Introduction
Third-Party Risk Management tools help organizations assess, monitor, and manage risks introduced by vendors, suppliers, partners, contractors, and service providers. These risks can include cybersecurity exposure, data privacy gaps, operational failures, regulatory non-compliance, financial instability, and reputational damage. Teams use these tools to standardize vendor due diligence, automate questionnaires, validate evidence, track remediation, and maintain continuous oversight across the vendor lifecycle.
Common use cases include onboarding critical SaaS vendors, reviewing outsourced IT and BPO partners, managing supply-chain security requirements, supporting audits, and tracking remediation for high-risk vendors. When evaluating a tool, focus on vendor inventory and tiering, questionnaire automation, evidence collection, continuous monitoring, workflow and approvals, reporting, integrations, risk scoring logic, contract and SLA controls, third-party cyber signals, and support for regulatory audits.
Best for: security teams, risk and compliance teams, procurement, legal, privacy offices, and IT governance teams managing many vendors across finance, healthcare, manufacturing, retail, and tech.
Not ideal for: very small businesses with only a few low-risk vendors and no formal audit needs; a lightweight spreadsheet-based process may be enough until complexity grows.
Key Trends in Third-Party Risk Management Tools
- Continuous monitoring replacing one-time annual vendor reviews
- More automation for questionnaires, evidence requests, and follow-ups
- Cyber risk scoring and external signals used to prioritize vendor attention
- Consolidation of third-party risk, compliance, and audit workflows into shared platforms
- Greater focus on fourth-party visibility and supply chain mapping
- Privacy and data handling assessment becoming a central requirement
- Built-in remediation workflows with deadlines, owners, and escalation
- Stronger reporting for board-level visibility and audit readiness
- Integrations with GRC, IAM, ticketing, and procurement systems becoming standard
- Higher expectations for configurable risk models rather than fixed scoring
How We Selected These Tools (Methodology)
- Prioritized tools with strong adoption in vendor risk and enterprise governance teams
- Selected platforms with end-to-end lifecycle support from onboarding to offboarding
- Considered capability depth in questionnaires, evidence, and remediation tracking
- Weighted continuous monitoring and cyber risk signal support where available
- Looked at workflow strength, approvals, and audit-ready reporting
- Included a mix of enterprise-grade and mid-market-friendly options
- Considered ecosystem and integration patterns with GRC and IT workflows
- Compared tools using a consistent scoring rubric based on practical outcomes
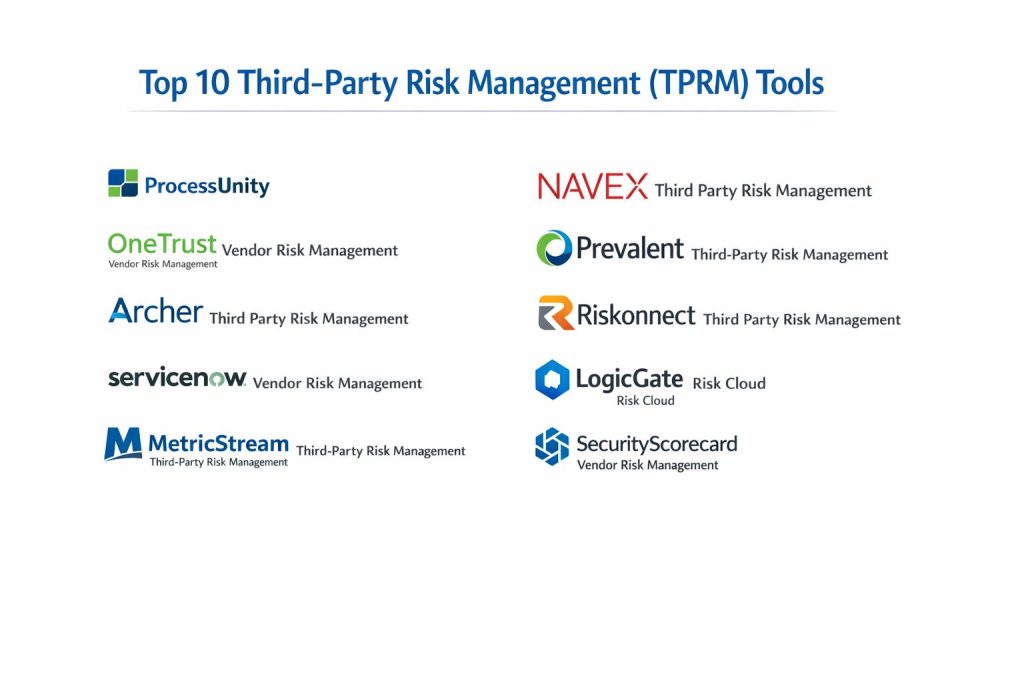
Top 10 Third-Party Risk Management Tools
1) ProcessUnity
A platform focused on third-party risk workflows, vendor onboarding, and standardized assessments. Often used by teams that want structured questionnaires, evidence management, and remediation tracking.
