INTRODUCTION
AI content authenticity and provenance tools represent the primary defense mechanism against the proliferation of deepfakes and synthetic misinformation. These technologies function by establishing a “chain of trust” for digital media, either through cryptographic labeling at the point of creation or forensic analysis after distribution. As generative AI models reach a level of realism that bypasses human detection, the ability to verify the origin and edit history of an image, video, or audio file has become a critical requirement for global security. These tools are no longer optional for media organizations, government agencies, or financial institutions where the integrity of digital evidence is paramount.
When evaluating these platforms, enterprise leaders prioritize interoperability and the resilience of the verification signals. Real-world applications are expanding rapidly, including the protection of electoral integrity, the verification of insurance claims, and the safeguarding of brand reputation against AI-driven impersonation. Buyers must distinguish between “detection” tools, which guess if content is AI-generated, and “provenance” tools, which provide immutable proof of a file’s journey. Modern expectations demand that these systems integrate directly into existing production workflows, ensuring that authenticity is “baked in” from the moment a camera shutter clicks or a rendering engine finishes its task.
Best for: News agencies, legal firms, trust and safety teams, social media platforms, and creators who need to prove their authorship in an AI-saturated market.
Not ideal for: Casual social media users, basic personal photo editing, or organizations that do not handle sensitive or high-stakes digital assets.
KEY TRENDS IN AI CONTENT AUTHENTICITY & PROVENANCE TOOLS
The industry is rapidly consolidating around the C2PA (Coalition for Content Provenance and Authenticity) standard, which provides a universal framework for “Content Credentials.” This shift moves the industry away from proprietary silos and toward a unified ecosystem where different tools can read and verify each other’s data. There is also a significant trend toward hardware-level integration, with camera manufacturers and smartphone chipmakers embedding cryptographic signing directly into the hardware sensors. Furthermore, global regulations are mandating the labeling of synthetic media, forcing platforms to adopt automated verification at scale. Real-time forensic watermarking is also becoming more robust, allowing metadata to survive aggressive compression and social media re-sharing.
METHODOLOGY
The selection of these top ten tools followed a rigorous evaluation of their technical architecture and industry adoption. We prioritized platforms that support open standards like C2PA and those that offer a multi-layered approach—combining metadata, digital watermarking, and forensic detection. Reliability was assessed through participation in global trust initiatives and the ability of the tools to withstand “adversarial attacks” designed to strip away provenance data. We also examined the ease of integration through APIs and SDKs, which is essential for enterprise-scale deployment. Finally, the scoring considered the balance between privacy-preserving features and the need for transparent attribution, ensuring that these tools protect both the consumer and the creator.
