated hardware security and practical enterprise deployment. Success in this field requires more than just selecting a tool; it requires a cultural shift toward a “zero-trust” architecture where security is verified by math and silicon rather than human promises. By adopting these platforms, organizations can finally unlock the full potential of the cloud and AI while maintaining absolute sovereignty over their most valuable digital assets.