Key Features
- Vendor inventory with tiering and lifecycle controls
- Questionnaire automation and reusable assessment templates
- Evidence collection workflows with tracking and audit trails
- Remediation management with owners and deadlines
- Risk scoring models and reporting dashboards
- Approval workflows and role-based access patterns
- Configurable workflows for different vendor categories
Pros
- Strong lifecycle structure and consistent assessment workflows
- Good fit for teams formalizing vendor risk programs
Cons
- Setup and configuration can require planning
- Some integrations may need customization depending on environment
Platforms / Deployment
- Web
- Cloud
Security & Compliance
- SSO/SAML, MFA, encryption, audit logs, RBAC: Not publicly stated
- SOC 2, ISO 27001, GDPR, HIPAA: Not publicly stated
Integrations & Ecosystem
Designed to connect with governance workflows and upstream vendor processes.
- GRC integrations: Varies / N/A
- Ticketing integrations: Varies / N/A
- Import/export and API workflows: Varies / N/A
- Notifications and collaboration tools: Varies / N/A
Support & Community
Implementation and support models vary by plan; documentation and onboarding depend on contract level.
2) OneTrust Vendor Risk Management
A vendor risk solution often used where privacy, data governance, and compliance workflows are important. Helpful for teams that want vendor assessments tied to privacy and policy requirements.
Key Features
- Vendor onboarding and risk tiering workflows
- Assessment questionnaires and evidence collection
- Privacy and data handling assessment workflows
- Remediation tracking and approval routing
- Reporting for audit and compliance visibility
- Policy alignment and documentation tracking
- Workflow customization for vendor categories
Pros
- Strong fit for privacy-driven vendor governance
- Helpful for organizations aligning vendor risk with broader compliance programs
Cons
- Complexity can increase as modules expand
- Licensing and packaging may be harder to compare across teams
Platforms / Deployment
- Web
- Cloud
Security & Compliance
- SSO/SAML, MFA, encryption, audit logs, RBAC: Not publicly stated
- SOC 2, ISO 27001, GDPR, HIPAA: Not publicly stated
Integrations & Ecosystem
Often used alongside privacy and compliance workflows with shared reporting needs.
- GRC and compliance integrations: Varies / N/A
- Workflow and ticketing handoffs: Varies / N/A
- APIs and connectors: Varies / N/A
- Data governance alignment: Varies / N/A
Support & Community
Support tiers vary; onboarding resources depend on plan and deployment scope.
3) Archer Third Party Risk Management
A well-known enterprise solution for structured governance workflows, including vendor risk. Best for large organizations needing strong controls, reporting, and enterprise governance alignment.
Key Features
- Vendor lifecycle tracking and structured workflows
- Configurable risk scoring models and control libraries
- Assessment workflows with evidence and approvals
- Issue management and remediation tracking
- Audit-oriented reporting and dashboards
- Role-based access and structured governance patterns
- Alignment with broader enterprise risk workflows
Pros
- Strong governance and enterprise reporting depth
- Highly configurable for complex enterprise requirements
Cons
- Implementation can be heavy and time-consuming
- Often more expensive and complex for smaller teams
Platforms / Deployment
- Web
- Cloud / Self-hosted / Hybrid (Varies / N/A)
Security & Compliance
- SSO/SAML, MFA, encryption, audit logs, RBAC: Not publicly stated
- SOC 2, ISO 27001, GDPR, HIPAA: Not publicly stated
Integrations & Ecosystem
Often connects into enterprise risk ecosystems and compliance tooling.
- GRC ecosystem alignment: Varies / N/A
- Ticketing and workflow integrations: Varies / N/A
- Data import/export and APIs: Varies / N/A
- Audit workflow integrations: Varies / N/A
Support & Community
Enterprise support options vary by agreement; best results typically come with structured implementation support.
4) ServiceNow Vendor Risk Management
A vendor risk capability often used by organizations already using a ServiceNow ecosystem. Best for teams that want vendor risk tied to enterprise workflows and operational processes.