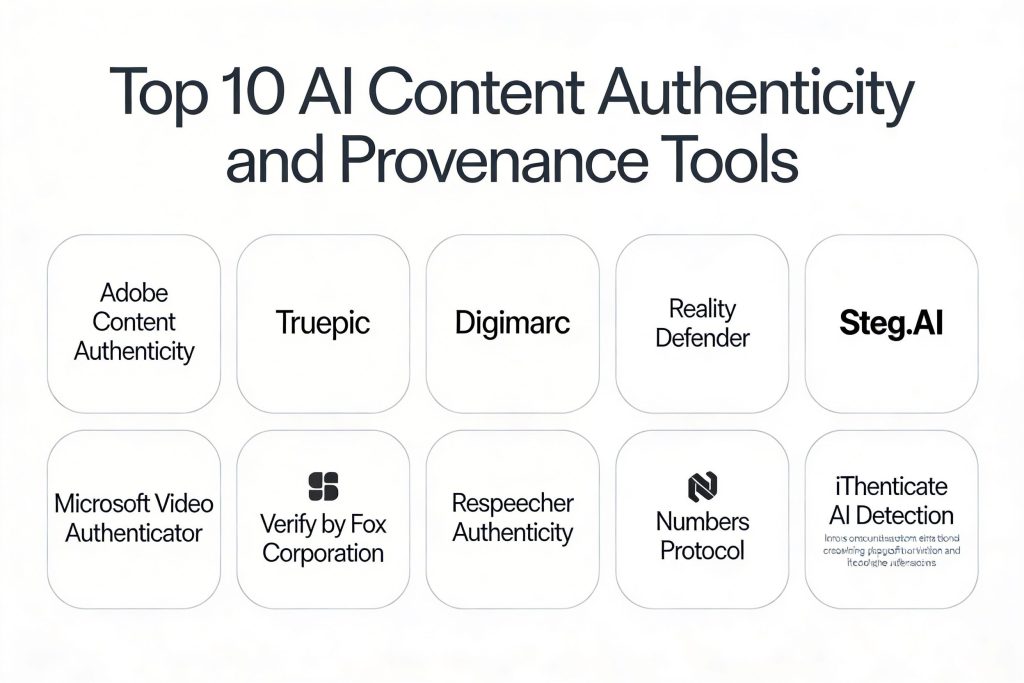
TOP 10 AI CONTENT AUTHENTICITY & PROVENANCE TOOLS
1. Adobe Content Authenticity
Adobe has taken a leadership role in the authenticity space by developing the Content Credentials system. This tool allows creators to attach tamper-evident metadata to their files, detailing who created the work and what tools were used. It is integrated directly into the Creative Cloud ecosystem, making it a natural choice for professional designers and photographers who already use Adobe products.
The system uses a combination of cryptographic signing and cloud-based “manifests” to ensure that provenance data persists even if the file is exported or screenshotted. It also includes an “Inspect” tool that allows anyone to view the history of a file by simply uploading it to a web portal.
Pros:
It is backed by the largest creative software company in the world and uses the industry-standard C2PA framework. The user interface is exceptionally clean, making it easy for non-technical users to understand the “ingredients” of a digital file.
Cons:
The system is most effective within the Adobe ecosystem, and its protection can still be bypassed by malicious actors who manually strip metadata from files not yet protected by its invisible watermarking feature.
Platforms / Deployment:
Windows / macOS / Web
Cloud / Hybrid
Security & Compliance:
C2PA Compliant, SHA-256 Hashing
SOC 2, ISO 27001
Integrations & Ecosystem:
Deeply integrated with Photoshop, Lightroom, and Firefly. It also connects with social media platforms like Behance and LinkedIn to display authenticity badges.
Support & Community:
Provides extensive documentation and is supported by the global Content Authenticity Initiative community.
2. Truepic
Truepic is a pioneer in “provenance-first” technology, focusing on capturing authentic media at the source. Its technology is designed for industries like insurance and banking, where the “truth” of a photo—such as the damage to a car or the identity of a customer—is financially critical.
The platform offers a mobile SDK that allows developers to build “secure cameras” into their own apps. When a photo is taken, Truepic verifies the device’s sensors, location, and time, then signs the file cryptographically to ensure it has not been altered since the moment of capture.
Pros:
It offers the highest level of assurance by verifying the environment at the point of capture. Its “Truepic Lens” technology is becoming a standard for secure remote inspections.
Cons:
The enterprise-level pricing can be prohibitive for smaller organizations. It requires a specific integration into mobile apps rather than being a general-purpose tool for existing files.
Platforms / Deployment:
iOS / Android / Web
SaaS / SDK
Security & Compliance:
C2PA Conformance, FIPS 140-2
SOC 2 Type II
Integrations & Ecosystem:
Integrates with major claims management systems and enterprise CRM tools. It also partners with hardware manufacturers to embed its technology at the chip level.
Support & Community:
Offers professional technical support and dedicated account management for enterprise clients.
3. Digimarc
Digimarc specializes in digital watermarking that is invisible to the human eye but easily detectable by software. Unlike standard metadata, Digimarc’s watermarks are woven into the actual pixels of an image or the frames of a video, making them extremely difficult to remove through cropping or compression.
Their Content Authenticity solution combines this robust watermarking with C2PA metadata. This creates a dual-layer of protection: the metadata provides the “who and how,” while the watermark provides a “silent signal” that links back to the original record if the metadata is ever stripped away.
Pros:
The watermarks are incredibly resilient and can survive almost any form of content manipulation. The platform is highly scalable, capable of protecting billions of digital assets across a global network.
Cons:
The initial setup and licensing model can be complex for organizations that do not have a large-scale asset management strategy.
Platforms / Deployment:
Cloud / API
Enterprise SaaS
Security & Compliance:
C2PA 2.1, GDPR Compliant
ISO 27001
Integrations & Ecosystem:
Offers powerful APIs for integration with Digital Asset Management (DAM) systems and content distribution networks.
Support & Community:
Provides 24/7 technical support for enterprise partners and a wealth of white papers on digital signal processing.
4. Reality Defender
Reality Defender is a premier deepfake detection platform that serves enterprises and governments. Rather than focusing solely on provenance, it uses a multi-model AI approach to scan files for artifacts that indicate synthetic manipulation in video, audio, and images.
The platform is often used at “choke points,” such as when a user uploads an ID photo or when a high-stakes video is received by a newsroom. It provides a probability score and a detailed heat map showing which parts of the media are likely to have been manipulated by AI.
Pros:
It is one of the most effective tools for detecting deepfakes that were created without any provenance data. Its models are constantly updated to detect the latest generation of generative AI models.
Cons:
As a detection tool, it is part of a constant “arms race” against new AI generators. It can occasionally produce false positives if not configured correctly for the specific media type.
Platforms / Deployment:
Web / API
Cloud-Native
Security & Compliance:
MFA, RBAC, Data Encryption at Rest
SOC 2
Integrations & Ecosystem:
Integrates via API into content moderation workflows and cybersecurity stacks. It is also available as a web portal for manual file inspection.
Support & Community:
Offers dedicated research insights and technical support for its high-security clients.
5. Steg.AI
Steg.AI provides forensic-grade digital watermarking with a focus on leak detection and brand protection. Their technology allows organizations to embed unique, imperceptible identifiers into their media, allowing them to trace the exact source of a file if it is leaked or misused.
The platform is designed for high-performance environments, capable of watermarking assets in real-time as they are being distributed. This is particularly useful for media companies that need to protect pre-release content or sensitive internal communications.
Pros:
The watermarks are “forensic,” meaning they can be used as evidence to identify the specific account or device that originated a leak. It works across images, video, and audio.
Cons:
It is primarily focused on the “tracking” aspect of provenance rather than the “public attribution” aspect, making it a more internal-facing security tool.
Platforms / Deployment:
Web / API / SDK
Cloud / On-Premise
Security & Compliance:
AES-256, Secure Key Management
Not publicly stated
Integrations & Ecosystem:
Connects with major video production pipelines and secure document management systems.
Support & Community:
Focuses on direct enterprise support and custom implementation services.
6. Microsoft Video Authenticator
Microsoft’s contribution to the space is a tool specifically designed to combat video deepfakes. It analyzes video files to identify subtle “blending” artifacts and pixel-level inconsistencies that are invisible to the human eye but common in AI-generated content.
The tool provides a real-time “confidence score” as the video plays, alerting the user to segments that may have been manipulated. It was developed in collaboration with major media organizations to provide a reliable check for journalists during breaking news events.
Pros:
It is backed by the vast research capabilities of Microsoft and is provided to qualified media organizations as part of their democratic integrity initiatives.
Cons:
Access is generally restricted to specific sectors like journalism and government to prevent malicious actors from using the tool to “test” and improve their deepfakes.