Key Features
- Vendor onboarding and assessment workflows
- Task-based remediation and ticket-driven follow-ups
- Integration with IT workflows and approvals
- Centralized risk register and reporting views
- Workflow automation for evidence requests
- Configurable scoring and vendor tiering
- Audit-friendly reporting and traceability
Pros
- Strong workflow automation for organizations already standardized on ServiceNow
- Good operational integration with remediation and task management
Cons
- Best value depends on existing platform adoption
- Configuration may require platform expertise
Platforms / Deployment
- Web
- Cloud
Security & Compliance
- SSO/SAML, MFA, encryption, audit logs, RBAC: Not publicly stated
- SOC 2, ISO 27001, GDPR, HIPAA: Not publicly stated
Integrations & Ecosystem
Strong fit when vendor risk needs to connect with IT operations and governance workflows.
- Ticketing and workflow automation: Varies / N/A
- GRC alignment: Varies / N/A
- APIs and connectors: Varies / N/A
- Procurement and vendor data sources: Varies / N/A
Support & Community
Large ecosystem of implementation partners; support tiers vary by plan.
5) MetricStream Third-Party Risk Management
A governance-focused platform used for risk, compliance, and vendor oversight. Best for teams wanting strong reporting and structured risk governance.
Key Features
- Vendor inventory, tiering, and lifecycle management
- Assessment workflows with evidence and approvals
- Risk scoring frameworks and control mapping
- Remediation and issue management workflows
- Audit and compliance reporting dashboards
- Configurable workflows for different vendor types
- Standardization across risk and compliance teams
Pros
- Strong reporting and governance structure
- Useful for organizations with mature GRC programs
Cons
- Implementation effort can be significant
- Complexity may be higher than needed for small programs
Platforms / Deployment
- Web
- Cloud / Self-hosted / Hybrid (Varies / N/A)
Security & Compliance
- SSO/SAML, MFA, encryption, audit logs, RBAC: Not publicly stated
- SOC 2, ISO 27001, GDPR, HIPAA: Not publicly stated
Integrations & Ecosystem
Often connects with compliance tooling and enterprise risk processes.
- GRC integrations and connectors: Varies / N/A
- Workflow and ticketing integrations: Varies / N/A
- Import/export and APIs: Varies / N/A
- Reporting ecosystems: Varies / N/A
Support & Community
Enterprise support and implementation options vary; structured onboarding is typically recommended.
6) NAVEX Third Party Risk Management
A platform often used for ethics, compliance, and risk programs, including vendor and third-party risk workflows. Good for teams linking vendor risk to broader compliance initiatives.
Key Features
- Third-party onboarding and due diligence workflows
- Assessments and documentation tracking
- Policy and compliance alignment for vendors
- Remediation tasks and follow-up workflows
- Reporting for audits and compliance reviews
- Configurable approval routing
- Centralized vendor risk documentation
Pros
- Good fit for compliance-driven vendor governance
- Helps standardize third-party diligence across departments
Cons
- Cyber risk depth may vary depending on needs
- Some advanced integrations may require additional setup
Platforms / Deployment
- Web
- Cloud
Security & Compliance
- SSO/SAML, MFA, encryption, audit logs, RBAC: Not publicly stated
- SOC 2, ISO 27001, GDPR, HIPAA: Not publicly stated
Integrations & Ecosystem
Works best when paired with compliance workflows and internal approval processes.
- Compliance and case management alignment: Varies / N/A
- APIs and integrations: Varies / N/A
- Workflow and notifications: Varies / N/A
- Vendor data imports: Varies / N/A
Support & Community
Support varies by plan; many teams rely on implementation guidance for setup.
7) Prevalent Third-Party Risk Management
A third-party risk platform that emphasizes assessment automation and continuous monitoring signals. Useful for teams managing many vendors and needing ongoing oversight.
Key Features
- Vendor intake and assessment workflows
- Questionnaire automation and evidence collection
- Continuous monitoring signals for vendor risk changes
- Remediation tracking and follow-up workflows
- Reporting dashboards for risk visibility
- Vendor tiering and program standardization
- Workflow automation for recurring assessments
Pros
- Strong focus on continuous monitoring and scale
- Helpful for reducing manual vendor follow-ups
Cons
- Scoring and signal interpretation require internal governance
- Coverage quality can vary by vendor type and region
Platforms / Deployment
- Web
- Cloud
Security & Compliance
- SSO/SAML, MFA, encryption, audit logs, RBAC: Not publicly stated
- SOC 2, ISO 27001, GDPR, HIPAA: Not publicly stated
Integrations & Ecosystem
Designed to support vendor monitoring workflows and reporting across risk teams.
- GRC and workflow integrations: Varies / N/A
- Ticketing and remediation handoffs: Varies / N/A
- API availability: Varies / N/A
- Data imports and exports: Varies / N/A
Support & Community
Support depends on plan; onboarding is often structured for large vendor programs.
8) Riskonnect Third Party Risk Management
A risk management platform that supports third-party risk programs, reporting, and governance workflows. Suitable for organizations that want vendor risk as part of broader operational risk oversight.
Key Features
- Vendor inventory, tiering, and assessment workflows
- Risk scoring and reporting dashboards
- Remediation and action tracking
- Approval workflows and governance controls
- Program analytics and executive reporting
- Configurable workflows and questionnaires
- Centralized documentation for audits
Pros
- Good fit for linking vendor risk to operational risk reporting
- Strong analytics and governance approach
Cons
- May require configuration effort to match internal risk models
- Some cyber-specific depth may depend on integrations
Platforms / Deployment
- Web
- Cloud
Security & Compliance
- SSO/SAML, MFA, encryption, audit logs, RBAC: Not publicly stated
- SOC 2, ISO 27001, GDPR, HIPAA: Not publicly stated
Integrations & Ecosystem
Often used as part of a wider risk ecosystem with shared reporting.
- GRC and operational risk integrations: Varies / N/A
- Workflow and ticketing tools: Varies / N/A
- APIs and data connectors: Varies / N/A
- Reporting exports: Varies / N/A
Support & Community
Support and onboarding vary by plan; implementation partners may be used for customization.
9) LogicGate Risk Cloud
A workflow-driven risk platform used for building configurable risk processes, including third-party risk. Good for teams that want flexibility without heavy custom development.
Key Features
- Configurable vendor risk workflows and intake forms
- Questionnaire automation and evidence tracking
- Remediation workflows with task ownership and escalation
- Risk scoring frameworks and reporting dashboards
- Approvals and role-based access patterns
- Cross-team collaboration workflows
- Flexible design for different vendor categories
Pros
- Flexible workflow builder approach for tailored programs
- Useful for teams that want to evolve processes over time
Cons
- Requires good internal process design to avoid workflow sprawl
- Some out-of-the-box content may need tailoring
Platforms / Deployment
- Web
- Cloud
Security & Compliance
- SSO/SAML, MFA, encryption, audit logs, RBAC: Not publicly stated
- SOC 2, ISO 27001, GDPR, HIPAA: Not publicly stated
Integrations & Ecosystem
Designed to fit into existing enterprise workflows through connectors and configurable processes.
- GRC integrations: Varies / N/A
- Ticketing and collaboration: Varies / N/A
- API and automation: Varies / N/A
- Data import/export: Varies / N/A
Support & Community
Support tiers vary; many teams benefit from structured onboarding to build consistent workflows.
10) SecurityScorecard Vendor Risk Management
A platform that emphasizes external cyber risk signals and vendor security visibility. Often used to prioritize vendor security conversations and track changes over time.
Key Features
- External security signal monitoring for vendors (coverage varies)
- Vendor inventory and cyber risk views
- Risk alerts and change tracking over time
- Reporting for vendor security posture discussions
- Workflows to support vendor outreach and remediation requests
- Portfolio-level visibility for many vendors
- Useful for prioritizing which vendors need deeper review
Pros
- Strong for continuous cyber posture visibility at scale
- Helpful for prioritization when vendor counts are high
Cons
- Not a full replacement for questionnaires and internal evidence collection
- Signal accuracy and coverage can vary by vendor footprint
Platforms / Deployment
- Web
- Cloud
Security & Compliance
- SSO/SAML, MFA, encryption, audit logs, RBAC: Not publicly stated
- SOC 2, ISO 27001, GDPR, HIPAA: Not publicly stated
Integrations & Ecosystem
Often used alongside broader TPRM workflows and GRC systems.
- GRC integration patterns: Varies / N/A
- Ticketing and workflow handoffs: Varies / N/A
- API integrations: Varies / N/A
- Reporting exports: Varies / N/A
Support & Community
Support varies by plan; teams typically combine it with internal review processes for best results.