Platforms / Deployment:
Cloud-based
Restricted Access
Security & Compliance:
Enterprise-grade Microsoft Cloud Security
GDPR, SOC 1/2/3
Integrations & Ecosystem:
Works within the broader Microsoft Azure ecosystem and is often used alongside other media verification tools.
Support & Community:
Supported by Microsoft’s dedicated AI for Good and Defending Democracy teams.
7. Verify by Fox Corporation
Verify is an open-source protocol developed by Fox Corporation to allow media companies to register their content on a public ledger. By creating a “digital fingerprint” of every article and image, they allow platforms and users to verify that a piece of news actually originated from their newsroom.
The tool uses a blockchain-based approach to ensure that the record of origin is immutable and cannot be altered by a third party. This allows readers to use a browser extension or a web portal to confirm the authenticity of a news link.
Pros:
It is an industry-led effort to solve the problem of news impersonation and “pink slime” websites. Its open-source nature encourages broad adoption by other media outlets.
Cons:
The effectiveness of the system depends on widespread adoption by both creators and platforms. It is more focused on “source verification” than “edit history.”
Platforms / Deployment:
Web / Blockchain
Decentralized Protocol
Security & Compliance:
Blockchain Immutability, Hashing
Not publicly stated
Integrations & Ecosystem:
Designed to be integrated into CMS (Content Management Systems) and social media platform verification layers.
Support & Community:
Maintains an open-source repository and a community of participating media organizations.
8. Respeecher Authenticity
Respeecher, a leader in AI voice cloning, has developed its own set of tools to ensure the ethical use of synthetic audio. Their system involves embedding “audio watermarks” into the speech they generate, which can be identified by their verification tools.
This approach allows broadcasters and filmmakers to use high-quality AI voices while ensuring that the content is clearly labeled as synthetic in the metadata. It also helps prevent the misuse of their technology for creating non-consensual voice clones.
Pros:
It sets a high ethical standard for the AI voice industry. The watermarks are designed to be audible to machines but completely transparent to human listeners.
Cons:
The verification only works for audio generated by Respeecher’s own system, rather than acting as a universal detector for all AI speech.
Platforms / Deployment:
Cloud / API
Managed Service
Security & Compliance:
KYC (Know Your Customer) for voice cloning
Not publicly stated
Integrations & Ecosystem:
Integrates with professional audio workstations and film production pipelines.
Support & Community:
Provides detailed ethical guidelines and professional support for creative partners.
9. Numbers Protocol
Numbers Protocol is a decentralized provenance network that treats every digital asset as a “Capture.” It provides a comprehensive record of a file’s lifecycle, including where it was taken, who owns the rights, and every time it has been licensed or edited.
The platform is popular among independent journalists and creators who want to maintain control over their intellectual property in an era of AI scraping. It creates a “Web3” identity for every file, making it easier to monetize and verify.
Pros:
It provides a very high level of transparency and is excellent for tracking the commercial life of an asset. It empowers individual creators with professional-grade provenance tools.
Cons:
The reliance on blockchain technology can introduce complexity and transaction costs that may not be suitable for high-volume, low-value assets.
Platforms / Deployment:
iOS / Android / Web
Decentralized Network
Security & Compliance:
Decentralized Storage, IPFS
Not publicly stated
Integrations & Ecosystem:
Integrates with various NFT marketplaces and decentralized social media protocols.
Support & Community:
Has a highly active developer community and provides a range of open-source SDKs.
10. Ithenticate AI Detection
iThenticate, long the standard for plagiarism detection in academia, has expanded its capabilities to include the detection of AI-generated text. It is used by publishers and universities to ensure the authenticity of research papers and manuscripts.
The tool uses advanced linguistic analysis to identify the statistical patterns common in Large Language Models (LLMs). It provides a detailed report showing which sections of a document are likely to be human-written versus AI-generated.
Pros:
It is the most trusted tool in the academic and scientific publishing world. It has a massive database of existing literature to compare against for traditional plagiarism as well.
Cons:
It is focused exclusively on text, rather than visual or audio media. Detecting AI text is notoriously difficult, and the tool is best used as a “flag” for further human review rather than a definitive judgment.
Platforms / Deployment:
Web-based
SaaS
Security & Compliance:
FERPA, GDPR, SOC 2
Data Privacy focused
Integrations & Ecosystem:
Integrates directly into the submission systems of major academic journals and university learning management systems.
Support & Community:
Offers professional training and dedicated support for educational and research institutions.
COMPARISON TABLE
| Tool Name | Primary Function | Content Type | Standard | Deployment | Public Rating |
| 1. Adobe Content Authenticity | Provenance | Images/Video | C2PA | Cloud/Desktop | 4.7/5 |
| 2. Truepic | Point-of-Capture | Images/Video | C2PA | Mobile SDK | N/A |
| 3. Digimarc | Watermarking | All Media | C2PA | API/Cloud | 4.6/5 |
| 4. Reality Defender | Deepfake Detection | All Media | Proprietary | Web/API | 4.8/5 |
| 5. Steg.AI | Forensic Tracking | All Media | Proprietary | API/SaaS | N/A |
| 6. Microsoft Authenticator | Deepfake Detection | Video | Proprietary | Restricted | N/A |
| 7. Verify (Fox Corp) | Source Verification | News/Media | Open/Web3 | Protocol | N/A |
| 8. Respeecher | Audio Provenance | Audio | Proprietary | Managed | N/A |
| 9. Numbers Protocol | Lifecycle Tracking | All Media | C2PA/Web3 | Decentralized | 4.4/5 |
| 10. iThenticate | Text Authenticity | Text | N/A | Web SaaS | 4.5/5 |
EVALUATION & SCORING OF AI CONTENT AUTHENTICITY TOOLS
The scoring below is a comparative model intended to help shortlisting. Each criterion is scored from 1–10, then a weighted total from 0–10 is calculated using the weights listed. These are analyst estimates based on typical fit and common workflow requirements, not public ratings.
Weights:
- Core features – 25%
- Ease of use – 15%
- Integrations & ecosystem – 15%
- Security & compliance – 10%
- Performance & reliability – 10%
- Support & community – 10%
- Price / value – 15%
| Tool Name | Core (25%) | Ease (15%) | Integrations (15%) | Security (10%) | Performance (10%) | Support (10%) | Value (15%) | Weighted Total |
| 1. Adobe Authenticity | 10 | 9 | 10 | 9 | 8 | 9 | 8 | 9.15 |
| 2. Truepic | 10 | 6 | 8 | 10 | 9 | 8 | 7 | 8.30 |
| 3. Digimarc | 9 | 7 | 9 | 9 | 10 | 9 | 7 | 8.50 |
| 4. Reality Defender | 9 | 8 | 8 | 9 | 9 | 8 | 6 | 8.15 |
| 5. Steg.AI | 8 | 7 | 7 | 9 | 10 | 7 | 7 | 7.75 |
| 6. Microsoft Authenticator | 8 | 7 | 6 | 10 | 8 | 8 | 8 | 7.70 |
| 7. Verify (Fox Corp) | 7 | 6 | 8 | 9 | 8 | 6 | 10 | 7.65 |
| 8. Respeecher | 8 | 8 | 7 | 8 | 9 | 7 | 7 | 7.65 |
| 9. Numbers Protocol | 8 | 6 | 7 | 9 | 7 | 7 | 9 | 7.55 |
| 10. iThenticate | 7 | 9 | 9 | 9 | 8 | 9 | 7 | 8.15 |
How to interpret the scores:
- Use the weighted total to shortlist candidates, then validate with a pilot.
- A lower score can mean specialization, not weakness.
- Security and compliance scores reflect controllability and governance fit, because certifications are often not publicly stated.
- Actual outcomes vary with assembly size, team skills, templates, and process maturity.