Comparison Table (Top 10)
| Tool Name | Best For | Platform(s) Supported | Deployment (Cloud/Self-hosted/Hybrid) | Standout Feature | Public Rating |
|---|---|---|---|---|---|
| ProcessUnity | Structured vendor assessments and remediation workflows | Web | Cloud | End-to-end vendor lifecycle workflows | N/A |
| OneTrust Vendor Risk Management | Privacy-aligned vendor risk and compliance workflows | Web | Cloud | Strong privacy and data handling governance | N/A |
| Archer Third Party Risk Management | Enterprise-grade governance and configurable controls | Web | Cloud / Self-hosted / Hybrid (Varies / N/A) | Deep enterprise configuration options | N/A |
| ServiceNow Vendor Risk Management | Vendor risk tied to operational workflows and tickets | Web | Cloud | Task-based remediation workflows | N/A |
| MetricStream Third-Party Risk Management | Mature GRC programs with strong reporting needs | Web | Cloud / Self-hosted / Hybrid (Varies / N/A) | Governance-focused dashboards | N/A |
| NAVEX Third Party Risk Management | Compliance-driven vendor due diligence programs | Web | Cloud | Third-party compliance alignment | N/A |
| Prevalent Third-Party Risk Management | Scale with assessment automation and monitoring signals | Web | Cloud | Continuous monitoring plus assessments | N/A |
| Riskonnect Third Party Risk Management | Vendor risk within broader operational risk oversight | Web | Cloud | Analytics and operational risk alignment | N/A |
| LogicGate Risk Cloud | Flexible workflow-driven vendor risk programs | Web | Cloud | Configurable workflows without heavy development | N/A |
| SecurityScorecard Vendor Risk Management | External cyber posture monitoring for vendor portfolios | Web | Cloud | Cyber risk signals for vendor prioritization | N/A |
Evaluation & Scoring of Third-Party Risk Management Tools
Weights: Core features 25%, Ease 15%, Integrations 15%, Security 10%, Performance 10%, Support 10%, Value 15%.
| Tool Name | Core (25%) | Ease (15%) | Integrations (15%) | Security (10%) | Performance (10%) | Support (10%) | Value (15%) | Weighted Total (0–10) |
|---|---|---|---|---|---|---|---|---|
| ProcessUnity | 8.5 | 7.5 | 7.5 | 6.5 | 7.5 | 7.5 | 7.0 | 7.63 |
| OneTrust Vendor Risk Management | 8.0 | 7.0 | 7.5 | 6.5 | 7.5 | 7.0 | 6.5 | 7.29 |
| Archer Third Party Risk Management | 9.0 | 6.0 | 8.0 | 7.0 | 8.0 | 7.5 | 6.0 | 7.63 |
| ServiceNow Vendor Risk Management | 8.0 | 7.5 | 8.5 | 7.0 | 8.0 | 8.0 | 6.5 | 7.74 |
| MetricStream Third-Party Risk Management | 8.5 | 6.5 | 8.0 | 7.0 | 8.0 | 7.5 | 6.0 | 7.48 |
| NAVEX Third Party Risk Management | 7.5 | 7.5 | 7.0 | 6.5 | 7.5 | 7.0 | 6.5 | 7.17 |
| Prevalent Third-Party Risk Management | 8.0 | 7.0 | 7.5 | 6.5 | 7.5 | 7.5 | 6.5 | 7.32 |
| Riskonnect Third Party Risk Management | 7.5 | 7.0 | 7.5 | 6.5 | 7.5 | 7.0 | 6.5 | 7.19 |
| LogicGate Risk Cloud | 7.5 | 7.5 | 7.5 | 6.5 | 7.5 | 7.5 | 7.0 | 7.43 |
| SecurityScorecard Vendor Risk Management | 7.0 | 7.5 | 7.0 | 6.5 | 8.0 | 7.0 | 6.5 | 7.17 |
How to interpret the scores:
- Scores compare tools only within this list, not the entire market.
- Higher totals usually indicate broader coverage across common TPRM needs.
- If you are compliance-heavy, prioritize workflow, evidence, and reporting depth.
- If you are cyber-heavy, prioritize monitoring signals and vendor security visibility.
- Always validate with a pilot using your real vendor categories and governance rules.
Which Third-Party Risk Management Tool Is Right for You?
Solo / Freelancer
Most solo users do not need a full TPRM platform unless they are consultants running vendor assessments for clients. If you do need one, focus on ease, templates, and quick reporting. LogicGate Risk Cloud may suit workflow-heavy consulting approaches, while SecurityScorecard Vendor Risk Management can help with fast vendor cyber posture snapshots as an input.