WHICH AI CONTENT AUTHENTICITY TOOL IS RIGHT FOR YOU?
Solo / Freelancer
Adobe Content Authenticity is the best choice for individual creators. It is already included in many Creative Cloud plans and provides a professional way to prove your work is “human-made” without needing technical expertise.
SMB
Small businesses focusing on marketing should consider Digimarc or Numbers Protocol. These tools help protect brand assets from being misused in AI-generated scams while providing a clear link back to the original company.
Mid-Market
Organizations in the insurance or real-estate sectors should prioritize Truepic. Its ability to verify photos at the point of capture significantly reduces the risk of fraud in remote inspections and claims.
Enterprise
For large-scale media companies or high-security firms, Reality Defender and Steg.AI offer the most robust protection. These tools provide the forensic depth needed to analyze unverified content and track internal data leaks.
Budget vs Premium
The Adobe and Verify (Fox Corp) solutions offer the best value for general use, while specialized forensic tools like Truepic and Reality Defender carry premium pricing for high-stakes enterprise needs.
Feature Depth vs Ease of Use
Ithenticate and Adobe are designed for broad, easy use. Conversely, Steg.AI and Truepic require more technical integration but offer much deeper security and tracking capabilities.
Integrations & Scalability
Digimarc and Adobe lead in scalability, with well-documented APIs that allow them to be embedded into existing high-volume production pipelines.
Security & Compliance Needs
Microsoft and Truepic are the strongest choices for organizations with extreme security requirements, offering the most rigid compliance and hardware-level verification.
FREQUENTLY ASKED QUESTIONS (FAQS)
What is the difference between AI detection and provenance?
Detection tries to guess if a file was made by AI by looking for flaws. Provenance provides a historical record of where the file came from and how it was made, like a “digital birth certificate.”
Can someone just screenshot a photo to remove the credentials?
While a screenshot removes simple metadata, tools like Adobe and Digimarc use invisible watermarking and fingerprinting to recover the credentials even from a screenshot.
Is there a universal standard for these tools?
Yes, the C2PA standard is the leading universal framework. Most major tools are now aligning with this standard to ensure they can work together.
Do these tools protect my privacy?
Most provenance tools are designed to be “privacy-first,” allowing you to choose how much information you include in the credentials, such as your name or location.
Are these tools only for images?
No, modern solutions cover images, video, audio, and even text, though the methods used (watermarking vs. metadata vs. hashing) vary by the type of media.
Can AI detection tools ever be 100% accurate?
No. AI detection is an “arms race.” As AI models improve, they become harder to detect. Provenance is generally considered a more reliable long-term solution.
How does blockchain help with content authenticity?
Blockchain provides an immutable ledger that records the “fingerprint” of a file, making it impossible for a third party to change the record of who created it and when.
Do I need special hardware to use these tools?
While software tools work on existing files, some “point-of-capture” tools like Truepic or those built into Leica/Nikon cameras use hardware-level security for higher trust.
Can these tools detect if a human-made photo was edited by AI?
Yes, C2PA-compliant tools record a “recipe” of the file, showing exactly which parts were modified by AI tools like Generative Fill.
Are these tools required by law?
In some jurisdictions, regulations like the EU AI Act and the California AI Transparency Act are beginning to mandate the labeling of synthetic content, making these tools a legal necessity.
CONCLUSION
Implementing AI content authenticity and provenance tools is a fundamental step toward restoring digital trust. As synthetic media becomes indistinguishable from reality, the focus must shift from reactive detection to proactive verification. The tools listed above provide the necessary infrastructure to protect creators, inform consumers, and secure organizational assets against the risks of deepfakes and misinformation. While no single tool is a perfect solution, a multi-layered approach that combines open standards with robust watermarking offers the best defense. Organizations should begin by identifying their most vulnerable content points and selecting a tool that integrates seamlessly into their current workflow while adhering to global standards like C2PA.