SMB
SMBs need a tool that reduces manual follow-ups and standardizes onboarding without heavy implementation. ProcessUnity, Prevalent Third-Party Risk Management, and LogicGate Risk Cloud are practical starting points depending on whether you want stronger workflows or stronger monitoring signals. If privacy requirements drive your program, OneTrust Vendor Risk Management can be attractive.
Mid-Market
Mid-market teams often need both structured assessments and continuous monitoring signals. Prevalent Third-Party Risk Management plus a consistent evidence workflow can reduce the burden on a small risk team. ServiceNow Vendor Risk Management is strong when remediation needs to flow directly into operational ticketing and approvals. Riskonnect Third Party Risk Management can be useful when vendor risk must roll up into operational risk reporting.
Enterprise
Enterprises typically require strict governance, configurable scoring, audit readiness, and cross-team visibility. Archer Third Party Risk Management and MetricStream Third-Party Risk Management are commonly chosen when deep governance and reporting are priorities. ServiceNow Vendor Risk Management is strong when workflow execution and remediation must be tied to IT operations and internal service processes.
Budget vs Premium
Budget programs should focus on reducing manual work and standardizing assessments first, then add monitoring later. Premium programs usually combine workflow depth, integrations, continuous monitoring, and executive reporting. The “premium” choice is not always the most expensive tool, but the one that best reduces operational friction and audit risk.
Feature Depth vs Ease of Use
If you need quick rollout, prioritize tools with clean assessment templates, minimal configuration, and intuitive workflows. If you need deep control mapping, complex tiering, and enterprise-level governance, choose a tool built for configuration and reporting depth, even if the rollout is heavier.
Integrations & Scalability
If procurement, GRC, IAM, ticketing, and contract systems are already established, integrations become a deciding factor. Choose tools that can automate vendor intake, assignment, evidence reminders, remediation tasks, and reporting exports without constant manual effort.
Security & Compliance Needs
If you handle sensitive data or regulated environments, focus on evidence collection, audit trails, access control patterns, and repeatable assessments. When security certifications are not publicly stated, treat them as unknown and validate through vendor security documentation and your internal review process.
Frequently Asked Questions (FAQs)
1. What does a TPRM tool actually replace in day-to-day work?
It replaces scattered emails, spreadsheets, and inconsistent vendor checklists by standardizing assessments, evidence requests, follow-ups, and remediation tracking in one workflow.
2. How do these tools help during audits?
They centralize vendor evidence, approvals, risk decisions, and remediation status so audit teams can see a clean record of what was reviewed and when.
3. Do I still need questionnaires if I have external cyber risk signals?
Yes in most cases. External signals help prioritize, but questionnaires and evidence are usually needed to confirm controls, contracts, and data handling practices.
4. What is vendor tiering and why is it important?
Tiering classifies vendors by criticality and risk so your team can apply deeper assessments to high-risk vendors and lighter reviews to low-risk vendors.
5. How long does implementation typically take?
It varies by program maturity and integrations. Teams with clear processes and vendor categories generally move faster than teams designing the program from scratch.
6. What are the most common mistakes in TPRM programs?
Asking every vendor the same deep questionnaire, failing to define tiering rules, not tracking remediation ownership, and not setting reassessment timelines.
7. How do these tools handle fourth-party risk?
Some support documentation and dependency tracking, but coverage varies. Many teams still need process controls to ensure vendors disclose critical subcontractors.
8. Can these tools integrate with ticketing and workflow systems?
Many do, but integration depth varies by tool and environment. The key is whether remediation tasks can flow cleanly into your existing work system.
9. What matters more: scoring models or workflow execution?
Workflow execution usually matters more day-to-day because it prevents missed follow-ups and incomplete evidence. Scoring is useful, but only if it drives action.
10. How do I choose between an enterprise GRC approach and a lighter platform?
Choose enterprise GRC-style tools when you need deep governance, control mapping, and broad risk reporting. Choose lighter platforms when speed, usability, and quick standardization are the priority.
Conclusion
Third-party risk is not just a compliance checkbox; it is an operational reality that can impact availability, data protection, and customer trust. The best tool depends on how your organization runs vendor onboarding, how often you reassess, and how tightly you need vendor remediation connected to daily work. Workflow-driven platforms help you standardize questionnaires, collect evidence, and track remediation without losing visibility. Monitoring-focused platforms help you prioritize which vendors need immediate attention when risk signals change. The smartest next step is to shortlist two or three tools, run a pilot using your real vendor tiers and evidence requirements, test integrations with ticketing and procurement, and confirm the reporting you need for audits and leadership.